A sometimes overlooked 2024 update delivers easier access to protected messages delivered to shared mailboxes. Instead of direct assignment of Full Access to user mailboxes, access can be controlled through membership of a mail-enabled security group. It’s a small but very nice change, just like any update that eases the life of tenant administrators.
An October 14 report says that Office 365 Message Encryption shouldn’t be used because its encryption scheme might reveal email content. Well, that might be the case if an attacker can hijack connectivity from Office 365 to another email service. But the relatively low levels of OME usage and the difficulty of acquiring enough email to understand message structure makes this a less than practical attack in the wild.
Microsoft 365 Data Loss Prevention (DLP) policies have wide-ranging capabilities when it comes to rules and exceptions. One exception covers the various types of encrypted email that can pass through the Exchange Online transport pipeline. As it happens, three message types are supported, but who could have guessed that permission controlled means rights management?
Office 365 Message Encryption protection is not available for messages sent to dynamic distribution groups. It’s all to do with rights management licensing. However, if you need to protect messages sent to dynamic distribution groups, for instance to make sure that confidential messages are inaccessible to external recipients use a sensitivity label instead and assign the special tenant-wide permission to recipients.
Office 365 Message Encryption (OME) allows OWA users to revoke some messages after they are delivered to recipients. But if the message goes to Office 365 or Outlook.com, you can’t revoke it. And there’s the slight matter of needing an Office 365 E5 license too. Even so, it’s still nice to be able to revoke messages if they go to the wrong place.
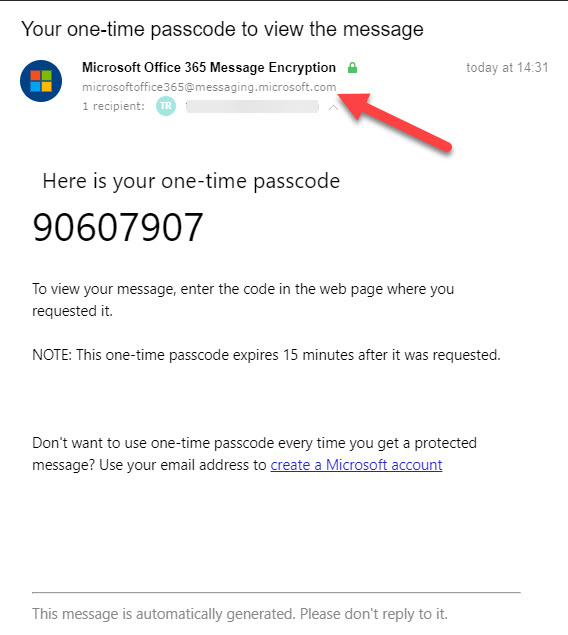
Microsoft is releasing some updates to Office 365 Message Encryption (OME) in January. The detail in the announcement wasn’t great, so we plunged in to find out what’s happening. THe bottom line is that OME will use tenant domains to send email so that anti-spam filters will consider the messages to be authentic.