October 1, 2022, is when Microsoft begins the final process of removing support for basic authentication for 7 email connection protocols from Exchange Online. The process will take several months to complete, and when it’s done, Office 365 will be a safer place that attackers will find more difficult to penetrate. But it’s time for tenants to prepare, if you haven’t already done so, and we highlight some critical points from Microsoft’s most recent post on this topic.
Last week’s announcement that Exchange Online will block basic authentication for multiple protocols on October 1, 2022, got some attention. Now the hard choices of what to do with clients and applications need to be made. To smoothen the path to remove basic authentication, Microsoft is making an exception for SMTP AUTH. Your scripts and multi-function devices will keep working after October 2022, but the writing is on the wall and eventually even SMTP AUTH will stop working.
Microsoft wants to remove basic authentication from Exchange Online connection protocols. But pressures have forced Microsoft into a new strategy and away from the mid-2021 date for deprecation of basic authentication for five protocols. Instead, Microsoft will disable basic authentication for protocols where it’s not used, include four addition protocols in its target set, and pause action for tenants where basic authentication is in active use. When they restart, Microsoft will give tenants 12 months’ notice that basic authentication will be blocked for a protocol. You can argue that Microsoft should have pressed ahead with their original plan, but would widespread disruption of service be worth the benefit gained from blocking vulnerable protocols? Balancing risk versus reward is often not easy.
Covid-19 dealt a blow to Microsoft’s plans to remove basic authentication from 5 connection protocols for Exchange Online and forced them to postpone the removal from October 13, 2020 to sometime in the second quarter of 2021. The news is disappointing because basic authentication is a weakness exploited by many hackers. But you can’t plan for a pandemic and Office 365 tenants need more time to be ready for the deprecation.
Some doubt that Exchange Online will disable basic authentication for five email connection protocols in October 2020. The refrain is that it will be too hard for customers. Well, it might be hard to prepare to eliminate basic authentication, but if you don’t, your Office 365 tenant will be increasingly threatened by attacks that exploit known weaknesses.
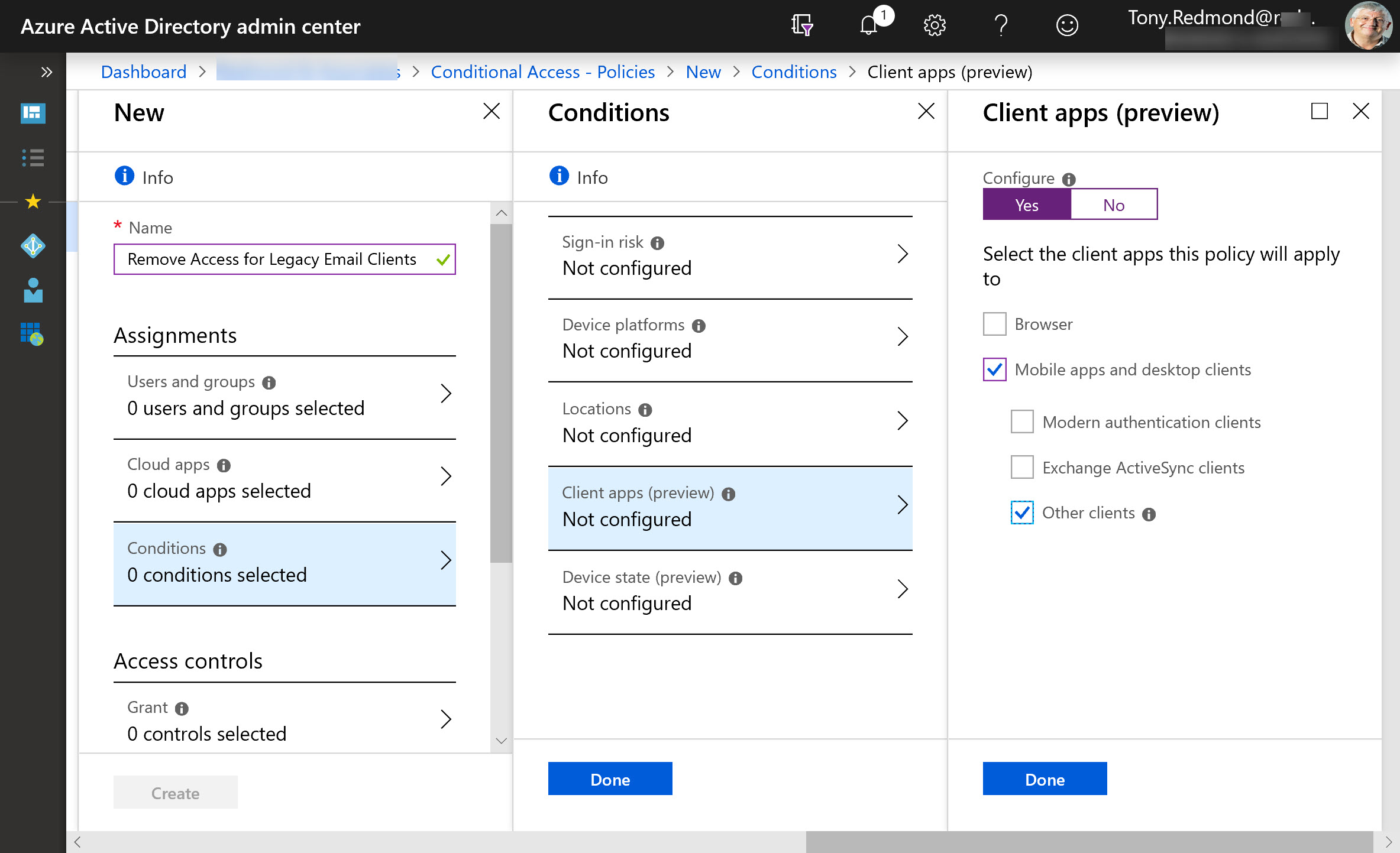
Microsoft plans to disable basic authentication for five Exchange Online connection protocols on October 13, 2020. They’ve been clear on this point for several months and are now moving to deliver tools and provide guidance about what people should do about clients that use basic auth connections with Exchange Web Services, Exchange ActiveSync, IMAP4, POP3, and Remote PowerShell. Work is needed to make sure that clients are prepared for the switchover to modern authentication.
Microsoft has announced that basic authentication for multiple email connection protocols won’t be supported after October 13, 2020. You won’t be able to connect with EWS, EAS, IMAP4, POP3, or Remote PowerShell unless you use modern authentication. There’s just over a year to prepare, but there’s some work to be done.
Despite the age of the protocols, you can cheerfully connect a wide range of IMAP4 and POP3 clients to Exchange Online. If you do, you might need to consider how to handle calendar appointments, and if you want to use iCAL, you’ll need to make some adjustments with PowerShell.
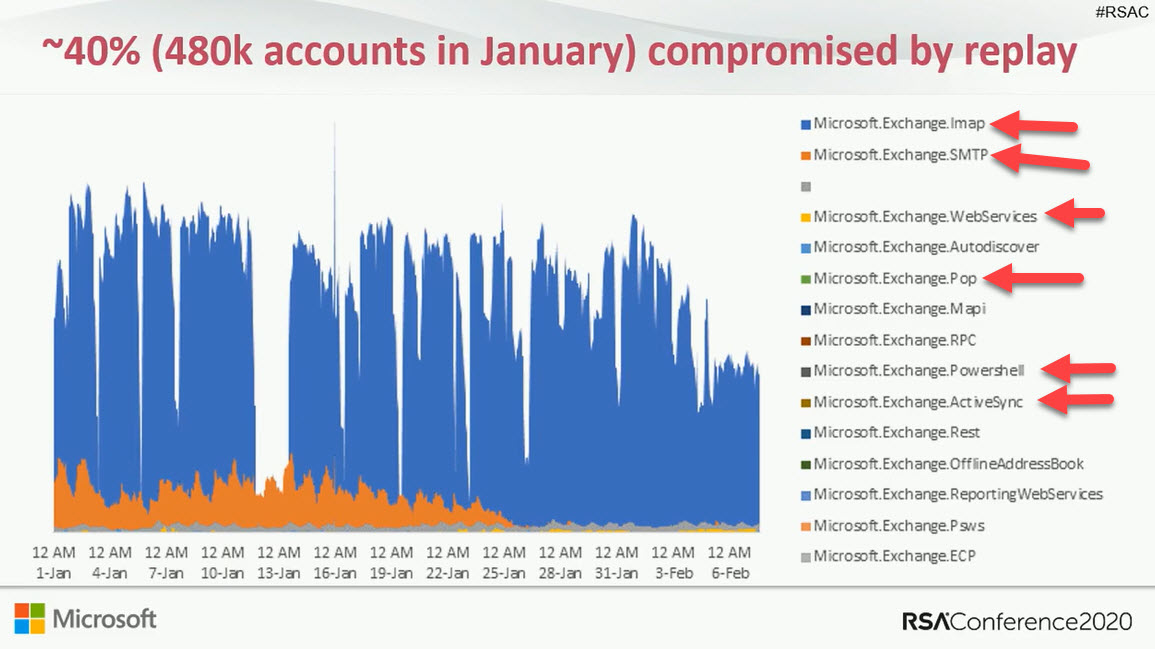
Exchange Online protocol authentication policies control what protocols a user can connect to mailboxes with, but it would be much better if we didn’t have to worry about some old and insecure protocols. Azure Active Directory gives Office 365 tenants the chance to clamp down on IMAP4 and POP3 connections and close off some of the holes that attackers try to exploit. Microsoft says that this can lead to a 67% reduction in account compromises, so that’s a good thing.