Purview Data Loss Prevention (DLP) rule checks can happen client-side and server-side. This change updates the Exchange Online organization configuration to instruct OWA to stop using Exchange Online to detect potential DLP rule violations before users send email. Instead, OWA will use the workload-neutral Data Classification Services (DCS). Using a workload-neutral service comes with some consequences in terms of OWA being unable to evaluate Exchange-specific predicates.
A new action for the DLP Policy for Copilot allows Microsoft 365 tenants to block Copilot from performing (Bing) web searches if a prompt contains sensitive information types. The new action allows Copilot to continue to process prompts using Microsoft 365 content (if the user has a Microsoft 365 Copilot license) while stopping potentially sensitive data being sent to Bing.
Microsoft has enhanced the DLP policy for Copilot to cover Office files held in any storage location instead of only Microsoft 365 locations like SharePoint Online and OneDrive for Business. The change is made in the Office augmentation loop, a little-known internal component that coordinates use of connected experiences by apps. Extending the DLP policy to cover all locations makes perfect sense.
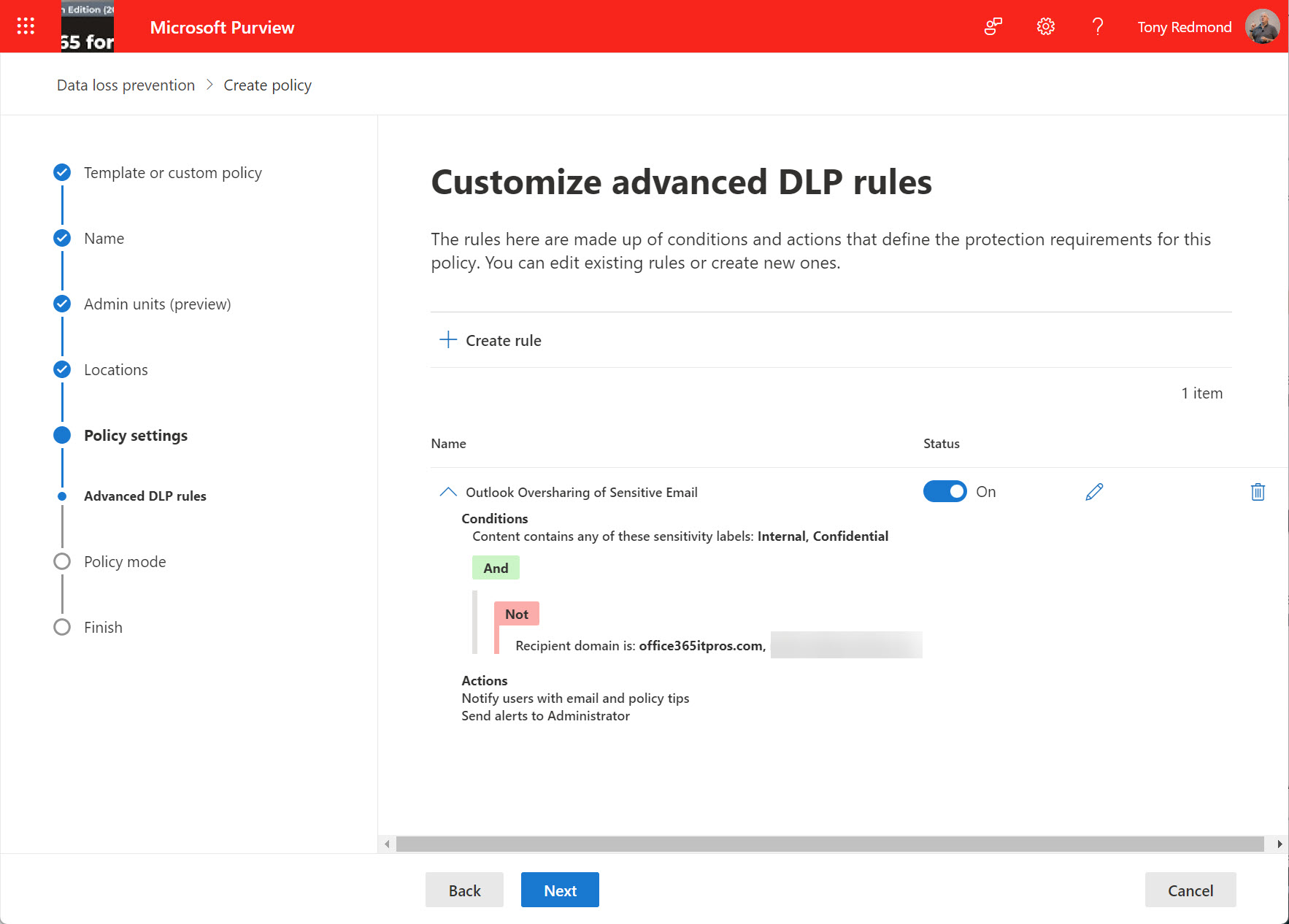
The news that the new Outlook client will support custom oversharing dialogs for DLP policies might not seem very interesting, but it provoked me to look more closely into how to build and deploy custom oversharing dialogs. All it takes is some well-structured JSON and an update to DLP rules, and the classic and Monarch Outlook clients should display custom tenant instructions to anyone who violates DLP rules.
MC1169572 announces that administrators can add classifications to DLP alerts to help with reporting. But how do you report DLP alerts? As it turns out, it’s relatively easy to retrieve DLP alerts via the Microsoft Graph Security API. Using the Get-MgSecurityAlertV2 cmdlet from the Microsoft Graph PowerShell SDK makes it even easier to find and report the data.
A new DLP policy for Copilot prompts monitors blocked sensitive information types like credit card numbers to stop their use in Copilot prompts. The new policy can’t be combined with the existing DLP policy for Copilot, which checks for files with specific sensitivity labels to prevent Copilot from using their content in its responses. But that’s OK because the two policies do very different work.
DLP diagnostics were announced in October 2024, and it’s taken quite a while for Microsoft to make the four DLP diagnostic tests available. In truth, none of the tests are earthshattering and the kind of checking done by the tests could be performed quite easily by an experienced tenant administrator who knows the DLP solution. But those administrators are unlikely to be the target audience for these tests.
First introduced in March 2025 to block access to sensitive documents by BizChat, Microsoft has extended the DLP policy for Copilot to cover the web and desktop versions of the Office apps (Word, Excel, and PowerPoint). The implementation works but could confuse users. It might be better if Microsoft simply removes all traces of Copilot when working with files subject to the DLP policy.
A cloud policy setting enables a delay for evaluating message content and allows Outlook DLP Policy Tips to be displayed after detection of a policy violation. The setting works by pausing message sends until Outlook has had time to check the content for DLP policy violations Pop-up messages inform users about the pause and the result of the check.
An update for Microsoft 365 Data Loss Prevention policies supports the configuration of oversharing popups for Outlook shown when a user composes email with specified sensitivity labels for either the message or any attachment. The idea is that the popup (a policy tip) helps the user to understand the problem and why they are violating a DLP policy so that they can address the problem before attempting to send the message.
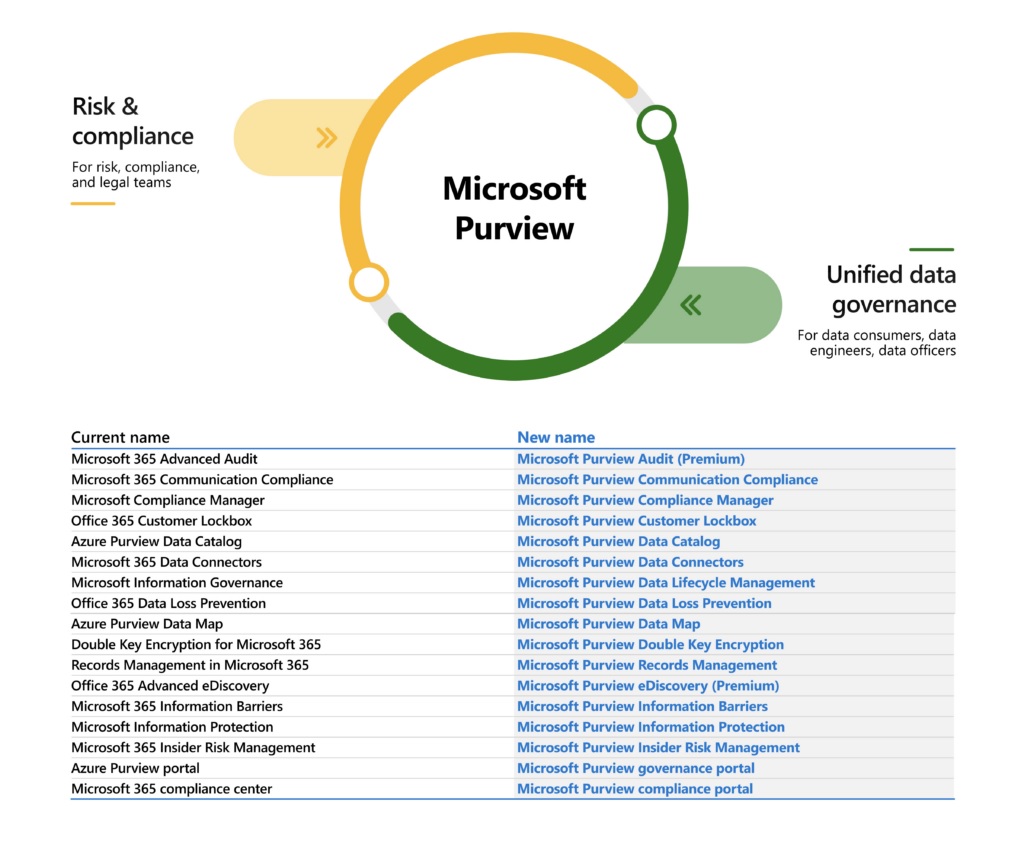
Microsoft marketing folks are no doubt very pleased with their latest branding success in introducing the Microsoft Purview suite. Others aren’t quite so thrilled, especially anyone who writes about technology and now has to update text to match the desires of the brand police. On the upside, there’s some good new functionality coming for different products in the suite.
Microsoft 365 Data Loss Prevention (DLP) policies have wide-ranging capabilities when it comes to rules and exceptions. One exception covers the various types of encrypted email that can pass through the Exchange Online transport pipeline. As it happens, three message types are supported, but who could have guessed that permission controlled means rights management?
To make Microsoft 365 DLP policies work like Exchange transport-rule based DLP, a January change will switch evaluation of sender conditions away from envelope information to message headers. Although this change might seem to be something beloved of email geeks, it’s actually an important update for organizations who want to move away from ETR-based DLP to Microsoft 365 DLP policies.
Teams meeting recordings can contain a lot of confidential information. It’s a quick and easy task to create a Data Loss Prevention (DLP) policy to stop people sharing these files externally, In this post, we show just how simple the required policy is, and just how effective it is at stopping external sharing.
Microsoft plans to surface recommendations to use communications compliance policies as part of its DLP workflow. That sounds acceptable, but it’s the second example of how Microsoft pushes high-priced premium features to Office 365 tenants through DLP. Apart from the undesirability of pushing features to customers through software, communications compliance is not something that you implement on a whim, so why does Microsoft think this is a good idea?
Microsoft 365 organizations which use Teams but don’t have a Teams DLP policy will see a Compliance Center widget recommending the creation of a DLP policy. Sounds good, and the policy covers the most common sensitive data types that people worry about. The downside is that Teams demands Office 365 E5 licenses for DLP policies. You might not know that, but you will if you accept the recommendation.
Teams Data Loss Prevention (DLP) policies help to stop users sharing confidential information through chats and channel conversations. A recent update means that accounts to be included or excluded in DLP policies can be specified using distribution lists or mail-enabled security groups. While this doesn’t sound very exciting, it is if you need to deploy DLP policies to targeted sets of Teams users.
Feb 24 2021 Update: The picker used for OneDrive for Business accounts will support distribution lists and security groups in March.
Microsoft has released a set of new sensitive information types, used to locate sensitive data by Microsoft 365 DLP policies. Many are country-specific versions of previous generic types (like passports or identity cards). The recommendation is to consider upgrading DLP policies to use the new types to get better (more accurate) matching.
Microsoft has made Endpoint DLP generally available. Leveraging Windows 10 workstations and the Edge browser, Endpoint DLP sends signals for evaluation to detect possible violations. The solution requires Microsoft 365 licenses and only supports Windows, so it’s not for every tenant. But those who have Microsoft 365 licenses will find this an attractive solution.
When you need to block external access to your most sensitive documents, Office 365 Data Loss Prevention policies and sensitivity labels combine to find and protect the documents. A really simple policy is enough to detect and block external access, and is covered by Office 365 E3 licenses. If you have E5 licenses, you can consider auto-label policies to find and protect sensitive documents at scale.
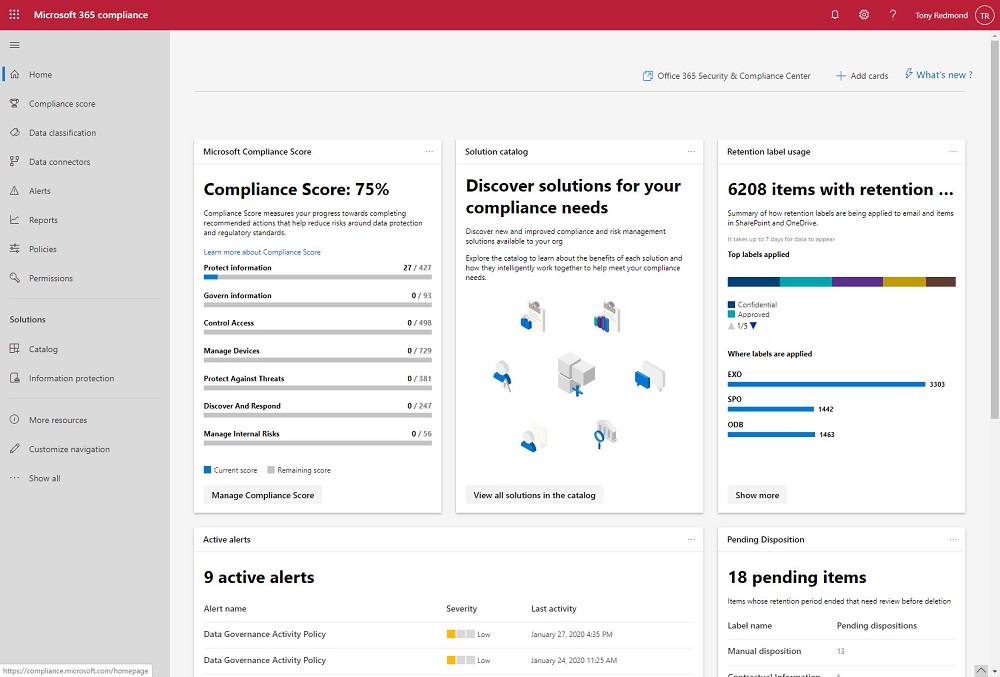
The Microsoft 365 Compliance and Security centers are roling out to Office 365 tenants where they’ll replace the old Security and Compliance Center over time. The new centers look fresher than the SCC, but looks can deceive and it’s much more important that the functionality exposed in the new portals work reliably all the time.
Office 365 supervision policies can now make use of artificial intelligence and machine learning to detect offensive language in email and Teams communications. The data model covers a wide range of problematic language, but only in English. You can go ahead and cheerfully continue to swear in French, German, and other languages with no danger of being detected by policy.
In a sign of how automation based on signals gathered by Office 365 will emerge to help administrators do a better job, the preview of the new Admin Center offered to create a DLP policy to protect some sensitive information that I had clearly overlooked. Well-intended as the portal was, its efforts to create the new policy failed. That’s not really important – it’s the glimpse into the future which is.
Office 365 offers different ways to apply encryption to important messages. When those messages hold sensitive data known to Office 365, like credit cards or passport numbers, we can define a transport rule or DLP policy to protect outbound email automatically. And while you can define rules and policies through the GUI, PowerShell is available too.
Microsoft thoughtfully provided Office 365 tenants with a Data Loss Prevention template for GDPR personal data. The only problem is that the rules in the template were too sensitive and started to block email.