A recent discussion about reporting changes to Microsoft 365 groups provoked the question about how to report distribution list changes. The answer is that the same structure can be taken in a PowerShell script to fetch and report data, including the audit records containing the information about the changes, but the actual code is very different. Distribution lists Exchange Online objects and not Entra ID groups…
Some days ago, I wrote about creating a new employee welcome email with ICS files for corporate events. As it turns out, Inviting employees to attend those events by updating the participant list with PowerShell is an easier and better approach. This article explains how to find calendar events, update participant lists, and update events with the Microsoft Graph PowerShell SDK.
ICS files are a useful method to send information about calendar events between different IT systems. This article discusses creating ICS files for Teams Online meetings as part of a project to send welcome messages to new employees that contain information about upcoming corporate events that the new people might like to attend. Suffice to say that formatting the ICS files to Outlook’s satisfaction takes some effort.
A PowerShell script that sends details of open tasks to users for follow up is a good thing. Storing open task statistics in a list for analysis of open task burndown over time is even better. This article describes how to update the script that sends email about open tasks to add the code necessary to use a list in a SharePoint Online site to store details about open tasks.
Version 24 of the Automating Microsoft 365 with PowerShell eBook is now available for current subscribers to download. The updated PDF and EPUB files are available from Gumroad.com. The paperback edition is also updated. In other news, a new version of the Microsoft Graph PowerShell SDK is available, and Microsoft has created a problem of their own making by announcing the retirement of the AutoRest utility.
Understanding what Graph permissions are required by apps can be challenging. In this article we discuss how the Group.Read.All and GroupMember.Real.All permissions work and why you should choose one permission over the other and respect the principle of least permission when it comes to assigning Graph permissions to your apps and PowerShell scripts.
This article discusses how to list files archived using the SharePoint Online file-level archiving feature. We also discuss how to archive and unarchive files using the Microsoft Graph PowerShell SDK and Graph API requests. As it turns out, the drives API is the best way to find (list) archived or unarchived files, while archiving files that haven’t been modified in a while is easy with a few lines of PowerShell.
In 2024, I wrote a script explaining how to report details of Teams online meetings, including participants. Now someone wants to report single-user meetings. Their reason is that company management believe that some remote workers schedule online meetings that only they attend with the intention of appearing active if anyone checks. It’s an odd ask, but we can do the job with PowerShell.
The additionalProperties property is available for many Microsoft Graph PowerShell SDK cmdlets. In this article, we explain the function of the additionalProperties property and how it functions in holding output for Microsoft Graph PowerShell SDK cmdlets. It’s all because of the lack of strongly typed properties, or so the AutoRest process would have us believe.
The May 2026 update for the Automating Microsoft 365 with PowerShell eBook is available. Current subscribers can download new PDF and EPUB files. The paperback edition of the book (available on demand from Amazon) is also updated. With over 400 pages of content, including twice that number of practical examples of using PowerShell to interact with Microsoft 365, the book is going from strength to strength.
A reader wanted a weekly incomplete task digest to send details of Planner tasks to people with outstanding work to do. We used PowerShell to scan for incomplete tasks for people who are members of a group, perform some analysis on the data, and create and send email. Despite some deficiencies in the Planner Graph API, the code is pretty straightforward.
The Copilot Retrieval API is a Microsoft Graph API that apps can use to search Microsoft 365 locations to find information to ground user prompts. Grounding means that the apps use the information found by Copilot to add context to the queries they submit to a generative AI engine for processing. Although I don’t have an immediate purpose for the API, it provides a nice insight into how grounding works.
Entra ID uses an eventually consistent multi-region database architecture. PowerShell code that fetches and updates Entra ID objects needs to interact with the database in the most efficient manner. This article illustrates some guidance from Microsoft engineering with examples from the Microsoft Graph PowerShell SDK. I’m sure your scripts already use these techniques, but if not, we have some helpful pointers.
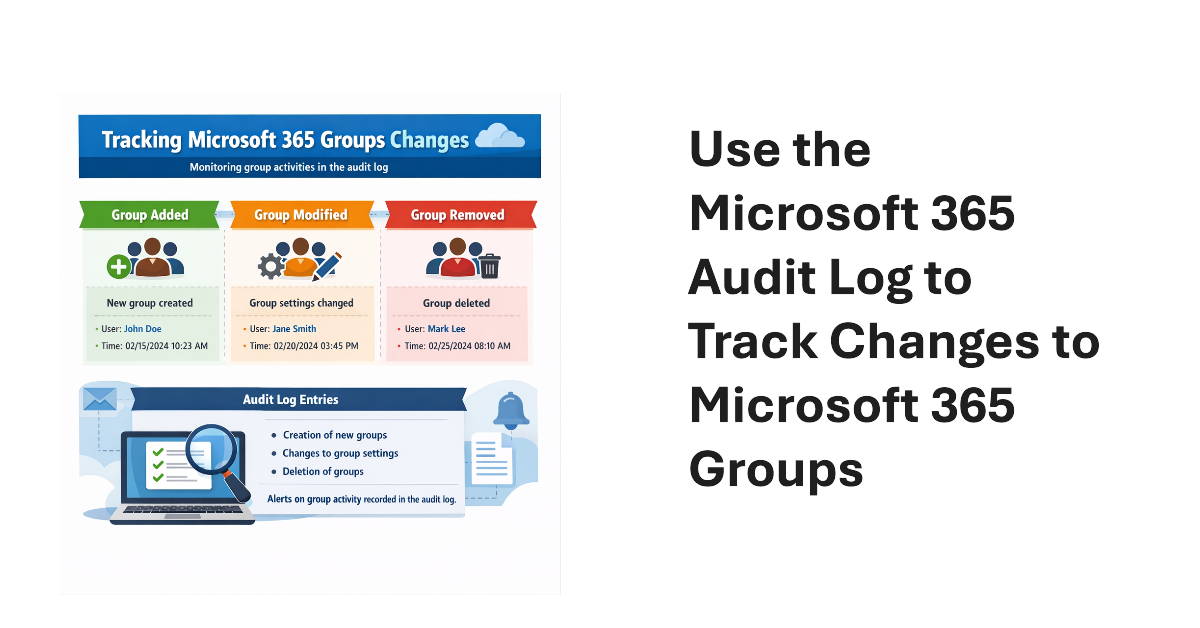
An old PowerShell script tracked changes to Office 365 Groups. The techniques from 2016 wouldn’t be used today because features like the unified audit log didn’t exist then. We show what’s possible now by creating a new version of a Microsoft 365 Groups Change Report script to track additions, deletions, and changes for Microsoft 365 groups in a tenant.
This article discusses the use of restricted site creation for third-party Entra ID apps. The feature has an allow or deny list to identify apps that can create new SharePoint Online sites. Controlling the set of apps that can create new sites contributes to limiting site sprawl and makes sure that every site has a real function. First-party apps like Teams are unaffected.
The April 2026 update for the Automating Microsoft 365 with PowerShell eBook is now available for subscribers to download. Refreshed EPUB and PDF files can be downloaded from Gumroad.com. The Kindle and paperback editions are also updated. This month we reflect on V2.36.1 of the Microsoft Graph PowerShell SDK and why so little has changed in this important component.
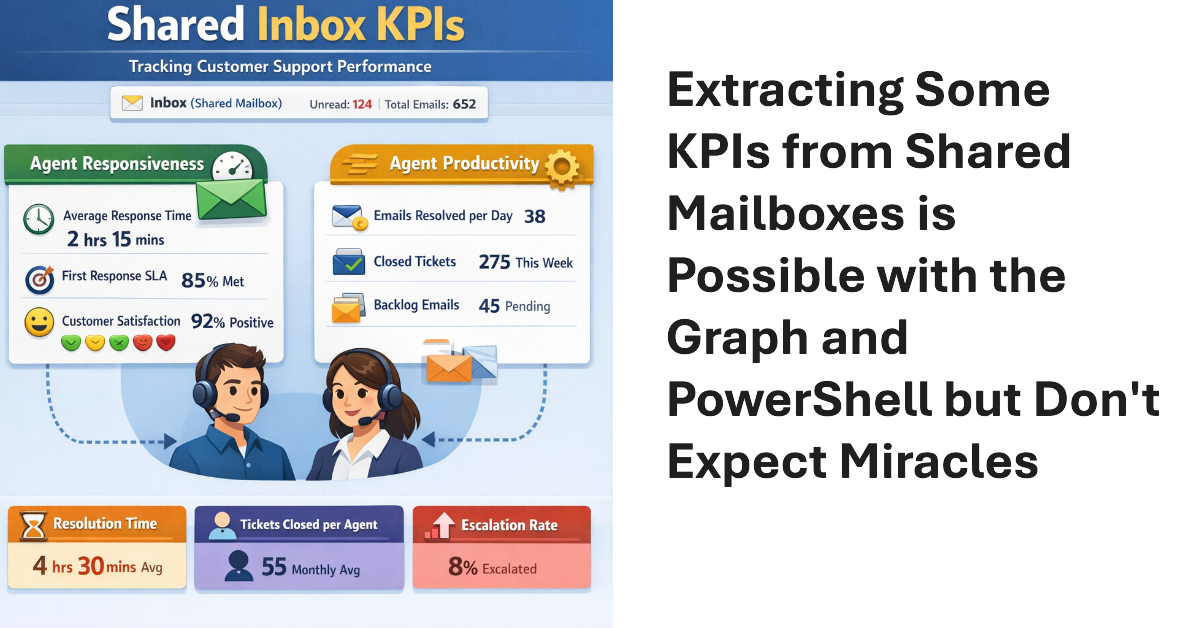
Shared mailboxes are not CRM systems. However, many Microsoft 365 tenants use shared mailboxes to handle customer queries and then want to measure KPIs such as agent responsiveness to customer queries or the number of queries handled per agent in a month. As explored in this article, it’s possible to use the Microsoft Graph to extract some KPI-like data from shared mailboxes.
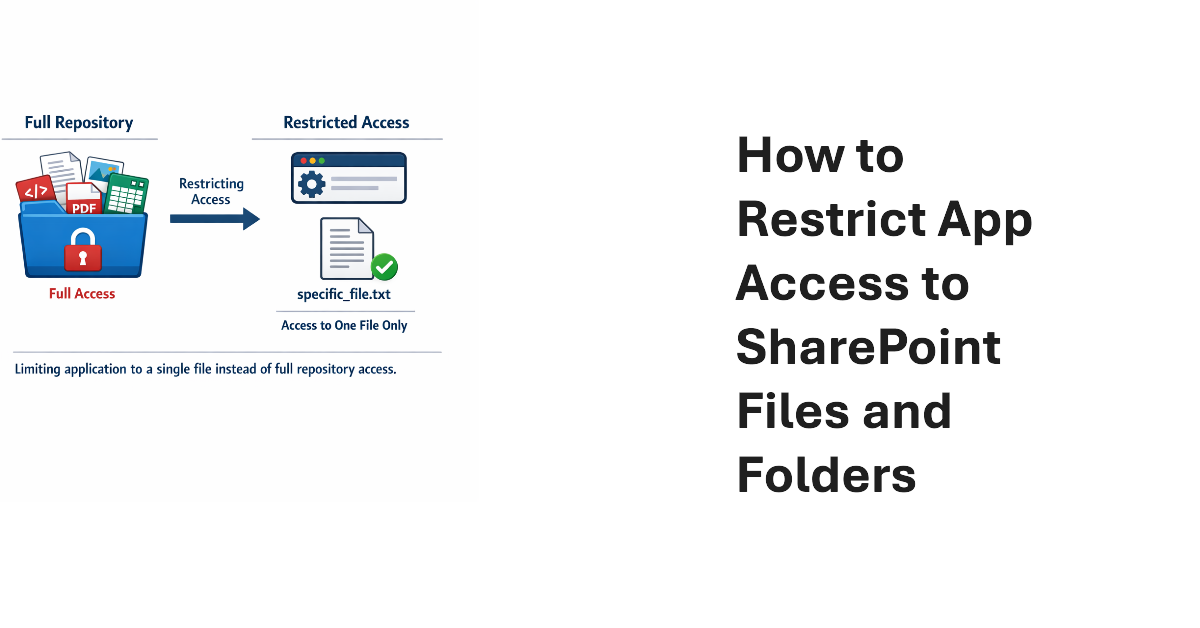
This article explains how to use scoped Graph permissions to restrict app access to lists and list items in SharePoint Online and OneDrive for Business sites. It’s a follow-up to other articles covering how to restrict app access to SharePoint Online sites and files. Scoping app access to specific objects is important because otherwise apps can access everything in SharePoint Online, and that isn’t good.
Update #21 for the Automating Microsoft 365 with PowerShell eBook is now available for current subscribers to download from Gumroad.com. Refreshed PDF and EPUB files are available and the paperback version available from Amazon.com is also updated. Automating Microsoft 365 with PowerShell is packed with practical ready-to-use examples of working with apps, sites, mailboxes, teams, plans, and other data. Every Microsoft 365 administrator should have this book!
Dev Proxy is a Microsoft tool built to help developers figure out the most effective way of using Microsoft Graph API requests. On the surface, Dev Proxy doesn’t seem like a tool that would interest people who use the Microsoft Graph PowerShell SDK to write scripts for Microsoft 365. But all tools have some use, and Dev Proxy can help.
Scoped permissions grant apps granular access to files and folders in SharePoint Online and OneDrive for Business sites using the Files.SelectedOperations.Selected Graph permission. The permission allows apps to access specific files or all the files in a folder. It’s a great way to make sure that apps don’t have unfettered access to confidential documents. Not that any app would try to have that kind of access…
The temptation to use the Mail.Send application permission in scripts can lead PowerShell developers into trouble because the permission allows access to all mailboxes, including sensitive executive and financial mailboxes. Fortunately, RBAC for Applications allows tenants to control the access that apps have to mailboxes and other Exchange content. All explained here with an example script to test RBAC of Applications.
On February 12, Microsoft announced the deprecation of the Credential parameter for the Connect-ExchangeOnline cmdlet in the Exchange Online PowerShell module. The deprecation won’t affect interactive sessions (which should all be protected by MFA), but it might stop some background jobs running when Microsoft retires the server components that currently support the ROPC authentication flow. Time to check scripts!
Monthly update #20 for the Automating Microsoft 365 with PowerShell eBook is now available for subscribers to download the updated EPUB and PDF files. Like any monthly update, #20 includes a mixture of new information, revisions, and even some bug fixes (changes to text or examples). Meantime, assembly clashes continue to be a bugbear for Microsoft 365 PowerShell modules. Microsoft should fix this problem!
An article from 2018 uses the AzureAD and Exchange PowerShell modules to synchronize membership between a security and a Microsoft 365 group. The idea is to enable collaboration for the members of the security group. This version does the work with the Microsoft Graph PowerShell SDK. The code is better and it will work as an Azure Automation runbook, which is always nice.
The Web Account Manager (WAM) authentication broker becomes the default method for handling interactive Microsoft Graph PowerShell SDK connections from V2.34 onwards. The rapid release of a new version (V2.33 appeared 12 days beforehand) is usually a sign of a big problem, but in this case the reason is more likely to be a security vulnerability that’s just come to light. We’ll find out after the holidays.
Update #19 of the Automating Microsoft 365 with PowerShell eBook is now available. Subscribers can download the updated PDF and EPUB files from Gumroad.com. A paperback version is also available, but we can’t update the print characters. In any case, a new SharePoint create Site API is in beta, and a new version of the Microsoft Graph PowerShell SDK is available. Both have their moments, as we discuss here.
After all the fuss about Teams users inviting people to chat via email, tenant administrators realize that knowing where users are active as guest accounts is not as easy as it might seem. Part of the problem is that data about user activity is mostly controlled by host rather than home tenants. However, it’s possible to extract some information from audit sign-in logs to figure out where tenant users go as guests.
The latest versions of the SharePoint Online PowerShell module support app-only authentication (certificate-based authentication) for the Connect-SPOService cmdlet. In other words, applications can now connect to SharePoint Online to run administrative cmdlets by presenting a registered Entra ID app and an X.509 certificate instead of the credentials for a human SharePoint administrator. It’s a good change, even if I still prefer using the Graph APIs for SharePoint automation.
The December 2025 update (version 18) of the Automating Microsoft 365 with PowerShell eBook is now available to download. Current subscribers can fetch the updated EPUB and PDF files from Gumroad.com using the link in their account (or receipt), but we can’t do much for the paperback edition except consider using scissors, paste, and Tippex, just like the old days.
If you can’t use managed identities, credential resources are a way to manage username and password credentials for Azure Automation runbooks. The Secret Management module is an alternative, and it’s a good option to manage credentials that are shared between interactive scripts and automation runbooks. This article describes how to use the Secret Management PowerShell module to fetch credentials stored in Azure Key Vault for use in an automation runbook.
What’s the best way to find SharePoint sites with the Microsoft Graph PowerShell SDK? Is the Get-MgAllSite cmdlet best or should you use the Get-MgSite cmdlet? Does it matter if you’re looking for one site or many sites? We explore the issue in this article by examining some reasons why you’d choose Get-MgSite and others that drive the decision for Get-MgAllSite.
New Graph APIs allow Entra administrators to restore a conditional access policy with a Graph request. This article explains how to list, restore, and permanently remove soft-deleted conditional access policies using Graph API requests run in PowerShell. Being able to restore conditional access policies removed in error closes a big gap, especially if agents might begin working on policies. Who knows what errors might happen in future.
An assembly clash happens when a PowerShell module attempts to load a .NET assembly only to find that a different version is already loaded in the session. Unhappily, this kind of thing happens far too often with Microsoft 365 modules, which implies that there isn’t a great deal of coordination between different development groups. All you can do is to load modules in the right order.
A change to a Graph beta API meant that some data used to create the user password and authentication report was no longer available. A script update was required. The experience underlines the truth that developers should not rely on the Graph beta APIs because the APIs are prone to change at any time as Microsoft moves them along to become production-ready.
This article describes the prerequisites and how to run cmdlets from the Teams PowerShell module in Azure Automation runbooks. We also consider when you’d want to consider using Teams PowerShell cmdlets instead of Graph API requests or cmdlets from the Microsoft Graph PowerShell SDK. The bottom line is that it’s possible, but maybe not a frequently-used option.
MC1134747 describes a new permissions requirement for Entra apps that run Teams PowerShell cmdlets. Fixing apps to meet the new requirement is easily done with PowerShell. First, find the apps that use Teams PowerShell (we show two ways), and then assign the two required permissions to the apps. All done with a few lines of Microsoft Graph PowerShell SDK code.
A custom runtime environment is a way of defining a specific job execution environment for Azure Automation runbooks, including Microsoft Graph PowerShell SDK runbooks. In this article, we create a new environment for PowerShell V7.4, load in some SDK modules, switch a runbook from a system-generated environment, and run some code.
The Office 365 for IT Pros eBook team is proud to announce the availability of update 15 for the Automating Microsoft 365 with PowerShell eBook. The book includes extensive coverage of how to work with Microsoft 365 workloads through standard modules, Graph APIs, and the Microsoft Graph PowerShell SDK, including hundreds of practical examples over 350-plus pages. No fluff, just real-world code.
Three new Graph API resources provide easy access to Entra ID authentication method summary data. The information is helpful to understand the type of sign-ins that happen, and the authentication methods used by user connections. The article includes a script based on the MFA sign-in summary to highlight non-MFA connections and the apps users connect to.