On Oct 14, 2025, Exchange 2019 and 2016 reach end-of-life and Exchange SE becomes the only supported on-premises Exchange server. In other news, we discuss Microsoft guidance for moving to cloud first identity, HVE and ECS and the extension of basic authentication support to September 2028, the introduction of auto-archiving for Exchange Online, and why Microsoft is deprecating the Contact object from Exchange Online.
This article explains how to use the Microsoft Graph PowerShell SDK to report Recoverable Items in a form that is usable for eDiscovery investigators and other highly-privileged use. The script fetches details of items found in folders like Deletions, Purges, Versions, and SubstrateHolds. Because accessing mailbox data is a sensitive action, consider restricting access to confidential mailboxes using RBAC for applications.
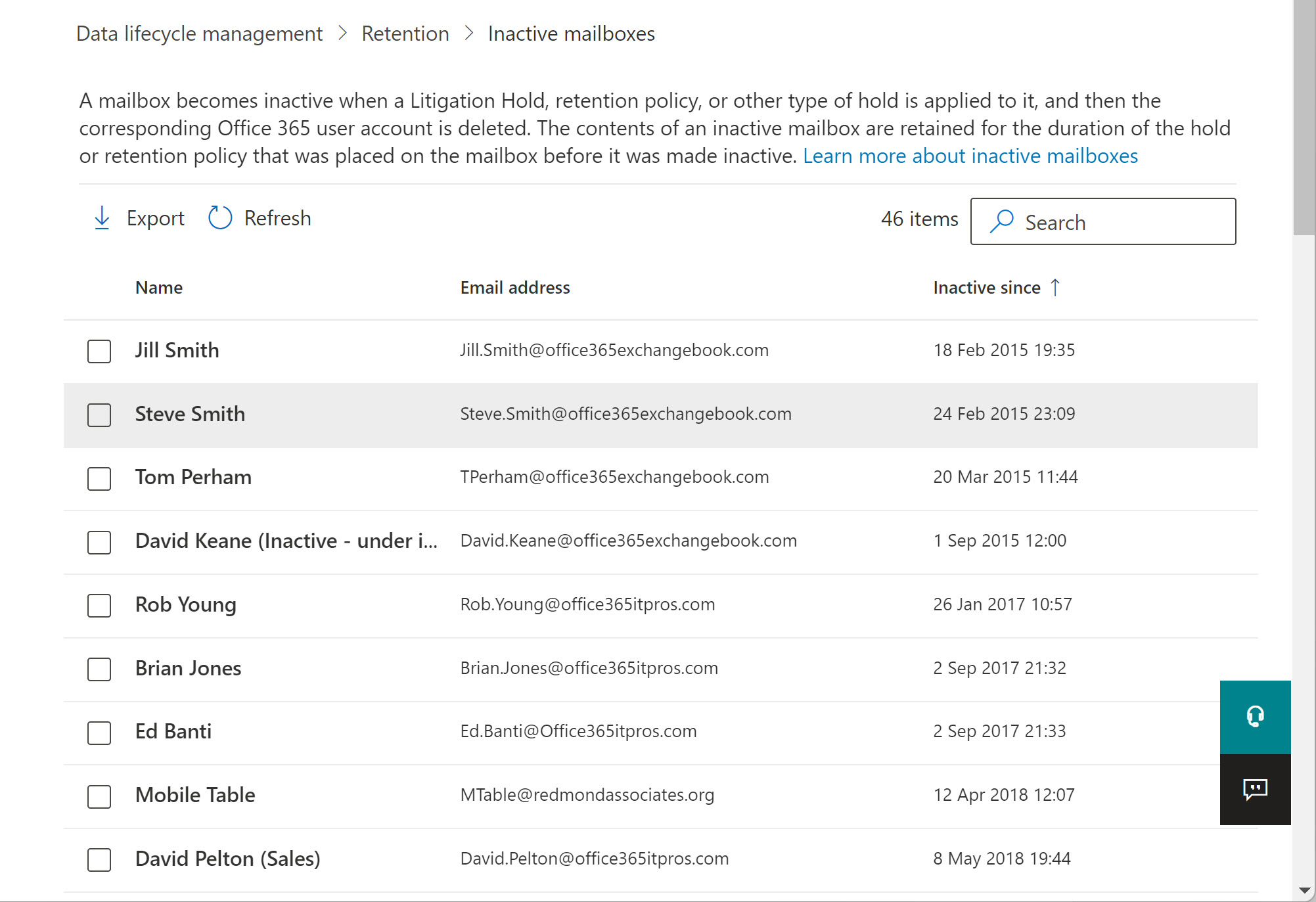
Microsoft plans to reduce the recovery period for inactive mailboxes newly released from retention holds and policies from 183 to 30 days. The change will be implemented worldwide by the end of September. The reduction in recovery time sounds seriously but it’s really not. If you haven’t figured out that you need to recover some data from an old inactive mailbox within 30 days, the data probably isn’t needed. And anyway, if you really want to, you can keep inactive mailboxes forever.
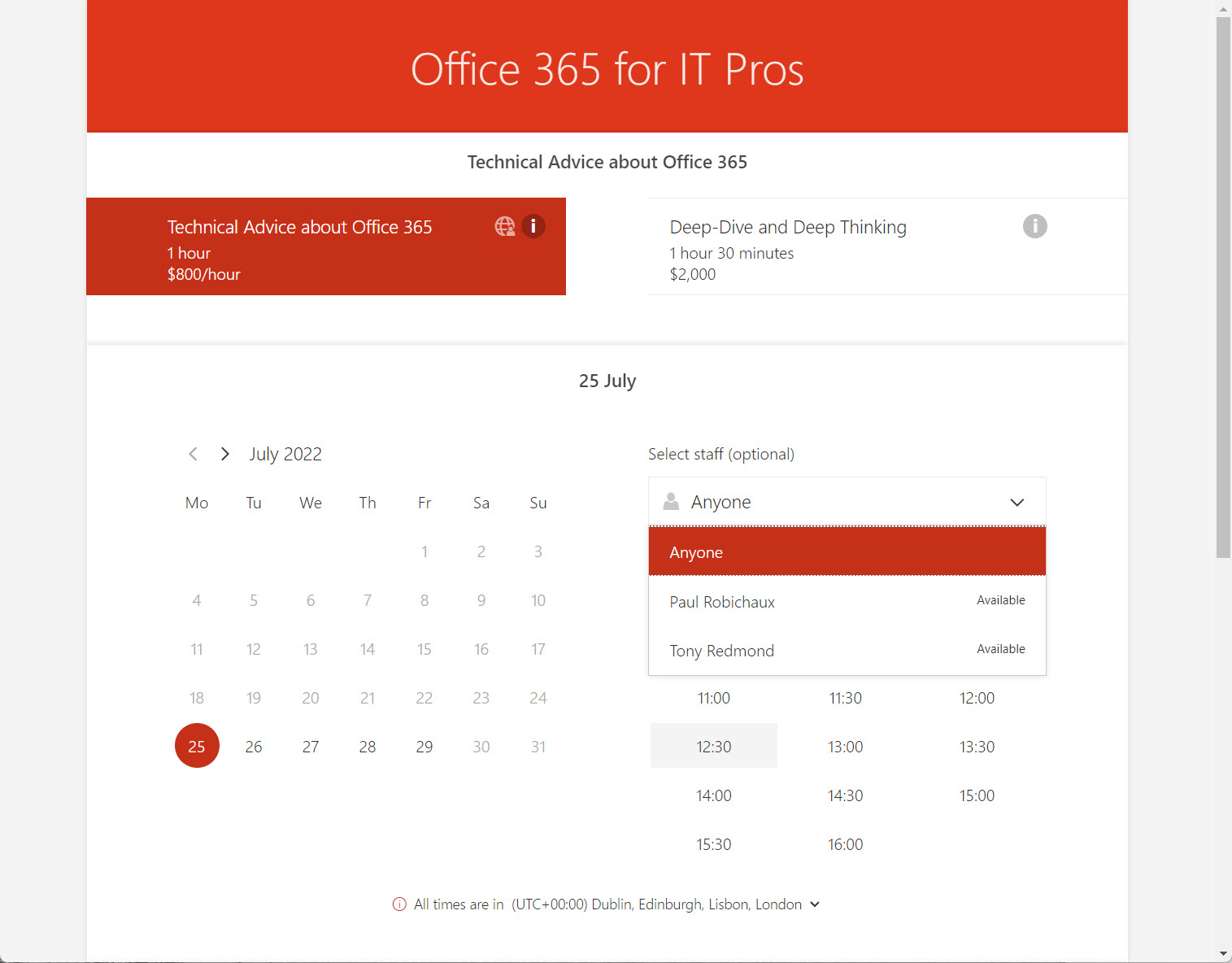
The Microsoft Bookings app is available to many Office 365 users. The app is designed to host a shared calendar for a group of people. The calendars are in special scheduling mailboxes that are created by the Microsoft 365 substrate. Appointments in the calendar can be scheduled by people through a bookings page, which can be on the internet or confined within an organization. It’s a neat way to run an online business – if only Bookings could take in some money for all that scheduled work.
Exchange Online tenants have a choice between inactive mailboxes and shared mailboxes when the need arises to keep “leaver” data like that belonging to ex-employees. Inactive mailboxes are essentially a compliance tool and sometimes shared mailboxes are better choices. We explore both in this short article.
A reader asked if it’s possible to use PowerShell to return the unread count for the Inbox folder in user mailboxes. The standard Exchange Online PowerShell cmdlets tell you a lot about mailbox folder statistics, but they can’t look inside a folder. But the Microsoft Graph APIs can, so a combination of PowerShell and the Graph deliver a solution to the problem.
Exchange Online plans to change the format of the Name and Distinguished Name mailbox properties. The idea is to make these properties unique and improve synchronization with Azure AD. It all sounds like a good idea, but these properties have been around in Exchange for a long time, and any change will surface in unexpected places – like the output of many Exchange cmdlets. Which is why Microsoft has paused the plan for further reflection.
A management request came in to report email sent by some users to external recipients. Although you might not agree that this is the right thing for any organization to do, it’s very possible by exploiting the message trace information retained by Exchange Online for 90 days. As a bonus, we email the report generated from message tracing data to the requesting manager. Isn’t PowerShell just wonderful?
Planner now creates digital twins (copies) of tasks in user mailboxes in Exchange Online to make data available for eDiscovery and compliance. Storing items in the Microsoft 365 substrate is the same approach to making data available for search and compliance as taken by Teams and Yammer.
Every Exchange Online tenant has four mailbox plans. Exchange uses the plans to populate some important mailbox settings based on the license assigned to the mailbox owner. This article explains the four mailbox plans, how to update the plan settings, and some of the things you can’t do with mailbox plans. We also include some PowerShell to report the mailbox plans assigned to users in your Office 365 tenant.
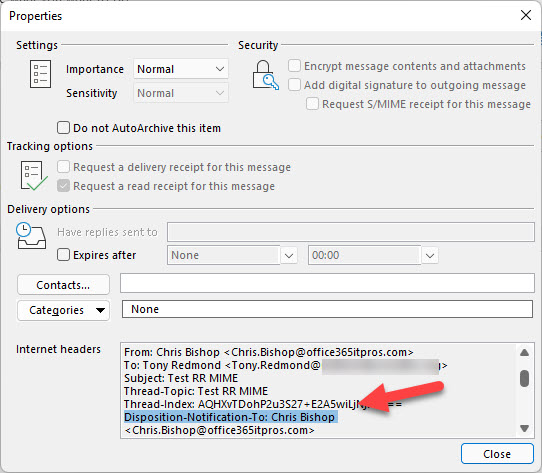
A reader request asked how to force users to send read receipts. This is a client-side feature so the settings involved differ from client to client. We explore how to control them in OWA and Outlook for Windows. A mixture of PowerShell and system registry settings help create a solution. We’re leaving figuring out how to manage other clients to our readers.
A 1.5 TB limit applies to Exchange Online archive mailboxes from November 1, 2021. In this article, we use PowerShell to report how close expandable archives are to the new limit. In reality, not many archive mailboxes will approach the new limit, but it’s nice to know things like the daily growth rate for an archive and how many days it will take for an archive to reach 1.5 TB. All whimsical stuff calculated with PowerShell!
Inactive mailboxes have been available in Exchange Online since 2015. A new inactive mailboxes listing is available in the Microsoft 365 compliance center. The GUI isn’t very functional, but perhaps it’s a starting point for some enhanced management capabilities for inactive mailboxes. We’ve only been waiting six years…
Microsoft wants to eliminate the Search-Mailbox cmdlet, but it’s still very valuable when the time comes to remove mailbox items because of a spam attack or similar reasons. The suggested replacement is Core eDiscovery searches and associated content search purge actions, but these are slower and less effective than Search-Mailbox. To prove the point, we’ve put together a demonstration script to show how to compose a search query and run it against a set of mailboxes.
A reader asked how to move membership of multiple distribution lists from one mailbox to another. We use PowerShell to do the job. Only a few lines are needed to switch the memberships, but we add a few more lines to make the script work better. We don’t handle dynamic distribution lists. This is possible for precanned (simple) filters, but given the number of dynamic distribution lists usually involved, it’s probably best to update directory settings manually.
Exchange Online assigns large mailbox quotas to users. These quotas are needed to cope with the volume and size of modern email. What used to take 2 KB in 1996 now consumes 60 times more. And while email is more graphical and prettier to look at, you’d wonder if the value of the actual content has changed much, if at all.
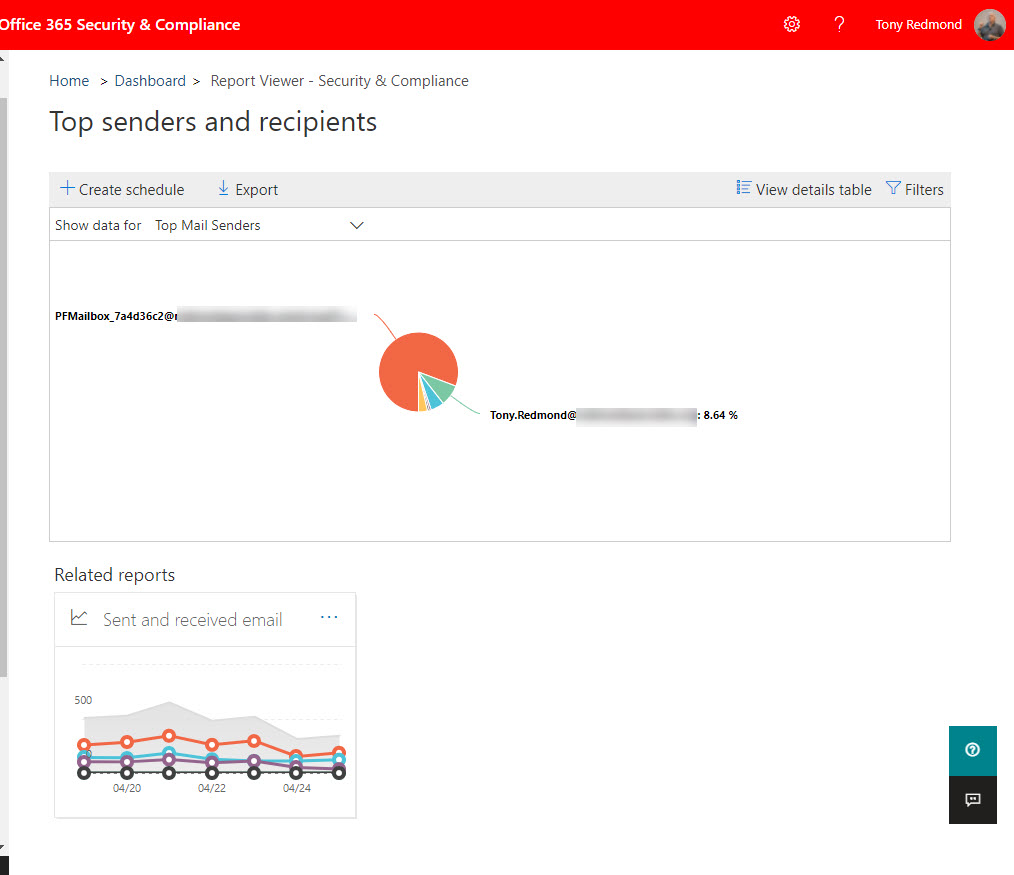
For whatever reason, Microsoft decided to cancel plans to remove the Top Senders and Recipients report from the SCC, citing customer feedback as the reason. The thing is that the SCC report and its underlying cmdlet use an old data source. The Microsoft Graph Reports API is the modern approach and an adequate replacement usage reports is available in the Microsoft 365 admin center. I really can’t understand why anyone would want to keep the old report as it’s not very good at all.
Exchange Online supports the ability to send email using any SMTP proxy address assigned to a mailbox. Following the announcement of the feature, users had many questions including what clients can be used. Here are some common questions and answers about the feature, including some PowerShell to report the set of proxy addresses assigned to user mailboxes.
Microsoft wants to retire the Search-Mailbox cmdlet from Exchange Online. But while the cmdlet available, it does a great job of removing mailbox items. If you get the search query right! In this example, we explain how to write a script to clear out calendar items from the mailboxes of multiple users.
Exchange Online indexes the items stored in mailboxes. Some of the items are partially indexed, meaning that not all of their content is indexable. Microsoft has a PowerShell script to analyze the number of partially indexed items found in mailboxes. The output is kind of esoteric, so we worked it over to create something more understandable.
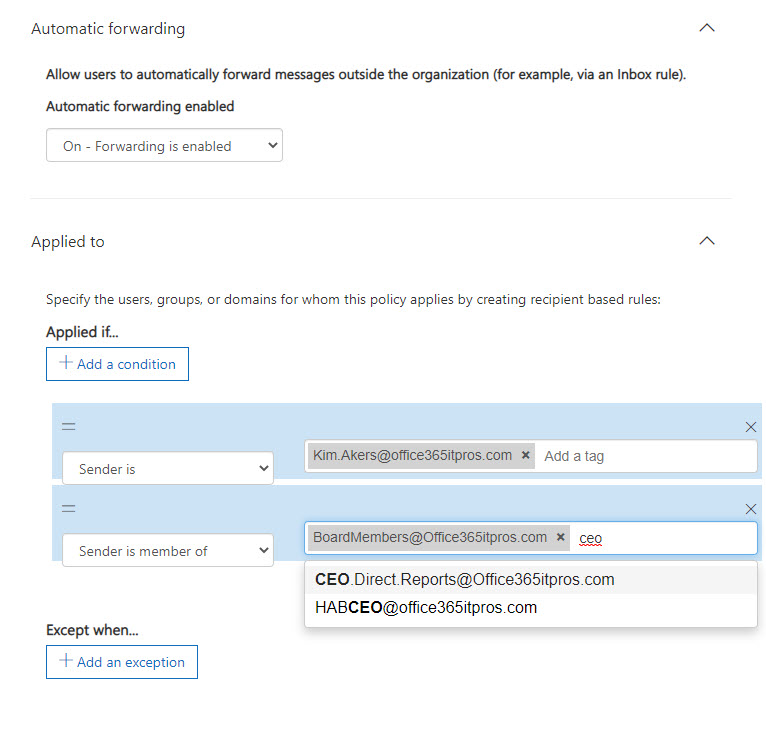
Microsoft has updated the Exchange Online outbound spam filter policy to stop automatic forwarding of email from user mailboxes. The change is now effective with the default set to block automatic forwarding. You can create a custom policy and apply it to selected mailboxes and distribution lists if they need to forward email.
Exchange Online supports dynamic distribution lists, a great way to address sets of recipients found by resolving a filter against the directory. In this example, we explore how to create a dynamic distribution list to address mailboxes marked as preferring a specific beverage. It might even be useful some day!
Exchange Online Protection (EOP) quarantines suspicious messages to stop spam, malware, and phishing email arriving into Exchange Online inboxes. Administrators can review quarantined messages. Reviewing messages can find some problems, like messages that shouldn’t have been stopped. But reviews take time, and sometimes other stuff gets in the way, which means that quarantined messages expire without anyone ever asking the question “why.”
Characterizing backup of Exchange Online mailboxes to PSTs as brain-dead might have been harsh, but it’s an accurate assessment of the worth of this idea. Plenty of cloud-based backup offerings exist that can process Exchange Online data more securely and at scale. If you want to backup Office 365, stay away from PSTs and use a different product, after asking some questions to ensure that the backups deliver the value you expect.
Exchange Online Protection monitors email traffic in and out of Office 365 tenants. When a mailbox exceeds limits, it might end up being restricted, such as in the case when the mailbox might be compromised. We tried to find out when Exchange Online Protection restricted mailboxes and what to do afterwards. Here’s what we discovered.
Many migration projects use Exchange Web Services (EWS) to move data to Exchange Online. EWS is using throttled to preserve resources. Here’s how to lift the restrictions for up to 90 days, all without going near a support call.
I’ve written many articles to explain how to use the Office 365 audit log to report different aspects of the platform. But taking action is much better than just reporting. In this post, we explain how to take a report generated from the Office 365 audit log and use it to drive some actions. In this case, removing the SendAs permission from people who aren’t using it.
Exchange Online mailboxes support SendAs, Send on Behalf Of, and FullAccess permissions. A previous script focused on the FullAccess permission. This version covers all three. It’s also a good example of how you need to pay attention to property sets when writing PowerShell code to use the new Exchange Online REST-based cmdlets.
In addition to mailbox permissions, Exchange Online supports folder-level delegated permissions. Users can create folder delegations through Outlook desktop. Like mailbox permissions, it’s a good idea for tenants to check folder-level delegations to ensure that people don’t keep permissions for longer than they should. We explain how to create a PowerShell script to generate such a report.
Exchange Online makes it easy to assign delegated permissions for user and shared mailboxes. But permissions assigned to people might not be still necessary, so it’s good to do a periodic check. In this post, we describe a script to scan for permissions on Exchange Online user and shared mailboxes and highlight non-standard permissions in a report generated as a CSV file.
Exchange Online enables mailbox auditing by default, which should mean that audit events get to the Office 365 audit log for all E3 and E5 mailboxes. Well, that’s what you might thing but that’s not what happens. Mailbox events for E5 mailboxes arrive just fine, but you must reenable E3 mailboxes for auditing before their events flow. It’s a bizarre situation.
Microsoft has released information about high-value Office 365 audit events and audit event retention policies. Both are part of a Microsoft 365 Advanced Audit offering. The MailItemsAccessed event is the first high-value audit event (we can expect more) and the retention policies are used to purge unneeded events from the Office 365 audit log.
Outlook Mobile now supports delegate access to Exchange Online mailboxes. By granting fuil access to a delegate, they can open and work with a mailbox, and send messages using the SendAS or SendOnBehalfOf permissions. The new feature underscores the advantage Outlook mobile enjoys over other mobile Office 365 email clients.
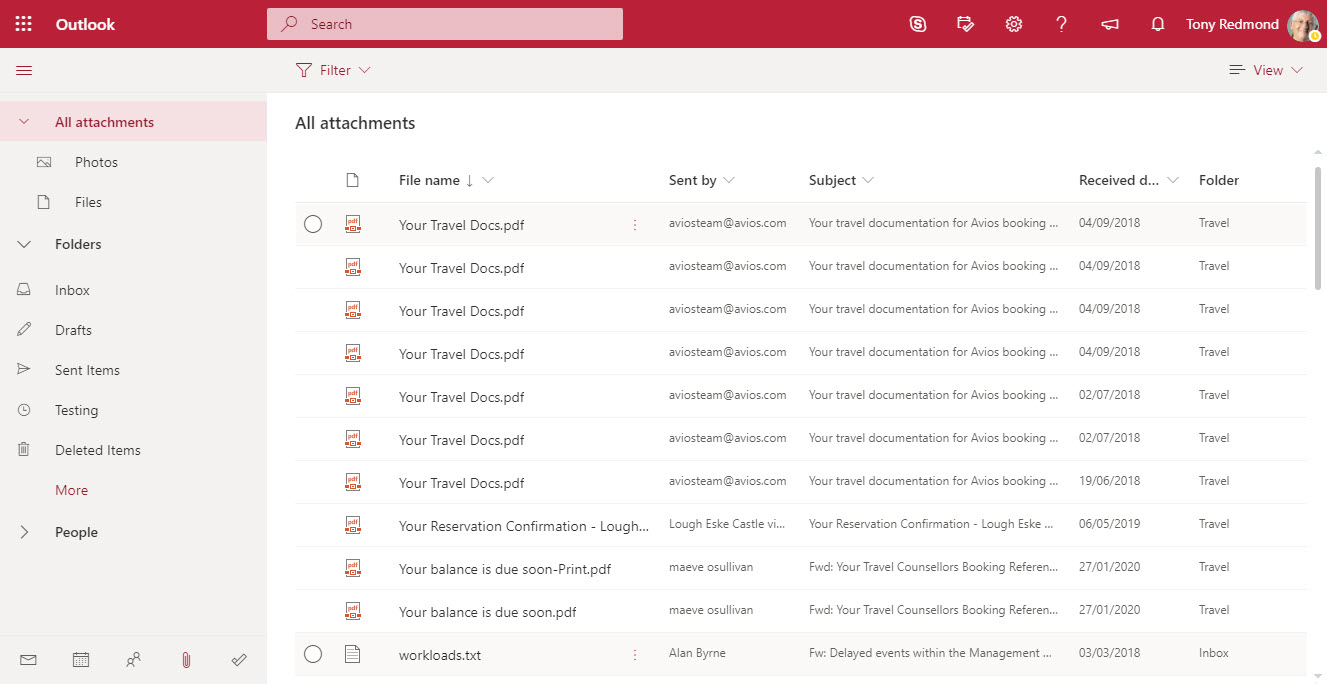
OWA now includes Files in its “module switcher”). The new module allows fast access to attachments stored in any folder in an Exchange Online mailbox. It’s a neat feature that will please many people simply because it makes finding often-elusive attachments just that bit easier.
Exchange Online now supports a custom recipient limit for mailboxes of between 1 and 1000. The limit controls the maximum number of recipients a mailbox can add to a message. Think of the fun you could have by setting the recipient limit on manager mailboxes to something small, like 6….
Some Exchange Online mailboxes are quite small (2 GB for frontline users). Tenant administrators might want to monitor mailbox usage to make sure that quotas aren’t unexpectedly exhausted. This post explains how to use a PowerShell script to calculate the percentage of mailbox quota used and highlight the problem if a threshold is passed.
Microsoft has announced that basic authentication for multiple email connection protocols won’t be supported after October 13, 2020. You won’t be able to connect with EWS, EAS, IMAP4, POP3, or Remote PowerShell unless you use modern authentication. There’s just over a year to prepare, but there’s some work to be done.
Microsoft is now rolling out MyAnalytics access to Office 365 accounts with an Exchange Online license.The first sign that anyone gets is when they receive one of MyAnalytics’s well-intended messages to help them organize their work life smarter. Funnily enough, some people don’t like the idea of Office 365 analyzing and reporting their work habits, which is why you might need to disable MyAnalytics for some mailboxes.
Microsoft has confirmed that disconnected Exchange Online mailboxes are not included in the sources scanned by Office 365 content searches, thus clearing up some misunderstandings that might have existed in the field. The bottom line is that if you want to search mailboxes that don’t belong to accounts, you should use inactive mailboxes.
Exchange Online allows users to add personal retention tags to their maiboxes through OWA settings. Some organizations don’t like this, so they can deploy user role assignment policies to block the feature. It;s something that you could consider doing if you’re preparing to switchover to Office 365 retention policies to impose the same retention regime across multiple workloads.