Shared mailboxes might need Microsoft Defender for Office 365 licenses, but how do you identify how many licenses? We use PowerShell to do the job by analyzing external email sent to shared mailboxes. If a mailbox receives external email, then by definition the mailbox receives benefit from MDO, and that’s the test for requiring a license.
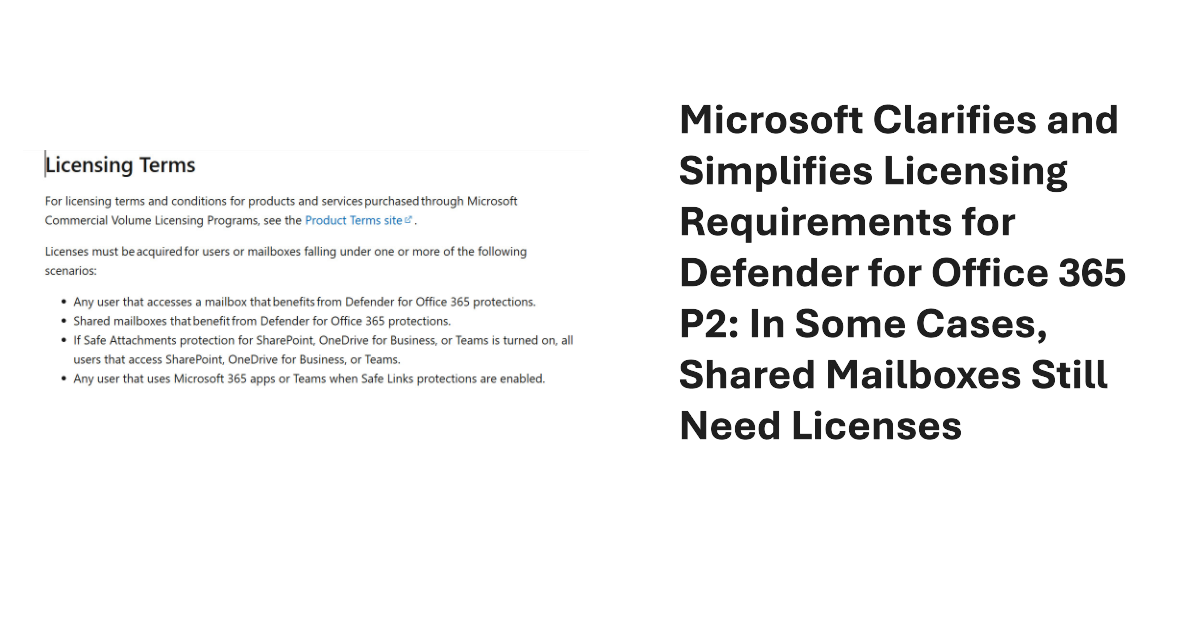
Some inconsistencies in the MDO P2 service description and licensing terms exposed a need for tenants to license every user and shared mailboxes. Microsoft has changed the service description and licensing terms to make them simpler. Mailboxes still need MDO licenses, but only if they benefit from MDO protection, including MDO P2 if that’s what they use. Tenant admins have some extra work to do to deploy policies. All explained here.
Microsoft Defender for Office 365 (MDO) requires shared mailboxes to be licensed but doesn’t extend the same requirement to Microsoft 365 Groups. Given that Microsoft 365 Groups have group mailboxes and can function very much like shared mailboxes, the difference in licensing is remarkable. Why does this happen? It could be due to internal Microsoft politics, omissions, or just a preference for Groups. Who knows?
A question about shared mailboxes brought up the topic of licensing requirements when a tenant has Microsoft Defender for Office 365 (MDO). The news is not good. Once MDO is active, every shared mailbox needs an MDO license, and every user mailbox must also be licensed for MDO (those with E5 licenses are covered). At $5 per month, those MDO licenses can ramp up to a considerable cost. Ouch!
July 1 marked the general availability of Exchange Server SE (subscription edition), the latest in a long line of server releases going back to Exchange 4.0 (1996). Exchange Server SE will soon be the only game in town after Exchange 2016 and 2019 reach end of support in October 2025. In other news, Defender for Office 365 now boasts protection against email bombs.
Microsoft Defender for Office 365 includes many tools to help investigators manage threat. The Email Preview tool shows the layout and appearance of the messages with which attackers try to fool recipients. It’s a valuable way of understanding how threat penetrates. But a recent change makes bad links in the email preview clickable, and that doesn’t seem like a good idea.
The Office 365 for IT Pros team welcomes Michel de Rooij as a new author. As a PowerShell Pro, he’ll like the code to update the impersonation protection list for anti-phishing policies. Or maybe he’ll rewrite it to make the code better. Either way, we win and the Mail Flow chapter should get a new lease of life.
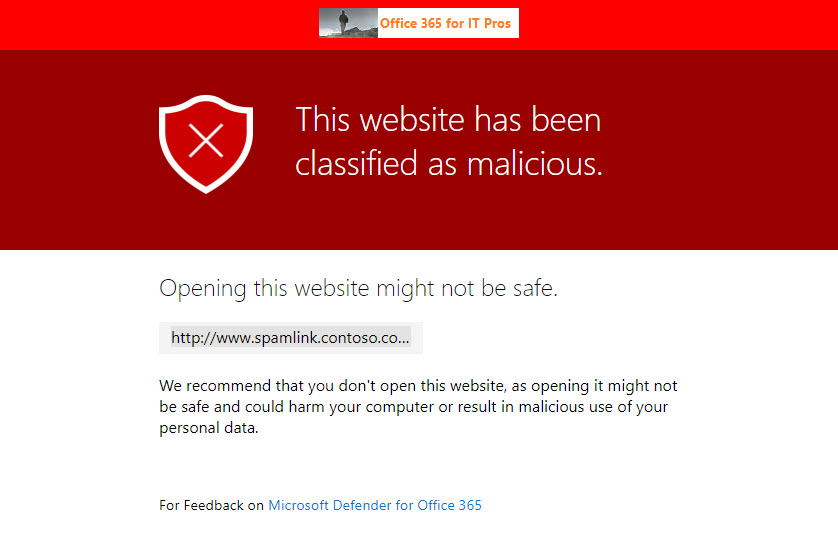
The Safe Links capability in Microsoft Defender for Office 365 is now generally available to protect Teams messages in chats and channel conversations, and even in web site links pinned as a channel tab. Most bad links flowing into an Office 365 tenant will continue to arrive by email, but this new capability closes off a gap where users are tempted to make a poor decision to share a malicious link through Teams.
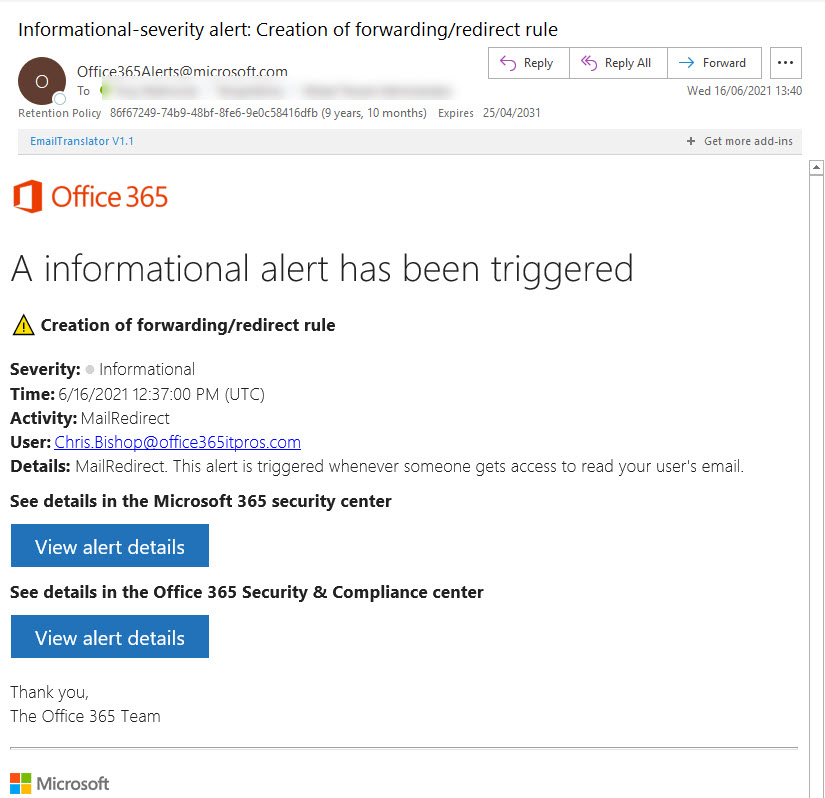
The need to remove basic authentication from Exchange Online is underlined by a June 14 report from the Microsoft Threat Intelligence Center pointing to how attackers compromise mailboxes using antiquated protocols like POP3 and IMAP4 to connect to accounts which don’t use MFA. After accounts are penetrated, the attackers plant inbox rules to forward copies of interesting messages and use the information received to plan and execute business email compromise attacks. Tenant administrators still have some work to do to secure Exchange Online and Azure AD…
Exchange Online Protection (EOP) and Microsoft Defender for Office 365 support anti-phishing policies which generate safety tips for users. The first contact safety tip warns users when they receive email from someone they don’t usually get messages from. It’s a way to put the recipient on their guard, just in case it’s someone trying to impersonate someone else whom the recipient actually knows.
A change due in December will improve how Exchange Online Protection suppresses high confidence phish messages and stop them being delivered to user mailboxes. The old-fashioned allowed sender and allowed domain lists are being taken out of the equation and ignored when EOP is sure that it’s dealing with some high-confidence phish. It’s time to check your anti-spam policies.