The BlockContentAnalysisServices sensitivity label setting blocks access to Microsoft connected services for the content of labeled Office documents. The intention is that users assign sensitivity labels with the block setting to protect an organization’s most sensitive files. Regretfully, Microsoft’s documentation and explanation offered in the message center post don’t convey a clear story about its value.
The advent of the MoreRecordsAvailable property gives the Search-UnifiedAuditLog cmdlet more precise control over fetching large numbers of audit records (up to 50,000 records). It’s a welcome change to report something positive about the Microsoft Purview Audit solution because most of the time we complain about its stability, slowness, and bugs. Things are looking up.
The Get-AdaptiveScopeMembers cmdlet reveals details of adaptive scope membership to make it possible to report this information programmatically. The task is not as simple as you might imagine. Summary records must be separated from member records, which can reflect add or remove operations. And there’s the question of pagination for large adaptive scope. All explained here with a PowerShell script to help.
A new Exchange Online feature allows administrators to remove multiple types of holds from mailboxes (usually inactive mailboxes). It’s a great way to release holds that might be keeping inactive mailboxes lingering in a tenant. The feature doesn’t remove holds used to retain items required for eDiscovery or other compliance purposes. Even so, this is definitely a feature that needs to be carefully tested.
Microsoft has released a set of security benchmark recommendations for Microsoft 365 tenants that it calls baseline security mode. The recommendations cover authentication, file access, and Teams and the idea is that these are settings that Microsoft believes have proven their value over the years. The only criticism that you might have is about the potential clash for conditional access policies, but that’s not serious.
Paul Robichaux and I led a session about Microsoft 365 Compliance at the European SharePoint Conference in Dublin on December 2, 2025. During the session, we discussed how intelligent versioning works and its value in saving storage, priority cleanup and its ability to delete files even if the files are under retention hold, and the recent revamp of the Purview eDiscovery solution. We were thrilled at the attendance. Here’s what happened.
A new DLP policy for Copilot prompts monitors blocked sensitive information types like credit card numbers to stop their use in Copilot prompts. The new policy can’t be combined with the existing DLP policy for Copilot, which checks for files with specific sensitivity labels to prevent Copilot from using their content in its responses. But that’s OK because the two policies do very different work.
Microsoft announced the modernization of grouping for sensitivity labels to a new “dynamic architecture.” It doesn’t take much to be more dynamic than the previous parent-child arrangement. Even if the announcement is a tad overhyped, it’s still goodness because administrators can now move labels between label groups in a way that wasn’t possible before. The new way of displaying labels should be everywhere in December 2025.
One of the settings for sensitivity labels governs how long items protected by a label remain accessible (including offline access) before reauthentication. The default is 30 days, which is a good balance between security and avoiding users having to constantly reauthenticate to open protected messages and files. If necessary, tenant administrators can change the validity period to be anything from 0 to 65535 days.
After a report to the MSRC about some missing file data from Copilot audit records, Microsoft fixed the problem and audit records now contain details about the SharePoint Online files reviewed by Copilot to construct answers to user prompts. Having solid audit and compliance data is a good thing, unless you’re a lawyer charged with defending an eDiscovery action who might be asked to produce the files.
Purview Priority Cleanup is growing its capabilities to be able to process files stored in SharePoint Online and OneDrive for Business. Public preview begins in mid-August, and the solution should be generally available at the end of September 2025. Removing files without regard for retention holds is much more complicated than removing mailbox items. The question is who needs this feature and how will it be used?
Litigation holds can retain mailbox data, but that’s it. You can swap litigation holds out for a Microsoft 365 retention policy and gain extra functionality, such as retaining OneDrive for Business content for the mailbox owners. It’s easy to script the transition from litigation holds to retention policy using PowerShell and to show how, we include a fully working script.
Microsoft recently announced the deprecation of the Exchange cmdlets to search for mailbox audit data. The audit data is ingested into the Microsoft 365 unified audit log, but it’s more difficult to find and retrieve Exchange mailbox audit events. Methods are available to find mailbox audit data, but interpreting what comes back is different. Any script that depends on the old cmdlets must be updated to interact with the unified audit log.
Litigation holds were great when introduced with Exchange 2010. Fifteen years on, better methods exist to preserve user information, like eDiscovery holds. It might seem unnatural to move from litigation holds to eDiscovery cases, but this approach allows the preservation of both mailbox and OneDrive content for as long as necessary. Retention policies can serve the same purpose, so choice exists for modern preservation.
Microsoft is making some important changes to Purview eDiscovery from May 26, 2025. The changes affect how content searches work and are likely to affect many Microsoft 365 tenants. Administrators and eDiscovery investigators will both have to master new ways of working with eDiscovery cases, searching for information, reviewing search results, and exporting what’s found. Changes to PowerShell cmdlets might affect scripts, so there’s lots to consider.
Microsoft Purview makes it easy to apply sensitivity labels to Office documents and PDF files with auto-label policies. Licenses are needed for auto-label policies, but at what cost? We look at the various licenses available to cover the functionality and consider if a DIY approach using the Graph API to apply labels would be cost effective.
The Microsoft E5 Security add-on is available for Microsoft 365 Business Premium (and other) tenants. The add-on looks like a bargain because the bundle offers significant value over individual licenses, but is it really? Like everything in life, unless you can use something, there’s no point in having it. In this case, have a plan to use E5 Security to deliver measurable results before you hand over any more license revenue to Microsoft.
Often Microsoft 365 tenants have large numbers of old but confidential documents that they need to protect and stop Microsoft 365 Copilot finding. Auto-label policies and trainable classifiers can apply sensitivity labels to protect Office files from Microsoft 365 Copilot using the DLP policy for Copilot. It’s a great example of combiining Microsoft 365 features to achieve a goal.
File sharing is at the heart of SharePoint Online. Being able to report file sharing events by analyzing the audit log is a good skill for Microsoft 365 tenant administrators to have. It allows administrators to know who shared what with whom and if the information being shared is protected adequately with sensitivity labels. But reporting file sharing is not just a matter of retrieving audit events. Work is necessary to refine and extract the goodness from the data.
A reader asked if it’s possible to discover who made retention label assignments for SharePoint files. The Files Graph API can’t tell you who (or what policy) made retention label assignments, but it’s possible to find this information in the audit log and use that data to report the requested information. All with a few lines of PowerShell!
The DLP policy for Microsoft 365 Copilot blocks access to sensitive files by checking for the presence of a sensitivity label. If a predesignated label is found on a file, Copilot Chat is blocked from using the file content in its responses. The nicest thing is that the DLP policy prevents users knowing about sensitive information by searching its metadata.
There’s no doubt that SharePoint Online sites and OneDrive for Business accounts hold lots of old files. A new On Demand Classification PAYG service aims to find and classify that data and apply sensitivity and retention labels based on policy settings. It’s a good idea for tenants that has these kinds of cold files hanging around gathering dust without anyone knowing if any of the files hold confidential information.
Microsoft has announced the removal of events alerts from the Purview Audit solution. Fortunately, the decision doesn’t affect activity alerts. Audit-based activity alerts are a way for tenants to mark events that they want to be notified about through email when these events appear in the unified audit log. Although they remain available, better ways exist to monitor critical audit events. The only problem is deciding which approach to take.
This article describes how to use Azure Automation for audit searches. The runbook runs an audit search to find events for specific operations, refines the set of events found by the search, and sends the information by email. Hopefully, someone will respond to the message and do the right thing to check the insight derived from the events.
On December 12, Microsoft said that they want to make the Search-UnifiedAuditLog cmdlet use high completeness for all its searches. If implemented, the result will be a disaster because many of the current uses of the cmdlet to retrieve audit log data will be rendered impracticable because of the slowness and unreliability of high completeness searches. Microsoft just doesn’t seem to understand how its software is used in production.
This article describes how to report the audit events for a user over a single day. The task seems simple, but inconsistency in audit payloads makes it harder. Workloads don’t help by the variations in audit events. In any case, persistence and knowledge about what the audit event captured for an action helps to decode the data, as illustrated by the script detailed here.
Microsoft recently renamed the default set of sensitivity label permissions. Each permission defines the usage rights for a labelled item for users. The rights range from the basic actions like edit, save, and print to the more advanced extract, right to run macros, and export. The trick is to make sure that sensitivity labels assign the right permissions to users.
The Purview Insider Risk Management solution can do all sorts of clever things, like tracking sensitivity label downgrades and removals as an indicator that a user might be preparing to exfiltrate data. The same kind of checking can be done by using the events captured in the audit log when people remove or change sensitivity labels. All in a few lines of PowerShell…
In a November 8 post, Microsoft says that Purview Data Lifecycle Management will allow tenants to split processing of Copilot interactions and Teams chats with different policies. The public preview for the change should be available in mid-November. This update makes perfect sense because there’s no logic to dictate that Microsoft 365 tenants want to impose the same retention period for Teams chats and Copilot interactions.
A recent article about analyzing interaction records for Microsoft 365 Copilot led to the question if it’s possible to do the same for Microsoft Copilot. After checking the compliance records captured by the Microsoft 365 substrate, we discovered that Microsoft Copilot generates compliance records. However, a bug with encoded text means that the information captured for responses from Microsoft Copilot and Microsoft 365 Chat isn’t visible. All explained here.
A reader asked how to find emails with sensitivity labels. Everyone knows that you can find SharePoint files protected by sensitivity labels, but what about emails? MAPI properties exist that hold details of sensitivity labels. These properties are promoted to Microsoft Search, and this allows features like end-user searching through the Microsoft 365 app and Outlook to work. But the best way to find emails with sensitivity labels is to use a Purview content search.
Adaptive searches are a nice way to target users, sites, and groups for Purview retention processing. But a user adaptive scope can’t select members of a group and target them. That is, unless you use the same attribute to identify users for both a dynamic group and an adaptive scope, which is what’s explained here.
MC894577 announces that DLP policy tips displayed in Outlook will soon support a set of new conditions. That’s good, but the text of the announcement is unclear about important points like the clients that will support the new policy tips, what kinds of groups are supported by the conditions, and precise details of how Outlook will differentiate between users with Office 365 E3 and E5 licenses.
eDiscovery is a calling best left to skilled investigators. But Microsoft 365 administrators need to know how to search and how the new Purview eDiscovery works. The new implementation is due by the end of 2024 and is in preview now. It unifies the three existing solutions in the Microsoft 365 eDiscovery space and promises to deliver new functionality. But will it make its dates? Who knows!
Three years ago, I wrote a script to analyze the audit records generated for Teams meeting recordings. Then things changed in terms of how the audit records were generated and how the Search-UnifiedAuditLog cmdlet returns audit search results. All of which meant that considerable work was needed to revamp (rewrite) the script. Maybe you need to check any script that uses the Search-UnifiedAuditLog cmdlet too?
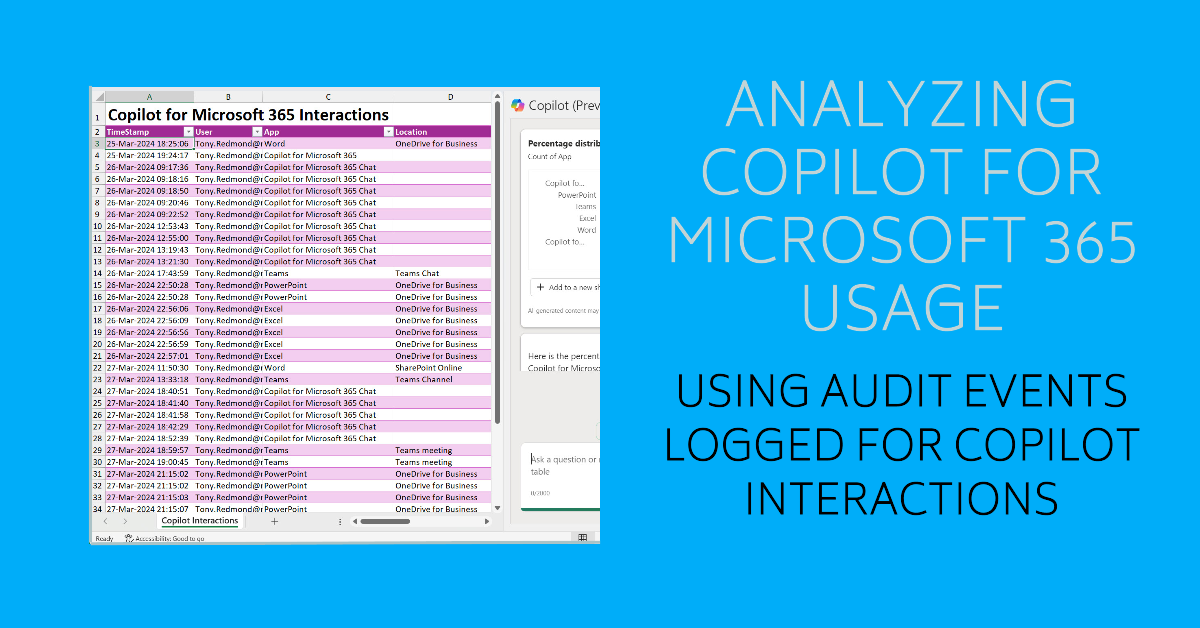
The unified audit log includes Copilot for Microsoft 365 audit events captured when users interact with Copilot through apps. The information is very helpful in terms of understanding the usage of Copilot in different apps (apart from Outlook, which isn’t captured). Some care needs to be taken to understand the data and interpret the audit events, but that’s usual when dealing with Microsoft 365 audit data.
A new preview feature supports high completeness audit log searches. These searches are optimized to make sure that they find every matching audit instead of finishing as quickly as possible. High completeness audit log searches do take more time but their results are accurate and they find more records than Search-UnifiedAuditLog was able to in the past. Looks like a good new feature.
A January 26 post announces the deprecation of four old Exchange audit cmdlets in favor of the Search-UnifiedAuditLog cmdlet. Removing old cmdlets is fine, but it would be nice if Microsoft took the opportunity to make Search-UnifiedAuditLog work better. Too many inconsistencies exist in how workloads provide information in audit events and Microsoft has made some recent unannounced changes.
In message center notification MC703706 Microsoft announces yet another attempt to retire the Search-Mailbox cmdlet. This time it’s due to happen in March 2024. I don’t mind Microsoft removing old technology from its products, but it’s important that the old functionality is replaced by newer, better technology. And that’s not the case here. At least, not so far.
The Sensitive by Default control allows tenants to prevent external access to newly uploaded documents until DLP processing checks their content. The idea is to close off the opportunity external users have to access control between its upload and DLP scanning of the content. You can combine the sensitive by default control with sensitivity labels to exert maximum control over confidential material.