Microsoft has delayed the retirement of basic authentication for the SMTP AUTH client submissions protocol to 2027 or beyond. New tenants will be the first to be blocked and Microsoft will disable basic authentication for SMTP AUTH in a way that existing tenants can reenable the protocol. Eventually, we’ll get a date for final retirement sometime in 2027. These things take time!
Now that October 1 has arrived, Microsoft has started the process to permanently remove basic authentication from 7 email connection protocols. So what happens next? Well, for many organizations, not much. They’re the ones that have already transitioned to modern authentication. For others, some unpleasant surprises might lie ahead as people discover that stuff just doesn’t work anymore.
Microsoft revealed some interesting Exchange Online statistics at the MEC 2022 event. 300 K physical mailbox servers is a staggering amount, but 7.3 billion mailboxes might be even more surprising. Also at MEC we discovered more about the campaign to remove basic authentication from Exchange Online and how well Microsoft’s Greg Taylor can communicate in Irish when he presents about the deprecation of basic authentication.
The upcoming removal of support for basic authentication in seven Exchange Online connectivity protocols could mean trouble for some Office 365 tenants if they don’t take care to ensure that modern authentication is used for PowerShell connections. The old-style Remote PowerShell connection must be replaced with the Connect-ExchangeOnline cmdlet from the Exchange Online management module (aka the V2 module). Apart from anything else, this should improve the performance and robustness of scripts, especially after Microsoft finishes the work to remove the WinRM dependency for older cmdlets.
October 1, 2022, is when Microsoft begins the final process of removing support for basic authentication for 7 email connection protocols from Exchange Online. The process will take several months to complete, and when it’s done, Office 365 will be a safer place that attackers will find more difficult to penetrate. But it’s time for tenants to prepare, if you haven’t already done so, and we highlight some critical points from Microsoft’s most recent post on this topic.
Microsoft is removing TLS 1.0 and 1.1 from Microsoft 365. This has been well flagged, but tenants might not understand the impact on PowerShell scripts which send email using the Send-MailMessage cmdlet and SMTP AUTH. In a nutshell, unless you force PowerShell to use TLS 1.2, attempts to send messages via Exchange Online will fail. It’s time to check those scripts and ,consider how to move away from SMTP AUTH and Send-MailMessage.
The road to modern authentication for Exchange Online is littered with things to do. One action item is to check Apple iOS and iPad devices using Exchange ActiveSync to connect to mailboxes. If these devices were configured to connect to Exchange Online before iOS 12, they’re likely using basic authentication. Right now, the only way to move them to modern authentication is to remove Exchange from the mail app and add Exchange again. It’s a bump on the way to modern authentication in October 2022.
Last week’s announcement that Exchange Online will block basic authentication for multiple protocols on October 1, 2022, got some attention. Now the hard choices of what to do with clients and applications need to be made. To smoothen the path to remove basic authentication, Microsoft is making an exception for SMTP AUTH. Your scripts and multi-function devices will keep working after October 2022, but the writing is on the wall and eventually even SMTP AUTH will stop working.
October 1, 2022 will be a big day for Exchange Online tenants because that’s when Microsoft starts to disable basic authentication for connectivity protocols whether or not tenants want this to happen. This is a huge and fundamental change that’s being driven by the need to increase the overall security of Exchange Online and individual tenants, while also blocking common attacks seeking to compromise user accounts. With only a year to go, it’s time to start work on preparing everything that needs to be in place for the great October 1 switchoff.
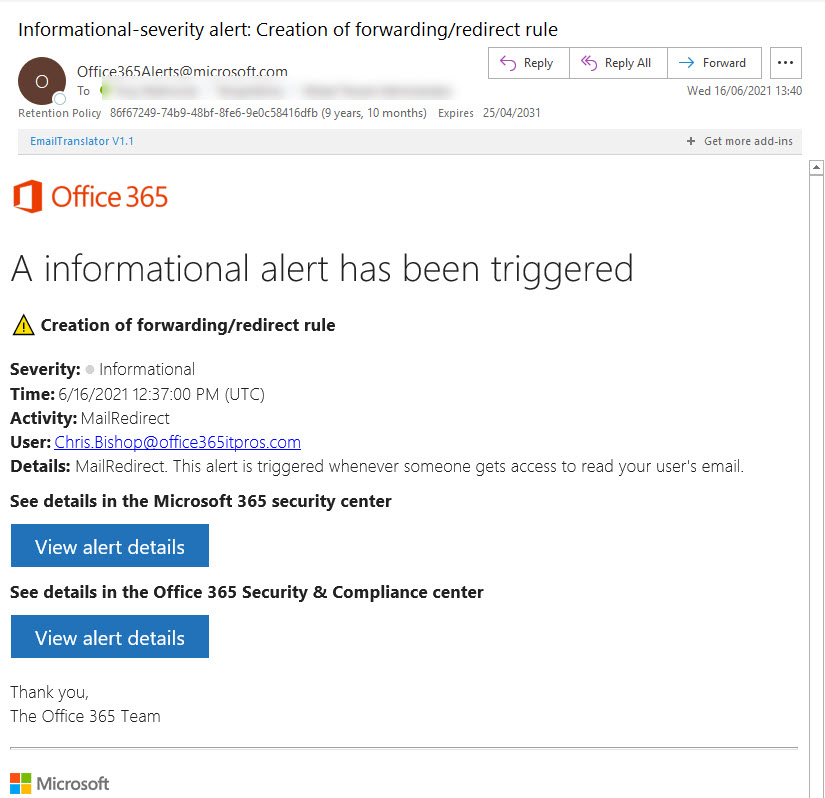
The need to remove basic authentication from Exchange Online is underlined by a June 14 report from the Microsoft Threat Intelligence Center pointing to how attackers compromise mailboxes using antiquated protocols like POP3 and IMAP4 to connect to accounts which don’t use MFA. After accounts are penetrated, the attackers plant inbox rules to forward copies of interesting messages and use the information received to plan and execute business email compromise attacks. Tenant administrators still have some work to do to secure Exchange Online and Azure AD…
Microsoft wants to remove basic authentication from Exchange Online connection protocols. But pressures have forced Microsoft into a new strategy and away from the mid-2021 date for deprecation of basic authentication for five protocols. Instead, Microsoft will disable basic authentication for protocols where it’s not used, include four addition protocols in its target set, and pause action for tenants where basic authentication is in active use. When they restart, Microsoft will give tenants 12 months’ notice that basic authentication will be blocked for a protocol. You can argue that Microsoft should have pressed ahead with their original plan, but would widespread disruption of service be worth the benefit gained from blocking vulnerable protocols? Balancing risk versus reward is often not easy.
The Microsoft 365 admin center includes the ability to manage settings for the default Exchange Online authentication policy. You might have other policies to allow selective access with basic authentication to some protocols; these policies must be managed with PowerShell. Authentication policies are part of the journey to eliminate basic authentication from Exchange Online, now expected to happen in mid-2021.
The combination of Exchange Online and PowerShell allows Office 365 admins to send messages for all manner of reasons. These scripts depend on SMTP AUTH connections and change is coming in this area with the deprecation of basic authentication. It’s a good idea to take an inventory of scripts that send email, including those that use the .NET classes to do the job.
Covid-19 dealt a blow to Microsoft’s plans to remove basic authentication from 5 connection protocols for Exchange Online and forced them to postpone the removal from October 13, 2020 to sometime in the second quarter of 2021. The news is disappointing because basic authentication is a weakness exploited by many hackers. But you can’t plan for a pandemic and Office 365 tenants need more time to be ready for the deprecation.
Azure Active DIrectory is getting a slimmed-down background image to help with bandwidth-constrained locations. Office 365 tenants with custom backgrounds won’t see the change. Customizing the appearance of the sign-in screen is easy if you prepare. And to finish up, we have pointers to a set of videos about how Azure Active Directory authentication works.
Some doubt that Exchange Online will disable basic authentication for five email connection protocols in October 2020. The refrain is that it will be too hard for customers. Well, it might be hard to prepare to eliminate basic authentication, but if you don’t, your Office 365 tenant will be increasingly threatened by attacks that exploit known weaknesses.
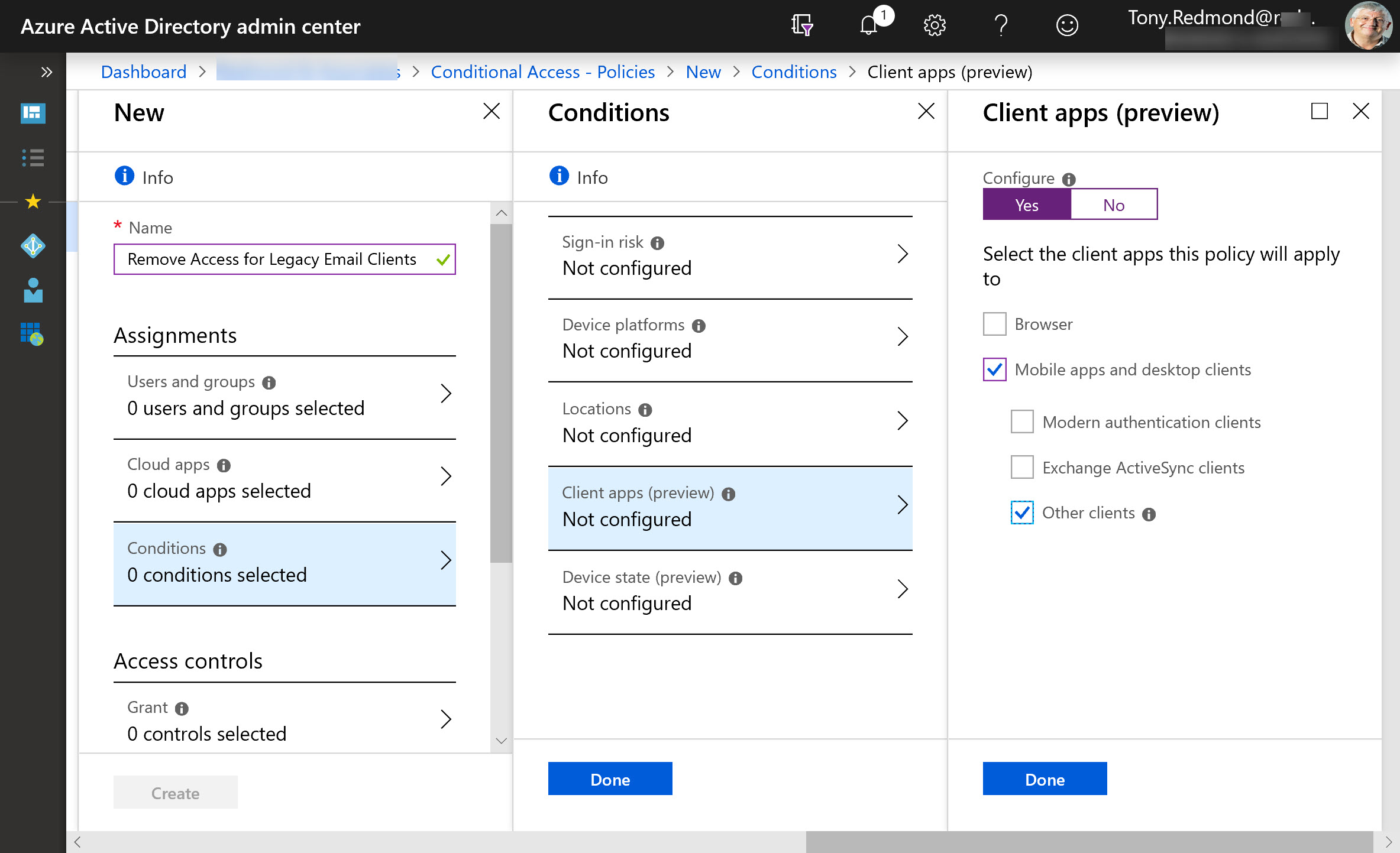
Microsoft plans to disable basic authentication for five Exchange Online connection protocols on October 13, 2020. They’ve been clear on this point for several months and are now moving to deliver tools and provide guidance about what people should do about clients that use basic auth connections with Exchange Web Services, Exchange ActiveSync, IMAP4, POP3, and Remote PowerShell. Work is needed to make sure that clients are prepared for the switchover to modern authentication.
Microsoft has announced that basic authentication for multiple email connection protocols won’t be supported after October 13, 2020. You won’t be able to connect with EWS, EAS, IMAP4, POP3, or Remote PowerShell unless you use modern authentication. There’s just over a year to prepare, but there’s some work to be done.
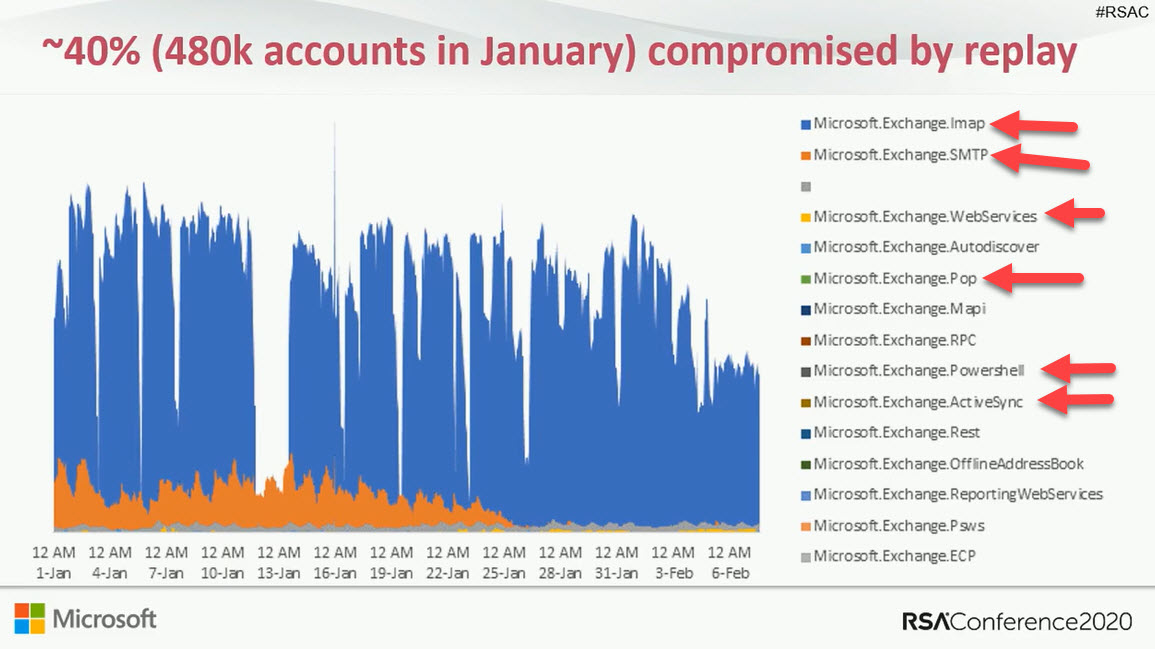
Exchange Online protocol authentication policies control what protocols a user can connect to mailboxes with, but it would be much better if we didn’t have to worry about some old and insecure protocols. Azure Active Directory gives Office 365 tenants the chance to clamp down on IMAP4 and POP3 connections and close off some of the holes that attackers try to exploit. Microsoft says that this can lead to a 67% reduction in account compromises, so that’s a good thing.
Microsoft has released a preview of the cmdlet set to allow tenants to create and manage protocol authentication policies for Exchange Online. It’s a great chance to disable basic authentication and reduce the attack surface for password spraying.