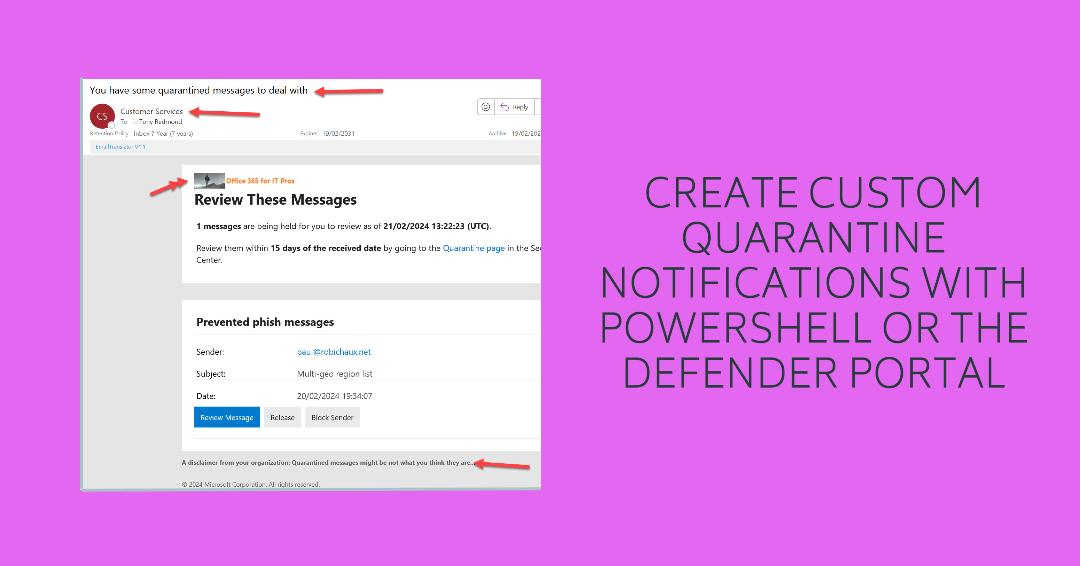
This article describes the experience of creating a custom quarantine message for Exchange Online Protection to send to those with email held in quarantine. The Microsoft Defender portal allows administrators to create custom settings for up to three languages. My initial attempts failed, but then something happened and all is well. It could just be the difference between English and English…
The Office 365 for IT Pros team welcomes Michel de Rooij as a new author. As a PowerShell Pro, he’ll like the code to update the impersonation protection list for anti-phishing policies. Or maybe he’ll rewrite it to make the code better. Either way, we win and the Mail Flow chapter should get a new lease of life.
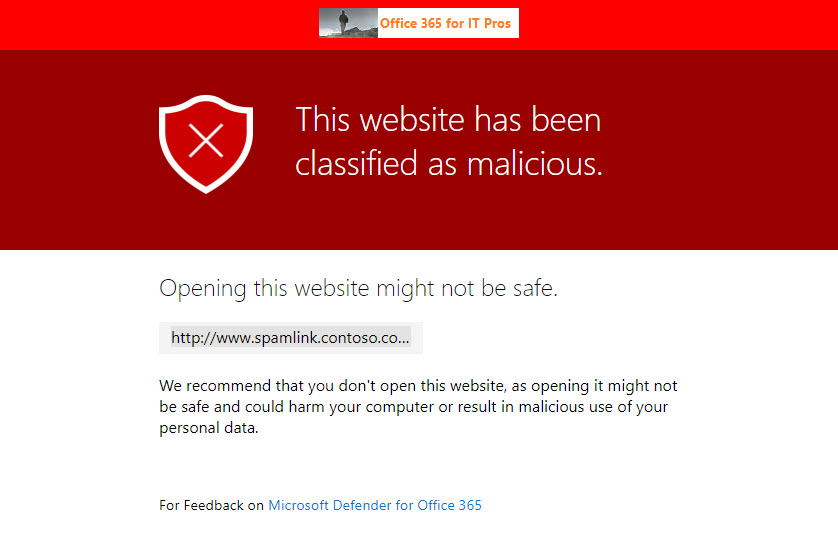
The Safe Links capability in Microsoft Defender for Office 365 is now generally available to protect Teams messages in chats and channel conversations, and even in web site links pinned as a channel tab. Most bad links flowing into an Office 365 tenant will continue to arrive by email, but this new capability closes off a gap where users are tempted to make a poor decision to share a malicious link through Teams.
A new phishing attack is circulating from an Office 365 tenant. The attack attempts to lure recipients into clicking a link to download a document. The phishing email is not quite as crude as other attempts and might lure users into doing the wrong thing, especially as the message is delivered to inboxes.
Exchange Online Protection (EOP) and Microsoft Defender for Office 365 support anti-phishing policies which generate safety tips for users. The first contact safety tip warns users when they receive email from someone they don’t usually get messages from. It’s a way to put the recipient on their guard, just in case it’s someone trying to impersonate someone else whom the recipient actually knows.
A change due in December will improve how Exchange Online Protection suppresses high confidence phish messages and stop them being delivered to user mailboxes. The old-fashioned allowed sender and allowed domain lists are being taken out of the equation and ignored when EOP is sure that it’s dealing with some high-confidence phish. It’s time to check your anti-spam policies.
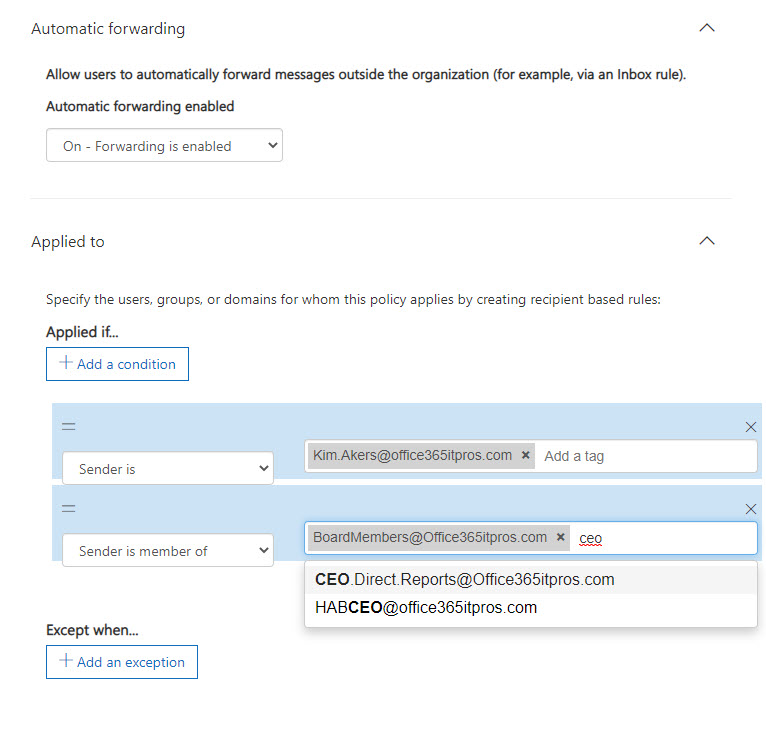
Microsoft has updated the Exchange Online outbound spam filter policy to stop automatic forwarding of email from user mailboxes. The change is now effective with the default set to block automatic forwarding. You can create a custom policy and apply it to selected mailboxes and distribution lists if they need to forward email.
A crude phishing attempt based on voicemail notifications from a VoIP service arrived in mailboxes. It’s easy for experienced users to pick up signs to stay away, but the unwary can be trapped. Report samples of phishing attempts to Microsoft to make Exchange Online Protection better and keep on educating users.
Exchange Online Protection puts problem messages into quarantine if it suspects that they contain spam, malware, or a phishing attempt. Instead of using the Security and Compliance Center GUI to work with quarantined messages, you can analyze details of quarantined messages with PowerShell to create some basic statistics and find messages that should be released.
Exchange Online Protection (EOP) quarantines suspicious messages to stop spam, malware, and phishing email arriving into Exchange Online inboxes. Administrators can review quarantined messages. Reviewing messages can find some problems, like messages that shouldn’t have been stopped. But reviews take time, and sometimes other stuff gets in the way, which means that quarantined messages expire without anyone ever asking the question “why.”
Exchange Online Protection monitors outbound email to pick up signs of potential compromise in Office 365 tenants. This can lead to EOP restricting a tenant’s ability to send outbound email and force the administrators to check for compromised accounts or connectors and other problems before contacting Microsoft Support to ask them to lift the restriction.
Exchange Online Protection monitors email traffic in and out of Office 365 tenants. When a mailbox exceeds limits, it might end up being restricted, such as in the case when the mailbox might be compromised. We tried to find out when Exchange Online Protection restricted mailboxes and what to do afterwards. Here’s what we discovered.
Office 365 users might receive a phishing attempt to say that they’ve just been paid by a UK healthcare group. The message shows some obvious signs to tell the recipient that it only contains trouble, but these signs are easier for humans to pick up than they are for machine learning. The combination of good message hygiene and user education should be enough to deflect phishing attacks.
ORCA is a project to help Office 365 tenant administrators validate their anti-spam and anti-malware settings against recommendations from Microsoft. ORCA is installed as a PowerShell module with just one cmdlet. After running Get-ORCAReport, you’ll have a report containing recommendations and observations about your configuration.
The fight against spam and malware goes on unabated. ZAP, or zero-hour auto purge, is an Exchange Online Protection (EOP) feature that’s getting some extra features to deal better with spam and phish malware. New policy controls are available to control the feature.
The Office 365 E5 plan includes Advanced Threat Protection (ATP), which builds on the anti-malware capabilities of Exchange Online Protection. ATP the includes Safe Attachments and Safe Links features, both of which can delay email delivery. I don’t notice the delay but others do. In any case, the more protection you have against malware, the better.
No one likes getting spam. Although EOP generally does a good job, Office 365 users can help themselves and help others by reporting spam that gets through to their mailboxes using Outlook’s Report Message add-in. And if they’d like someone else to report bad mesages, admins can do so through the Security and Compliance Center.