Table of Contents
Blog Post, Roadmap Item, but No Notification
On July 28, Microsoft announced they had upgraded the Microsoft 365 admin center to make it easier for tenants to manage the default Exchange Online authentication policy. Authentication policies were introduced in October 2018 to enable granular (account level) management of basic authentication for the connection protocols for Exchange Online.
The change fulfils Microsoft 365 roadmap item 65007. No notification was posted in the message center in the Microsoft 365 admin center as Microsoft chose to post a blog instead. While appreciating the popularity of the EHLO blog with the Exchange community, it would still have been better if Microsoft posted a notification too to allow tenants to track change more effectively, especially by synchronizing update data through the link between Planner and the message center.
Org-wide Settings
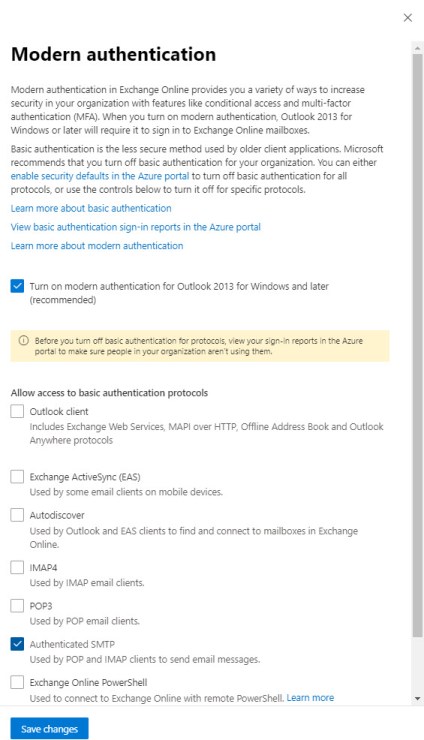
Microsoft has updated the Modern authentication settings available in the Org (organization) settings section of the Microsoft 365 admin center. Instead of just one setting (to turn on modern authentication for Outlook clients), settings are available to control access to basic authentication for the connectivity protocols covered by authentication policies (Figure 1).
What’s Updated by the Microsoft 365 Admin Center
If you’ve never used authentication policies in the past, changing settings in the admin center will create a default authentication policy and update the organization policy to register the policy. You can check if a default authentication policy is in place by running the Get-OrganizationConfig cmdlet:
Get-OrganizationConfig | Select DefaultAuthenticationPolicy DefaultAuthenticationPolicy --------------------------- No Basic Auth
In this case, we can see that the default authentication policy is called “No Basic Auth”; this policy is assigned automatically to Exchange Online accounts unless it’s overridden by an explicit assignment using the Set-User cmdlet (learn how in this post).
Need to Manage Non-Default Authentication Policies
If your tenant has defined authentication policies, changes made in the Microsoft 365 admin center only affect the default policy. Any other policies remain unchanged. For instance, my tenant has two policies. The default policy disables basic authentication for all connection protocols while another allows basic authentication for PowerShell, which is still needed in some circumstances until organizations can switch over to certificate-based authentication for batch jobs. This policy is assigned to specific accounts.
When we run Get-AuthenticationPolicy to see what policies exist, the WhenChanged property reveals that only the default policy was updated:
Get-AuthenticationPolicy | Format-Table Name, WhenChanged
Name WhenChanged
---- -----------
No Basic Auth 29/07/2020 23:20:03
PowerShell Basic Auth 22/03/2019 01:40:02
What’s obvious from this is that you still need to manage non-default authentication policies with PowerShell.
Authentication Policies and Conditional Access
Authentication policies only apply to Exchange Online and work for all Exchange Online licenses. They complement conditional access policies, which are a more comprehensive method to insist on modern authentication connectivity across Microsoft 365.
In fact, authentication policies have a great advantage over conditional access policies in that they block attacker attempts to connect using basic authentication. Conditional access policies are processed post-authentication, so an attacker has already managed to compromise an account at this point. Another thing to remember is that conditional access policies require Azure Active Directory Premium P1 licenses, which some organizations do not have for all or some accounts.
Moving Forward Towards Modern Authentication
Weaning people off basic authentication is a long process. It’s an essential step towards better security by closing off routes taken by attackers to compromise accounts (read this post if you’re in any doubt on this point). Microsoft has a plan to remove basic authentication from Exchange Online by the end of 2022. Small steps like making it easier for tenant administrators to manage default authentication policies help, but the big challenges remain: updating old clients, updating hardware devices that connect to Exchange, and user education. We’ve still got work to do.
The move to modern authentication is a great example of how things change in the cloud. It’s important to have all the facts to help guide your journey from basic authentication. Subscribe the Office 365 for IT Pros eBook to learn from our experience!
2 Replies to “Microsoft 365 Admin Center Manages Default Authentication Policy for Exchange Online”