No Microsoft 365 admin portal will tell you about the set of email addresses assigned to Teams channels. Fortunately, it’s relatively easy to create a report with PowerShell and just a little Graph magic.
The Get-MailTrafficSummaryReport cmdlet gets a lot of praise in some quarters. I am not so impressed. The Exchange Online cmdlet is useful, but it’s now showing its age in a world when better data to create a view of user activity is available elsewhere, notably in the Microsoft Graph. This doesn’t mean that the cmdlet doesn’t do a good job; it’s just that it hasn’t received much love from Microsoft since 2015.
Microsoft 365 Data Loss Prevention (DLP) policies have wide-ranging capabilities when it comes to rules and exceptions. One exception covers the various types of encrypted email that can pass through the Exchange Online transport pipeline. As it happens, three message types are supported, but who could have guessed that permission controlled means rights management?
Microsoft announced the preview of the Send from Email Aliases feature on January 25. The only problem is that the same feature was released in April 2021. And OWA gained full support for it in October 2021. So why would Microsoft reissue an existing feature? They’re not saying, but I suspect it’s down to fixing some issues in the Exchange Online transport service to make sure that messages sent from an email alias work properly in every circumstance.
Outlook desktop couldn’t display actionable messages generated by Teams and Yammer properly while OWA and Outlook mobile could. It’s a small issue in the context of Microsoft 365, but it irritated me. I fixed the problem but don’t know how except that the Actionable Messages Debugger for Outlook might have been involved. Another day in the life of a Microsoft 365 tenant administrator…
Microsoft is changing the way the Exchange Online transport service resolves the membership of dynamic distribution groups. Instead of doing this when someone sends a message to a dynamic group, Exchange resolves the membership once daily and whenever the recipient filter changes. It’s a reasonable approach designed to make messages move faster and more reliably, and it’s similar to the way that Azure AD dynamic groups maintain their memberships, so it shouldn’t make much difference.
Exchange Online transport (mail flow) rules are a powerful way to manipulate messages as they pass through the transport system. In this example, we look at how to BCC messages sent by some employees for management review. I’m not sure that this is a good idea (for many reasons), but the need does exist to copy messages automatically, so we explore the use of transport rules as a solution.
Every Exchange Online tenant has four mailbox plans. Exchange uses the plans to populate some important mailbox settings based on the license assigned to the mailbox owner. This article explains the four mailbox plans, how to update the plan settings, and some of the things you can’t do with mailbox plans. We also include some PowerShell to report the mailbox plans assigned to users in your Office 365 tenant.
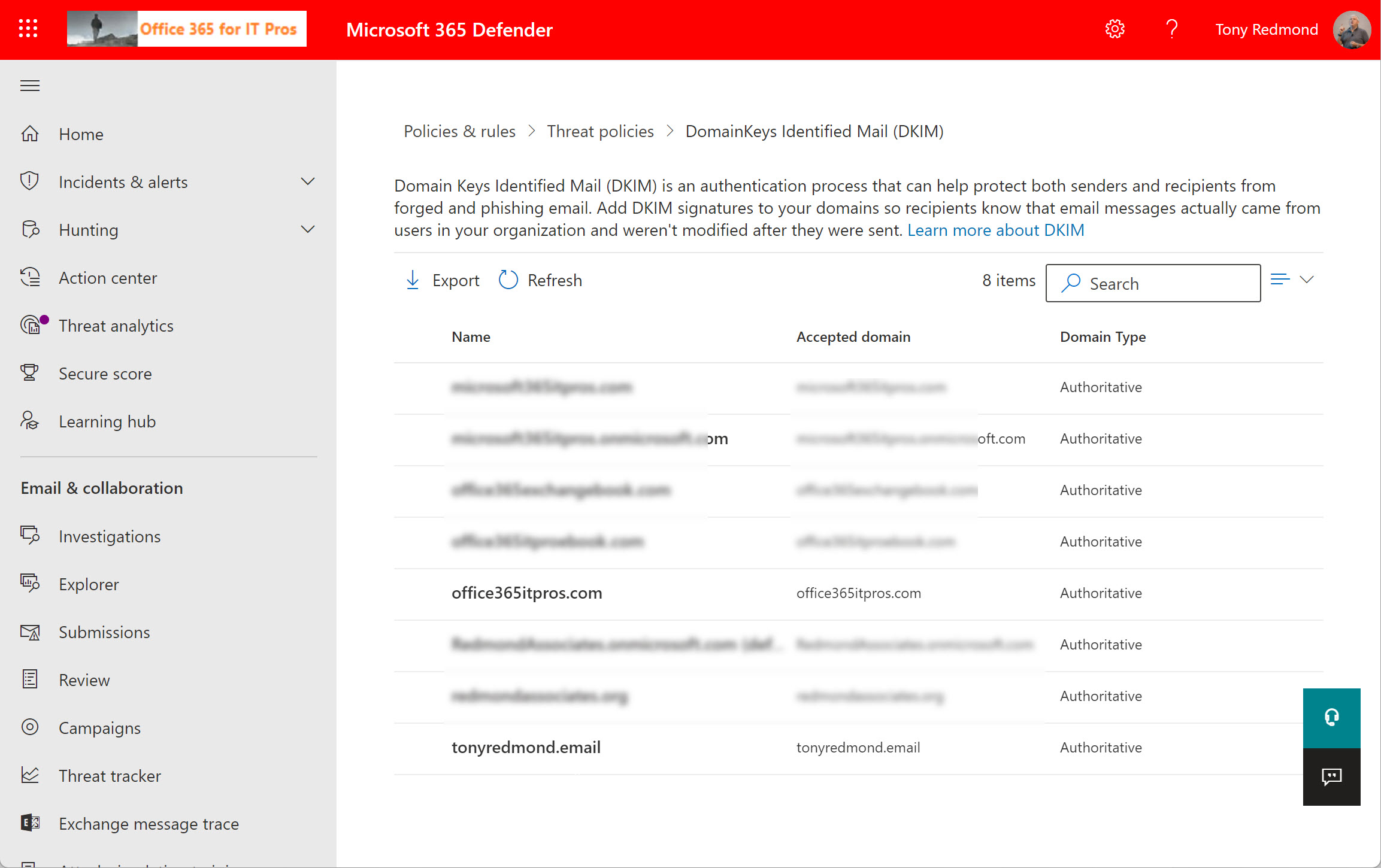
A new Microsoft 365 DKIM management page is a good prompt to check that all domains used to send email in n Office 365 tenant are configured properly for DKIM. The process of enabling DKIM and key rotation is easily done through the GUI or PowerShell once the correct CNAME records are in DNS.
Most Microsoft 365 tenants will have to manage the mailboxes of ex-employees. Retention policies are an excellent method to achieve this goal, if you remember to add mailboxes to a suitable retention policy before deleting their Azure AD account. In this article, we consider Microsoft’s recommendation to use a specific retention policy for inactive mailboxes and how to go about using such a policy.
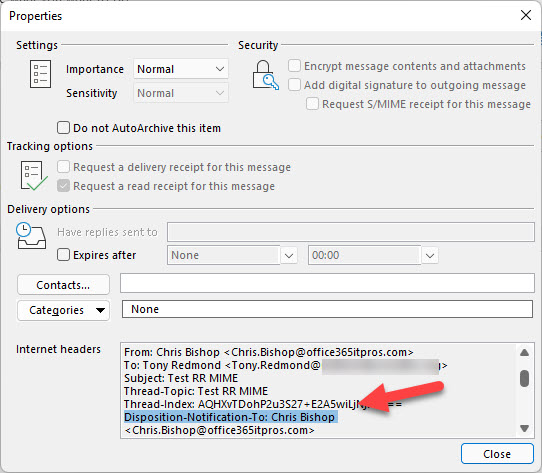
A reader request asked how to force users to send read receipts. This is a client-side feature so the settings involved differ from client to client. We explore how to control them in OWA and Outlook for Windows. A mixture of PowerShell and system registry settings help create a solution. We’re leaving figuring out how to manage other clients to our readers.
A recent update to OWA adds the option to allow users to choose which proxy addresses assigned to a mailbox they would like to send messages from. It’s a small change which completes the client support for the earlier server-side update to allow users to send using mailbox proxies, and it makes using proxy addresses more approachable and useful. OWA also includes a drop-down list in the compose message screen to allow users to select an address to send from, and makes sure that message headers are updated correctly so that messages go back to the right address.
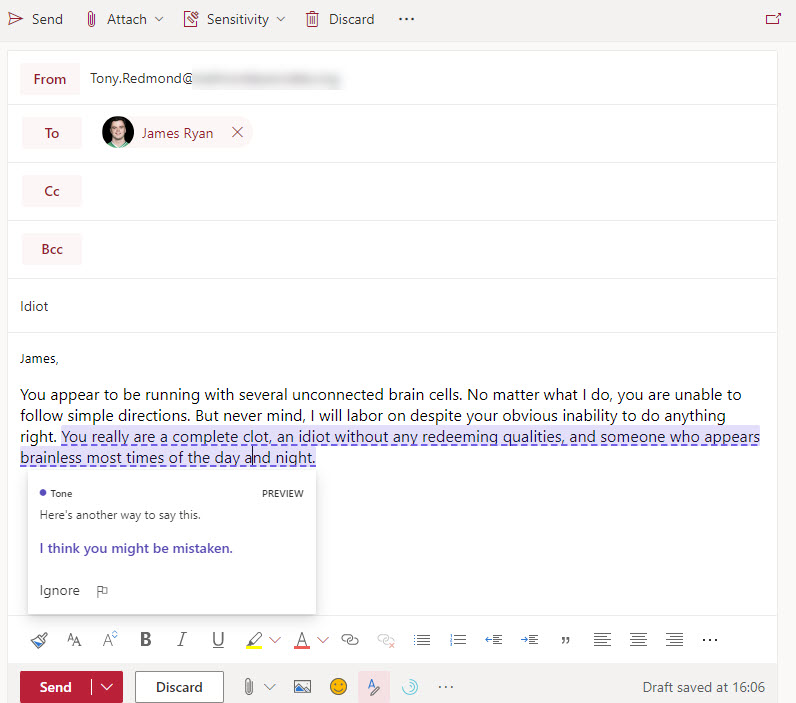
A new Microsoft Editor feature aims to make OWA messages more polite through “tone detection.” Currently only available for U.S. English, Editor scans for impolite text and comes up with suggested replacement text. The results vary from very good to not so good, but this might be because it takes time for a learning model to accumulate enough information about a user’s writing style to be able to detect impolite text accurately. We’ll know over time.
Microsoft is applying their Viva brand to the features currently known as MyAnalytics. Viva Insights will span a monthly email digest, the Outlook insights add-on, and the Insights dashboard. If you don’t want users to access these features, you can disable the features individually or remove the service plan from user licenses. The rebranding is happening now and due to complete in November.
Microsoft hopes to accelerate the removal of TLS 1.0 and 1.2 connections from Exchange Online by disabling connectivity in 2022 and forcing organizations which need to use the older protocols to connect to a new “legacy smtp” endpoint. It’s not a bad plan because it transfers responsibility for choosing to use obsolete connections to customers. Most organizations will go with the flow (no pun intended) and use TLS 1.2, but those who need some time to update applications and devices know what they have to do.
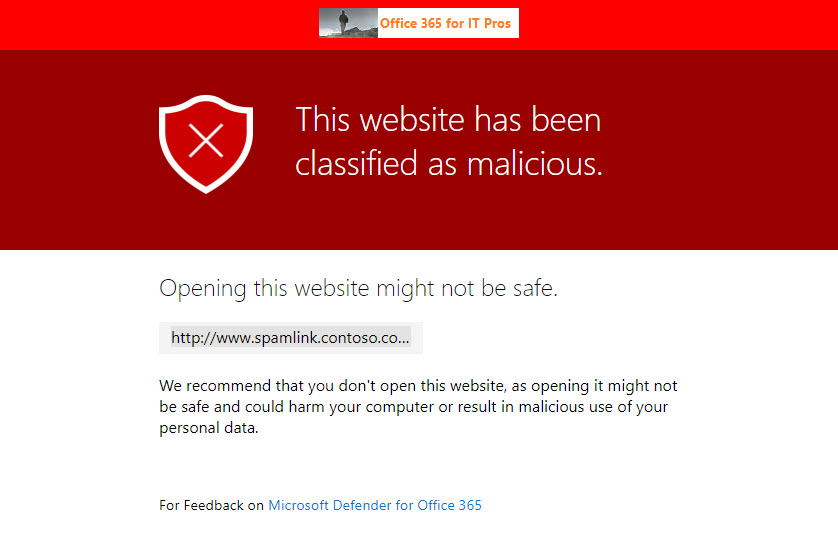
The Safe Links capability in Microsoft Defender for Office 365 is now generally available to protect Teams messages in chats and channel conversations, and even in web site links pinned as a channel tab. Most bad links flowing into an Office 365 tenant will continue to arrive by email, but this new capability closes off a gap where users are tempted to make a poor decision to share a malicious link through Teams.
Exchange Online already imposes limits on the number of messages a mailbox can receive per hour. New limits will restrict the number of messages individual senders can send to a third of the overall limit. The restriction doesn’t apply to senders with an Exchange Online mailbox in the same tenant. And if a mailbox runs into a limit, it features on the splendidly named Hot Recipients report. What’s not to like about that.
Microsoft says a change to Outlook shared calendaring is arguably the biggest made since 1997. That’s all marketing hyperbole because many other more important technical advances have occurred in that time, including drizzle mode synchronization, Autodiscover, and Outlook Anywhere. What’s your favorite Outlook feature since 1997?
Exchange Online assigns large mailbox quotas to users. These quotas are needed to cope with the volume and size of modern email. What used to take 2 KB in 1996 now consumes 60 times more. And while email is more graphical and prettier to look at, you’d wonder if the value of the actual content has changed much, if at all.
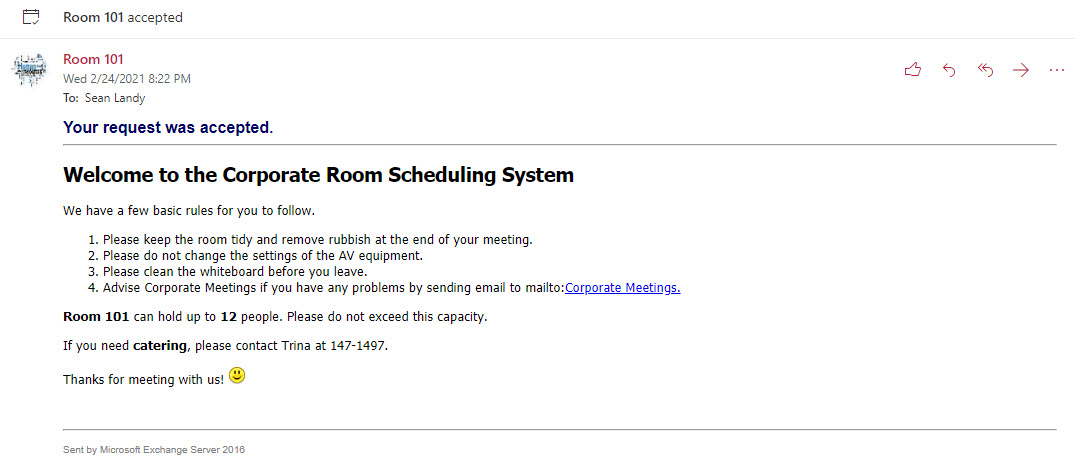
Exchange Online’s calendar assistant is good at responding to meeting requests for rooms. It can be even better with just a little customized text to remind those who book the rooms about meeting etiquette. Even though we might never get back to physical meetings in conference rooms, some face to face gathering will happen in the future, so now’s the time to prepare for bookings to be handled in a nicer fashion.
Teams supports several methods to import email. Outlook for Windows can drag and drop messages into Teams conversations. It’s a quick and easy way to move the focus of a conversation, but there are some downsides to be aware of.
A new phishing attack is circulating from an Office 365 tenant. The attack attempts to lure recipients into clicking a link to download a document. The phishing email is not quite as crude as other attempts and might lure users into doing the wrong thing, especially as the message is delivered to inboxes.
You can configure Exchange Online distribution lists so that they reject messages sent to them as BCC recipients. I’m not sure how much use this feature will get, but it’s nice to have it anyway. PowerShell is the only management tool to configure distribution lists for the new block until Microsoft gets around to updating the Exchange Admin Center.
Exchange Online tenants can activate external email tagging, which causes Outlook clients (not desktop yet) to highlight messages received from external domains. The feature can replace custom implementations to mark external email, usually done with transport rules. It’s easy to implement and control, but the mail tip offering to block an external sender seems a little over the top.
From April 2021, Exchange Online will apply hard limits for the number of messages a mailbox can receive per hour. The limit remains the same (3,600), but now Exchange will block the mailbox receiving any more email for an hour. The new version of the Exchange Admin Center (EAC) promises to highlight problem mailboxes so that admins can ask owners why their mailboxes receive so much email.
A change made to the storage location in SharePoint Online for email sent to Teams channels caused problems for people who created Flows based on a known location. Instead of having one big folder for email messages sent to a folder, it seems like Microsoft plans to use a new folder for each month. There’s nothing wrong with this approach, but it would have been nice if Microsoft warned people using the folder for automated processing that a change was coming. They didn’t.
Exchange dynamic distribution lists allow messages to be sent to sets of recipients determined by a query against the directory. A custom filter is a powerful way to find the right set of recipients. In this case, we want to find mailboxes with certain job titles whose Azure AD accounts are not blocked for sign-in. Here’s how to create the filter, make sure it works, and create the DDL.
Exchange Online Dynamic Distribution Lists are a powerful way to address changeable groups of recipients. The query against the directory is the big thing to get right, but you’ve also got to make sure that the directory data is accurate and reliable. Once you’ve got a good directory, it’s easy to create dynamic distribution lists which are easy to use and never go out of date.
Office 365 Message Encryption (OME) allows OWA users to revoke some messages after they are delivered to recipients. But if the message goes to Office 365 or Outlook.com, you can’t revoke it. And there’s the slight matter of needing an Office 365 E5 license too. Even so, it’s still nice to be able to revoke messages if they go to the wrong place.
Exchange Online supports dynamic distribution lists, a great way to address sets of recipients found by resolving a filter against the directory. In this example, we explore how to create a dynamic distribution list to address mailboxes marked as preferring a specific beverage. It might even be useful some day!
At the Ignite 2020 virtual conference, Microsoft ISV Code Two Software demonstrated a new Outlook API to make email signature management easier across all Outlook clients. The Signature API supports web add-ins that work on all Outlook platforms to allow users to select which corporate email signature to apply before sending messages. The new API should be available at the end of 2020 and we can expect updates from multiple ISVs in the email signature management space to exploit the new capability.
Power Automate (Flow) can forward email from Exchange Online mailboxes to external recipients. This isn’t a great idea if you want email kept within the control of your data governance framework. Power Automate now inserts x-headers in the email it sends, which allows the use of transport (mail flow) rules to detect and reject these messages if required.
Characterizing backup of Exchange Online mailboxes to PSTs as brain-dead might have been harsh, but it’s an accurate assessment of the worth of this idea. Plenty of cloud-based backup offerings exist that can process Exchange Online data more securely and at scale. If you want to backup Office 365, stay away from PSTs and use a different product, after asking some questions to ensure that the backups deliver the value you expect.
Exchange Online Protection monitors outbound email to pick up signs of potential compromise in Office 365 tenants. This can lead to EOP restricting a tenant’s ability to send outbound email and force the administrators to check for compromised accounts or connectors and other problems before contacting Microsoft Support to ask them to lift the restriction.
Exchange Online Protection monitors email traffic in and out of Office 365 tenants. When a mailbox exceeds limits, it might end up being restricted, such as in the case when the mailbox might be compromised. We tried to find out when Exchange Online Protection restricted mailboxes and what to do afterwards. Here’s what we discovered.
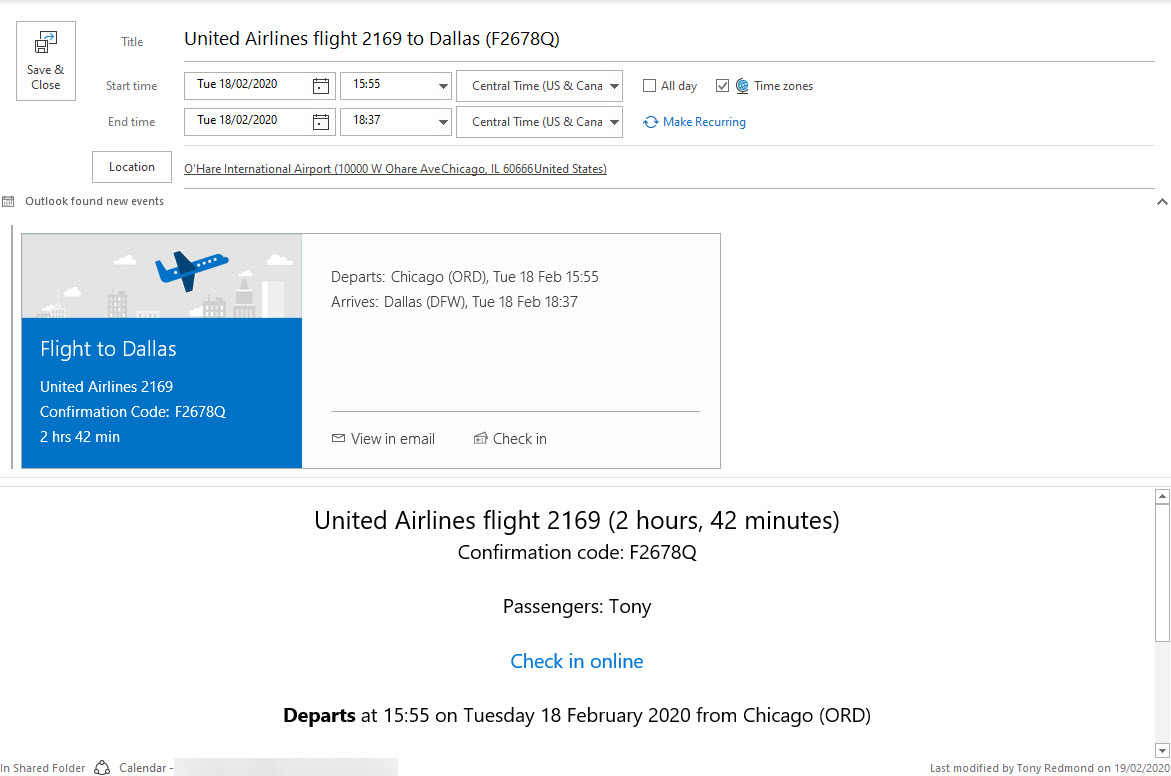
Exchange Online will soon drop processing email to create calendar events for things like restaurant reservations. The good news is that travel details are still supported, meaning that you won’t have to extract and enter details like flight numbers, departure times, and so on. And notifications for your Amazon deliveries continue too.
Covid-19 dealt a blow to Microsoft’s plans to remove basic authentication from 5 connection protocols for Exchange Online and forced them to postpone the removal from October 13, 2020 to sometime in the second quarter of 2021. The news is disappointing because basic authentication is a weakness exploited by many hackers. But you can’t plan for a pandemic and Office 365 tenants need more time to be ready for the deprecation.
Microsoft has revealed that Outlook for iOS is getting a new rich text editor to brighten and embellish email messages. The new editor is in build 4.27.0, but there’s no news if Outlook for Android will get the same editor.
Outlook Mobile now supports delegate access to Exchange Online mailboxes. By granting fuil access to a delegate, they can open and work with a mailbox, and send messages using the SendAS or SendOnBehalfOf permissions. The new feature underscores the advantage Outlook mobile enjoys over other mobile Office 365 email clients.
Exchange transport rules are a powerful way to apply different conditions to messages as they pass through the transport service. In this case, we add a disclaimer to calendar meeting requests with a pretty simple rule that works on the basis that it detects a special x-header in meeting requests and applies the disclaimer when the x-header exists.