Purview Data Loss Prevention (DLP) rule checks can happen client-side and server-side. This change updates the Exchange Online organization configuration to instruct OWA to stop using Exchange Online to detect potential DLP rule violations before users send email. Instead, OWA will use the workload-neutral Data Classification Services (DCS). Using a workload-neutral service comes with some consequences in terms of OWA being unable to evaluate Exchange-specific predicates.
MC1169572 announces that administrators can add classifications to DLP alerts to help with reporting. But how do you report DLP alerts? As it turns out, it’s relatively easy to retrieve DLP alerts via the Microsoft Graph Security API. Using the Get-MgSecurityAlertV2 cmdlet from the Microsoft Graph PowerShell SDK makes it even easier to find and report the data.
DLP diagnostics were announced in October 2024, and it’s taken quite a while for Microsoft to make the four DLP diagnostic tests available. In truth, none of the tests are earthshattering and the kind of checking done by the tests could be performed quite easily by an experienced tenant administrator who knows the DLP solution. But those administrators are unlikely to be the target audience for these tests.
The DLP policy for Microsoft 365 Copilot blocks access to sensitive files by checking for the presence of a sensitivity label. If a predesignated label is found on a file, Copilot Chat is blocked from using the file content in its responses. The nicest thing is that the DLP policy prevents users knowing about sensitive information by searching its metadata.
There’s no doubt that SharePoint Online sites and OneDrive for Business accounts hold lots of old files. A new On Demand Classification PAYG service aims to find and classify that data and apply sensitivity and retention labels based on policy settings. It’s a good idea for tenants that has these kinds of cold files hanging around gathering dust without anyone knowing if any of the files hold confidential information.
MC894577 announces that DLP policy tips displayed in Outlook will soon support a set of new conditions. That’s good, but the text of the announcement is unclear about important points like the clients that will support the new policy tips, what kinds of groups are supported by the conditions, and precise details of how Outlook will differentiate between users with Office 365 E3 and E5 licenses.
The Sensitive by Default control allows tenants to prevent external access to newly uploaded documents until DLP processing checks their content. The idea is to close off the opportunity external users have to access control between its upload and DLP scanning of the content. You can combine the sensitive by default control with sensitivity labels to exert maximum control over confidential material.
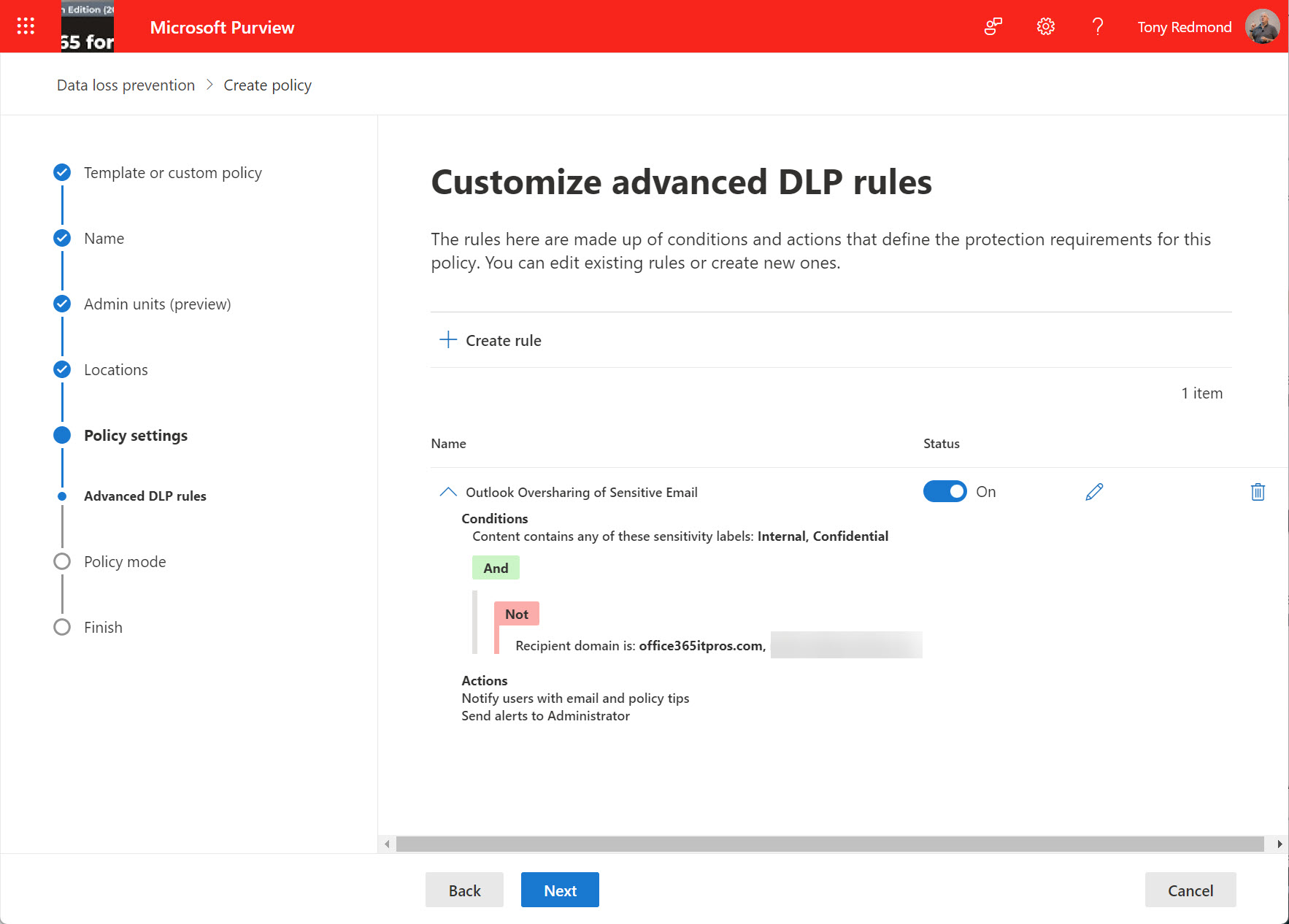
An update for Microsoft 365 Data Loss Prevention policies supports the configuration of oversharing popups for Outlook shown when a user composes email with specified sensitivity labels for either the message or any attachment. The idea is that the popup (a policy tip) helps the user to understand the problem and why they are violating a DLP policy so that they can address the problem before attempting to send the message.
Microsoft 365 Data Loss Prevention (DLP) policies have wide-ranging capabilities when it comes to rules and exceptions. One exception covers the various types of encrypted email that can pass through the Exchange Online transport pipeline. As it happens, three message types are supported, but who could have guessed that permission controlled means rights management?
To make Microsoft 365 DLP policies work like Exchange transport-rule based DLP, a January change will switch evaluation of sender conditions away from envelope information to message headers. Although this change might seem to be something beloved of email geeks, it’s actually an important update for organizations who want to move away from ETR-based DLP to Microsoft 365 DLP policies.
Microsoft has made Endpoint DLP generally available. Leveraging Windows 10 workstations and the Edge browser, Endpoint DLP sends signals for evaluation to detect possible violations. The solution requires Microsoft 365 licenses and only supports Windows, so it’s not for every tenant. But those who have Microsoft 365 licenses will find this an attractive solution.
When you need to block external access to your most sensitive documents, Office 365 Data Loss Prevention policies and sensitivity labels combine to find and protect the documents. A really simple policy is enough to detect and block external access, and is covered by Office 365 E3 licenses. If you have E5 licenses, you can consider auto-label policies to find and protect sensitive documents at scale.
In a sign of how automation based on signals gathered by Office 365 will emerge to help administrators do a better job, the preview of the new Admin Center offered to create a DLP policy to protect some sensitive information that I had clearly overlooked. Well-intended as the portal was, its efforts to create the new policy failed. That’s not really important – it’s the glimpse into the future which is.
Office 365 offers different ways to apply encryption to important messages. When those messages hold sensitive data known to Office 365, like credit cards or passport numbers, we can define a transport rule or DLP policy to protect outbound email automatically. And while you can define rules and policies through the GUI, PowerShell is available too.
Microsoft thoughtfully provided Office 365 tenants with a Data Loss Prevention template for GDPR personal data. The only problem is that the rules in the template were too sensitive and started to block email.