The Microsoft 365 admin center includes an option for administrators to send Copilot diagnostic logs on behalf of users to Microsoft for investigation. Sounds good, but the diagnostic logs are in plain text (JSON format) and the prompts and responses for Copilot user interactions can be viewed by administrators. That doesn’t seem like a good way to preserve anyone’s privacy. Vote for the feedback item to close this loophole.
The Microsoft 365 Connector for Claude allows Claude to access SharePoint and OneDrive files, emails, and Teams chats and meetings. The connector is now available to all users, including the free tier for Claude. Installing the connector creates two Entra ID enterprise apps (MCP server and client) and channels Graph requests to Microsoft 365 to fetch information for processing by Claude. Is that a good thing?
Since the release of the preview version of the UTCM solution, some have asked if UTCM will replace the Maester tool. The answer is no. The tools are complementary and both are very useful to Microsoft 365 tenant management. Maester is a community-driven reporting tool that highlights inconsistencies between external and Microsoft baselines. UTCM focuses on setting drift that can occur in workload configurations. Both have their own niche.
Unified Tenant Configuration Management (UTCM) is a new tenant configuration management solution that can monitor changes to over 300 resource types found within Microsoft 365 tenants. Currently accessible via Microsoft Graph beta APIs to all tenants, UTCM offers an alternative to Microsoft DSC and third-party configuration management products. No details are available yet about an admin UX, licensing, or availability.
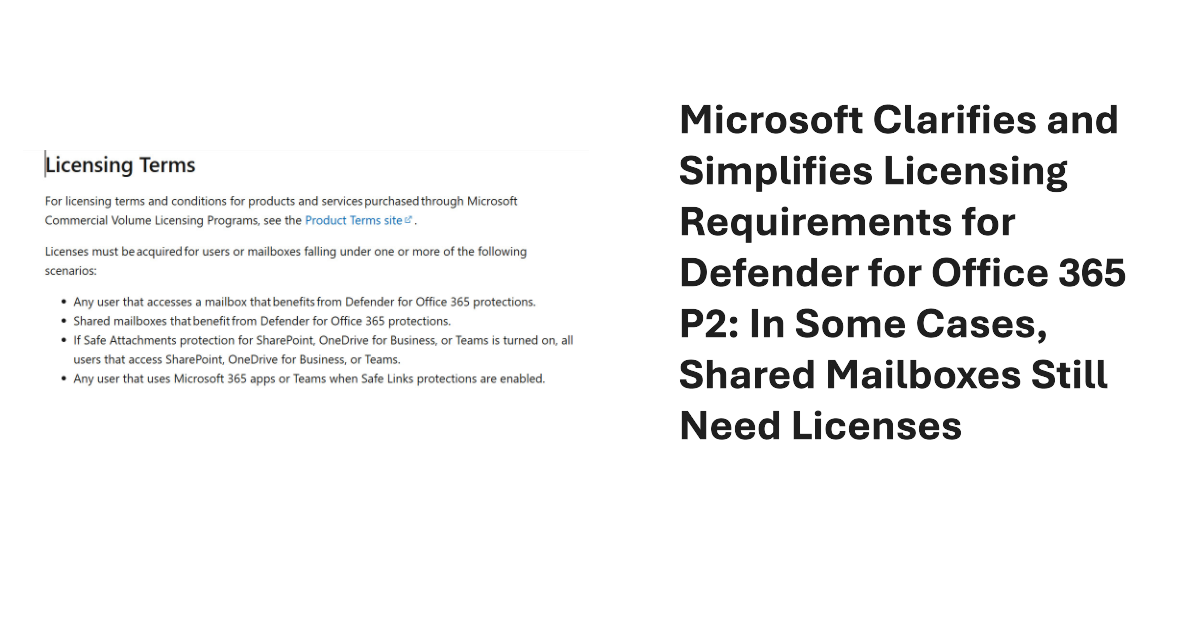
Some inconsistencies in the MDO P2 service description and licensing terms exposed a need for tenants to license every user and shared mailboxes. Microsoft has changed the service description and licensing terms to make them simpler. Mailboxes still need MDO licenses, but only if they benefit from MDO protection, including MDO P2 if that’s what they use. Tenant admins have some extra work to do to deploy policies. All explained here.
Microsoft announced a new Copilot license check diagnostic for the Exchange Connectivity Analyzer. Sounds good, but the test is very simple, and its results don’t tell you anything more than a few lines of PowerShell can deliver. To prove the point, we wrote a quick script to show how to perform a Copilot license check with the Microsoft Graph PowerShell SDK.
The Office 365 for IT Pros eBook team is proud to announce the availability of update 15 for the Automating Microsoft 365 with PowerShell eBook. The book includes extensive coverage of how to work with Microsoft 365 workloads through standard modules, Graph APIs, and the Microsoft Graph PowerShell SDK, including hundreds of practical examples over 350-plus pages. No fluff, just real-world code.
The Microsoft Authenticator app is a secure authentication method for MFA. The app is getting an easier way for backup and recovery, which should make it easier for people to move to new iOS devices. Instead of a Microsoft recovery account, Authenticator will use the iCloud keychain. The update is expected to roll out in September 2025.
The old Set-MsolCompanySettings cmdlet is no more, so how can a Microsoft 365 tenant block email-based subscriptions? With the Graph, of course! Seriously, there’s no 1-to-1 mapping from the old cmdlet to a new, but some of the settings are available in the Entra ID authorization policy. We can update the authorization policy with PowerShell to block email-based subscriptions, like Copilot Studio.
Microsoft Purview makes it easy to apply sensitivity labels to Office documents and PDF files with auto-label policies. Licenses are needed for auto-label policies, but at what cost? We look at the various licenses available to cover the functionality and consider if a DIY approach using the Graph API to apply labels would be cost effective.
Microsoft has announced the removal of events alerts from the Purview Audit solution. Fortunately, the decision doesn’t affect activity alerts. Audit-based activity alerts are a way for tenants to mark events that they want to be notified about through email when these events appear in the unified audit log. Although they remain available, better ways exist to monitor critical audit events. The only problem is deciding which approach to take.
The Microsoft Graph PowerShell SDK offers developers easy access to data across the Microsoft 365 ecosystem and that’s good. However, there’s a problem with Graph SDK plain text passwords that must be fixed. In today’s threat climate, passwords should be passed as secure strings. It’s a small but important step to improve overall security.
A new people administrator role is available in Entra ID. The new role allows holders to manage settings associated with people, like pronouns and custom properties for the Microsoft 365 user profile card. The people administrator role is a less privileged way to assign responsibilities for people actions and removes the need to assign more privileged roles like User administrator. Time for a role review!
Entra ID retains audit log records for service principal signins for 30 days. The audit data can reveal some interesting insights such as the presence of unexpected service principals or access to an application from an external source, or even the use of an app secret by an application instead of a more secure method. It’s time to write some PowerShell to interpret the data.
A set of new granular Graph permissions for User account management is now available to handle common operations like changing account passwords or updating phone numbers. There’s no need to update existing code unless you want to use the principle of lease privilege, in which case you’ll replace the current permissions with the new permissions. My feeling is that relatively few will go update code, but I could be surprised.
The scheduled retirement of Delve on December 16, 2024, meant that Microsoft had to create a new way for users to update their profile settings. The new method has now appeared in Microsoft Search, and it will spread to other workloads (like OWA) where users can access and update their profile. The new mechanism is welcome, but it’s still too difficult to customize user profiles within a tenant.
In February 2025, Microsoft will begin enforcing a mandatory MFA requirement for the Microsoft 365 admin center. All connections to the Microsoft 365 admin center must pass an MFA challenge. The move is to increase the percentage of Entra ID user accounts protected by MFA. This article explains what’s happening and outlines how to gain insight into who might be affected by the change.
Group-based licensing is a mechanism to make it easier to assign and manage product licenses for large sets of user accounts. In this article, we discuss how to use Microsoft Graph PowerShell SDK cmdlets to manage group-based license assignments in a Microsoft 365 tenant. Assigning licenses to groups is very much like direct assignments, but some differences exist.
A recent question asked how to force users to reauthenticate at 7AM every Monday. The solution seems to revoke access for user accounts. This article describes how to create an Azure automation runbook (PowerShell script) to find target accounts and revoke their access. By linking the runbook to an automation schedule, we can make sure that revocation happens at the desired time.
The Microsoft 365 Licensing Report PowerShell script has been upgraded to generate detailed license information and to deal with expired license subscriptions. You can download V1.94 of the script from GitHub. Before attempting to run the licensing report script, take the time to read previous articles to understand the basics of the script and how to generate the files used for pricing information.
The Microsoft 365 admin center will support continuous access evaluation (CAE) from September 2024 to help revoke access from accounts more quickly when critical events happen (like an account password being changed). Adding CAE support to an admin center is always a good idea, but it shouldn’t take away from the need to protect Microsoft 365 accounts with multifactor authentication. Stop compromise before you need to react to compromise!
Microsoft Purview and the Exchange Online Search-UnifiedAuditLog cmdlet both perform searches of the Microsoft 365 unified audit log. Both mechanisms support the concept of scoped searches to limit audit records returned by searches to the administrative units an account can manage. But the permissions assigned by the two mechanisms aren’t synchronized, which can lead to complications.
The decision to rationalize license management in the Microsoft 365 admin center wasn’t popular but the signs are that it could deliver benefits to customers in the form of new features and functionality. The first updates are a GUI to manage self-service purchases and trials together with notifications to administrators when a user makes a self-service purchase. More needs to happen, but positive indications are there.
Microsoft’s project to impose a mandatory MFA requirement for access to Azure management tools and sites will start enforcement on or after October 15, 2024. The new requirement will only affect administrator accounts who access Azure sites and tools (like PowerShell). Normal users shouldn’t notice any difference. The Azure MFA requirement is a great way to drive home the need for MFA to protect Microsoft 365 administrator accounts against attack. Prepare now!
The August 15 announcement that Microsoft Copilot (the version that doesn’t use the Graph) will benefit from enterprise data protection from September is good news. However, Microsoft said nothing about the security issues around Copilot for Microsoft 365 reported at the recent BlackHat USA 2024 conference. In other news, tenants can pin Microsoft Copilot to app navigation bars using a new control in the Microsoft 365 admin center.
The Usage Reports Graph API is now generally available, which means that it’s fully supported. In other news, a Graph API is available for Microsoft 365 Backup, The news demonstrates once again how widely the Graph APIs are used with Microsoft 365 and why tenant administrators should acquire some knowledge about how the Graph works.
Microsoft is removing license assignments from the Entra admin center. From Sept 1, new license assignments are done in the Microsoft 365 admin center. In other news, a new Self-service trials and purchases page is coming to the Microsoft 365 admin center to control the ability of users to purchase self-service licenses or use trial licenses.
Tenant administrators know that they need to deal with mailboxes and OneDrive accounts when people leave, but what about Teams chat messages? Or rather, the information stored in the compliance records captured in Exchange Online mailboxes? Reviewing chat messages can be an ardous task, so perhaps the solution might be to export the compliance records to a PST for long-term retention.
MC837081 announces that the Microsoft 365 admin center is to lose its ability to send password in email after updating a user account. It’s the right thing to do because sending passwords in email is bad practice and encourages people to treat passwords with less respect than they should. The long-term solution is to move away from passwords, but it will take time before Microsoft 365 is passwordless.
Microsoft plans to archive unlicensed OneDrive sites starting in January 2025. The obsolete sites will end up in Microsoft 365 archive, from where the sites can be reactivated for a small per-gigabyte fee. Archived sites are indexed and discoverable. However, the message is clear: remove unlicensed OneDrive sites now. They’re only cluttering up your digital landscape and might give Copilot for Microsoft 365 a headache.
The Microsoft 365 licensing report now supports a cost center analysis based on cost center values stored in an Exchange custom attribute. The new analysis is entirely optional, but it seems like many tenants store cost center values in custom attributes, so this update might work well for them. That is, if the cost center data stored in Exchange is accurate… Rubbish in always means rubbish out…
Every Microsoft 365 tenant must deal with ex-employee mailboxes. The default choice is to make the mailboxes into shared mailboxes. But inactive mailboxes could be a better option to deal with the requirements to preserve user privacy and avoid inadvertent disclosure of PII to people who don’t need that information. Perhaps it’s time to reassess how your organization deals with ex-employee mailboxes?
I dislike the Microsoft 365 self-service purchase mechanism and disable it in any tenant where I can. Global and Billing administrators for tenants that allow self-service purchases will soon receive notifications when self-service purchases occur to allow them to take action to allow, cancel, or change the purchased subscription. Or they can do what I do and avoid the problem in the first place by prohibiting self-service purchases.
A reader wanted to know why the Purview Compliance portal doesn’t show who last updated sensitivity label policies. The reason why is unclear, but what’s for sure is that Purview doesn’t record the data anywhere. But PowerShell and the audit log soon reveal who last made changes to labels and policies. It’s yet another example of how PowerShell fills gaps Microsoft leaves behind.
The Teams and Groups activity report is a popular script that helps administrators identify inactive teams and groups within a Microsoft 365 tenant. The script code has been developed over the years. The last version converted to Graph API requests to improve performance. This time, the upgrade is to use the Microsoft Graph PowerShell SDK to make the code easier to maintain.
V1.2 of the User Passwords and MFA report includes the names of authentication methods registered for user accounts. V1.3 expands the amount of detail reported for each method, such as the phone number used for SMS challenges, or the email address used for SSPR. It’s a small but important detail that’s useful to administrators. However, it also comes with a potential privacy issue, so the script must handle that too.
The Microsoft 365 Licensing Report is a popular PowerShell script that’s just been updated to V1.9 with a bunch of changes to highlight different aspects such as license costs for disabled user accounts and inactive user accounts. Copious use of some very dubious color choices makes the HTML report created by the script look very nice (if you’re color blind) and the new version can generate an Excel worksheet.
A Microsoft Graph update makes per-user MFA state available for user accounts. Being able to access the data means that we can include it in the User Passwords and Authentication report. You can now see if accounts are disabled, enabled, or enforced for per-user MFA along with all the other information captured about passwqrd changes, MFA authentication methods, and so on.
Microsoft is deploying additional audit events to tenants with Purview Audit (Standard) licenses. Among the 15 Teams events in the set are Teams meeting audit events to capture details of meetings and participants. Unhappily, some of the data that you’d like to have for meetings, like the subject, are missing. And meeting participant information is available for some classes of user but not for others.
A May 20 post contains the welcome news that the new audit events promised for Purview Audit standard customers should be available in June 2024. Some of these events are for Exchange Online, like the famous MailItemsAccessed event. Others are for Teams and SharePoint Online. In the case of Exchange, tenant administrators might have to do some work to validate that mailbox audit configurations are correct.