Microsoft has delayed the retirement of basic authentication for the SMTP AUTH client submissions protocol to 2027 or beyond. New tenants will be the first to be blocked and Microsoft will disable basic authentication for SMTP AUTH in a way that existing tenants can reenable the protocol. Eventually, we’ll get a date for final retirement sometime in 2027. These things take time!
The Direct Send feature allows apps and devices to send unauthenticated email via Exchange Online to internal receipts. Microsoft doesn’t want unauthenticated connections to send email because these connections could be hijacked by spammers. Enter the Reject Send feature to block Direct Send. Reject Send is in preview now but Microsoft wants it to be the default setting in the future.
Exchange Online announced two important changes on April 15. SMTP AUTH is being depreciated and a new external recipient rate limit is being introduced. The changes are intended to improve the security of Exchange Online. The introduction of an external recipient rate limit is also intended to reduce the ability of spammers to abuse the platform.
Microsoft is removing TLS 1.0 and 1.1 from Microsoft 365. This has been well flagged, but tenants might not understand the impact on PowerShell scripts which send email using the Send-MailMessage cmdlet and SMTP AUTH. In a nutshell, unless you force PowerShell to use TLS 1.2, attempts to send messages via Exchange Online will fail. It’s time to check those scripts and ,consider how to move away from SMTP AUTH and Send-MailMessage.
Last week’s announcement that Exchange Online will block basic authentication for multiple protocols on October 1, 2022, got some attention. Now the hard choices of what to do with clients and applications need to be made. To smoothen the path to remove basic authentication, Microsoft is making an exception for SMTP AUTH. Your scripts and multi-function devices will keep working after October 2022, but the writing is on the wall and eventually even SMTP AUTH will stop working.
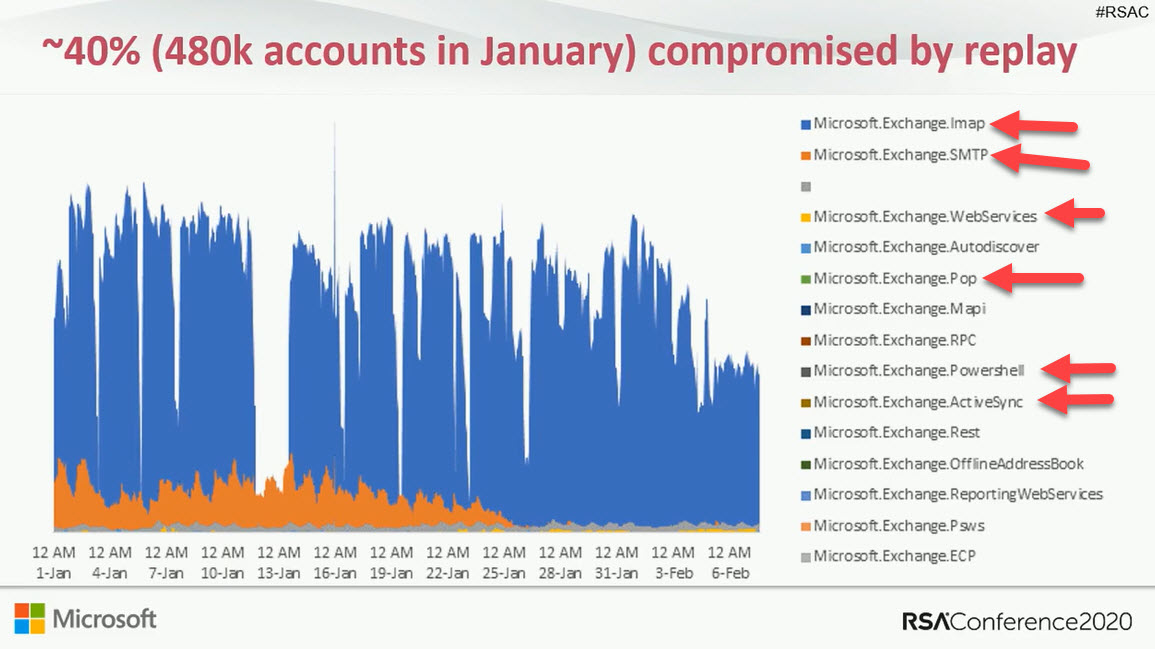
Covid-19 dealt a blow to Microsoft’s plans to remove basic authentication from 5 connection protocols for Exchange Online and forced them to postpone the removal from October 13, 2020 to sometime in the second quarter of 2021. The news is disappointing because basic authentication is a weakness exploited by many hackers. But you can’t plan for a pandemic and Office 365 tenants need more time to be ready for the deprecation.
Some doubt that Exchange Online will disable basic authentication for five email connection protocols in October 2020. The refrain is that it will be too hard for customers. Well, it might be hard to prepare to eliminate basic authentication, but if you don’t, your Office 365 tenant will be increasingly threatened by attacks that exploit known weaknesses.