Azure AD conditional access policies can exert fine-grained control over the type of external users who can connect and what tenants they belong to. The new capability works especially well alongside Azure B2B Collaboration (guest users) and Azure B2B Direct Connect (used by Teams shared channels). It’s yet another way to impose control over who you allow to connect to your tenant.
The Entra ID Keep Me Signed In (KMSI) feature uses a persistent cookie to allow users close and reopen browser sessions without sign-ins. If you don’t want to use KMSI, you can update Azure AD company branding to remove the option. Users will then have to reauthenticate each time they start a browser session. The decision to disable or keep KMSI is highly tenant-specific and depends on how authentication happens.
Many Microsoft 365 features depend on accurate user account data in Entra ID (Azure AD). Here’s how to use PowerShell to track down accounts with important missing properties. Once you know which accounts need to be updated, it’s easy to insert the missing properties. Boring, but easy…
The Active Directory schema includes a drink attribute. This didn’t make the transition to Azure AD, but you can use one of the custom attributes to make drink show up on Microsoft 365 profile cards. This might not seem like a good use of your time, but it’s actually an illustration of how to put the Microsoft Graph Explorer tool to good use.
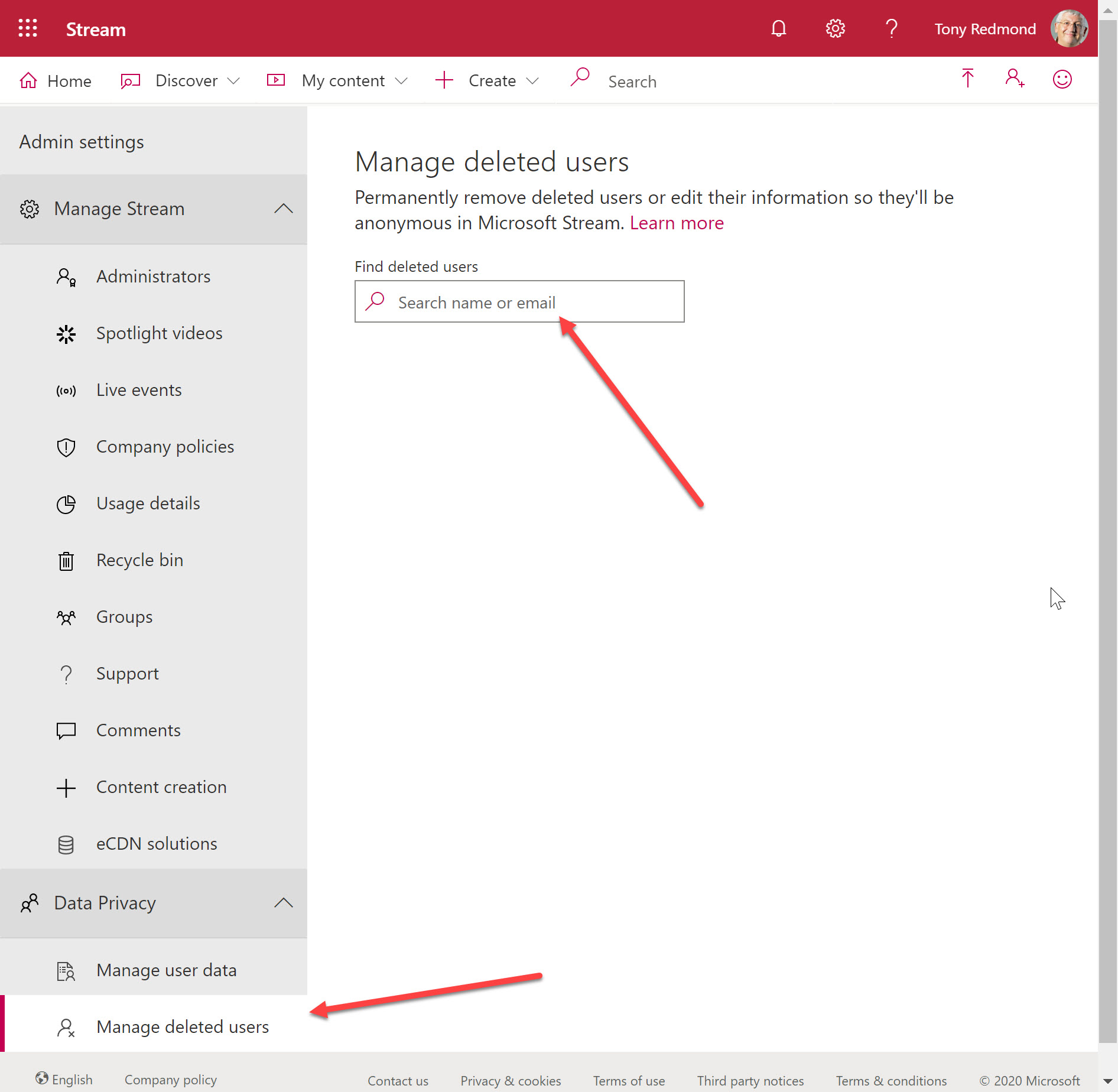
Microsoft Stream administration include a Manage deleted users option. However, you can’t manage a deleted user until all trace of their account has been removed from Azure AD, which means that you usually must wait 30 days for an account to be hard-deleted. It’s logical, but not in a good way.
Azure Active DIrectory is getting a slimmed-down background image to help with bandwidth-constrained locations. Office 365 tenants with custom backgrounds won’t see the change. Customizing the appearance of the sign-in screen is easy if you prepare. And to finish up, we have pointers to a set of videos about how Azure Active Directory authentication works.
The Azure Active Directory Group Naming policy generates display names for new Office 365 Groups created by various applications. You can include a prefix or suffix in a group name, The approach taken by email favored prefixes because this gathered all distribution lists together in one place in the GAL. However, prefixes work better with applications like Teams.
Azure Active Directory now features the public preview of the My Sign-Ins feature, which allows users to see where their sign-ins originate and what applications are used to sign-in. It’s a nice idea but Office 365 users are unlikely to find the page. We can help by creating a custom tile with a link to the My Sign-Ins page. The tile appears in the Office 365 apps menu and makes it easy for people to access their sign-in data.
Office 365 makes extensive use of Azure Active Directory guest accounts. Implementing a risky sign-in policy is a good idea, but it can have the unfortunate side-effect of suddenly blocking guest accounts that could previously access tenant resources. If blocks happen, they can only be lifted through administrative intervention in the guest account’s home tenant.
A reader asks if it’s possible to create a dynamic Office 365 group for global administrators. Well, it is and it isn’t. Azure Active Directory doesn’t give us the ability to execute the right kind of query to find global administrators, but with some out-of-the-box thinking, we can find a way to accomplish the task.
The Groups section of the Azure Active Directory portal now includes a preview of a feature to configure the Office 365 Groups naming policy without going near PowerShell. Although those proficient with scripts and GUIDs will lament this sad reduction in standards, the normal administrator will welcome the chance to forget some obscure syntax.
The LinkedIn connector for Office 365 now uses a group to control the set of user accounts allowed to connect their accounts to LinkedIn. It’s a good change because it makes the connection easier to manage. Even so, you might still need to use PowerShell to manage the membership of the group, especially if you want to add multiple people to the group at one time.
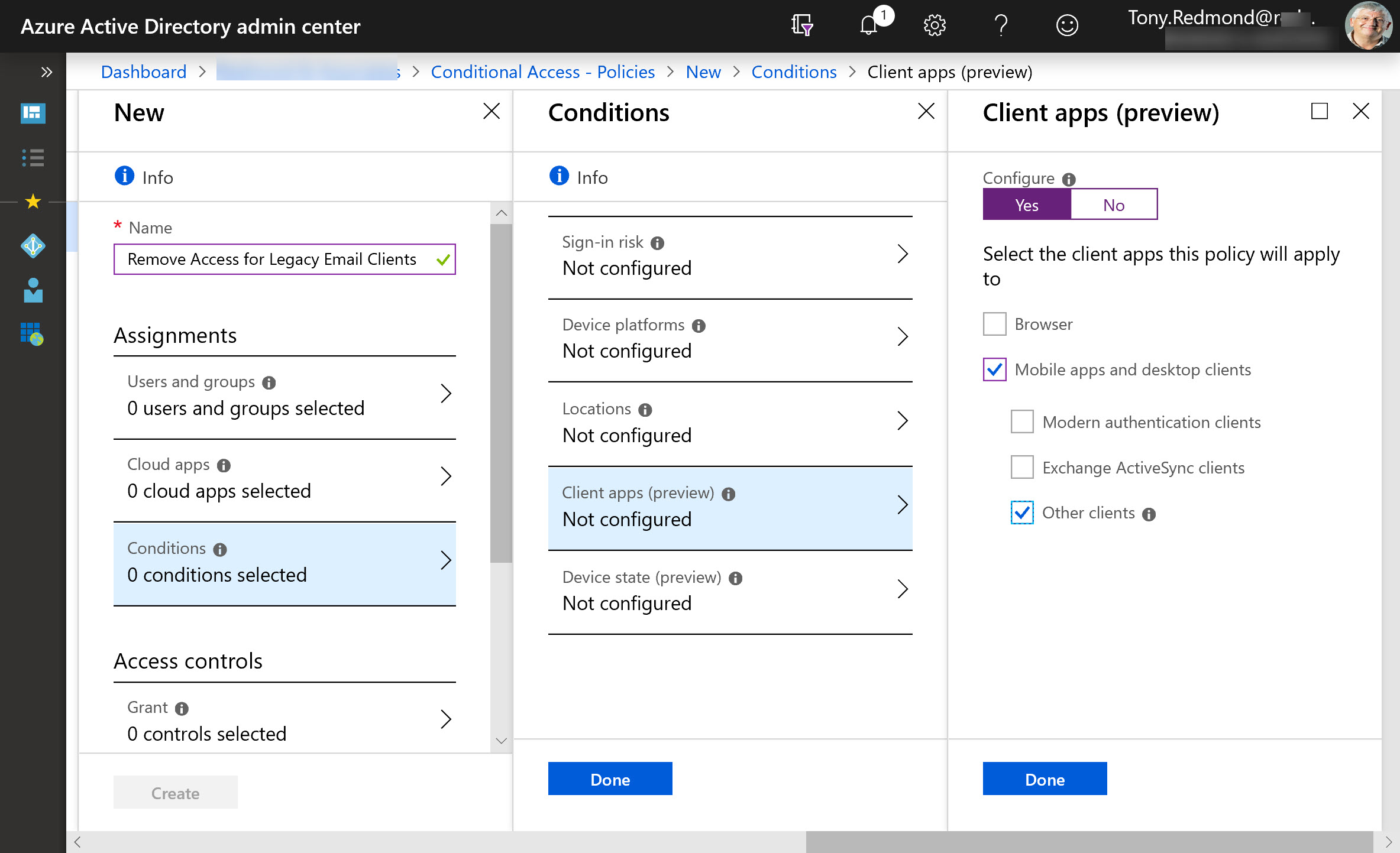
Exchange Online protocol authentication policies control what protocols a user can connect to mailboxes with, but it would be much better if we didn’t have to worry about some old and insecure protocols. Azure Active Directory gives Office 365 tenants the chance to clamp down on IMAP4 and POP3 connections and close off some of the holes that attackers try to exploit. Microsoft says that this can lead to a 67% reduction in account compromises, so that’s a good thing.
The January 24-25 Azure Active Directory outage demonstrated once again how important AAD is to Office 365. Microsoft’s Post Incident Report tells us what happened to deprive 1% of the users in Europe of service. That doesn’t sound a lot, but you’d be mad if you were affected.
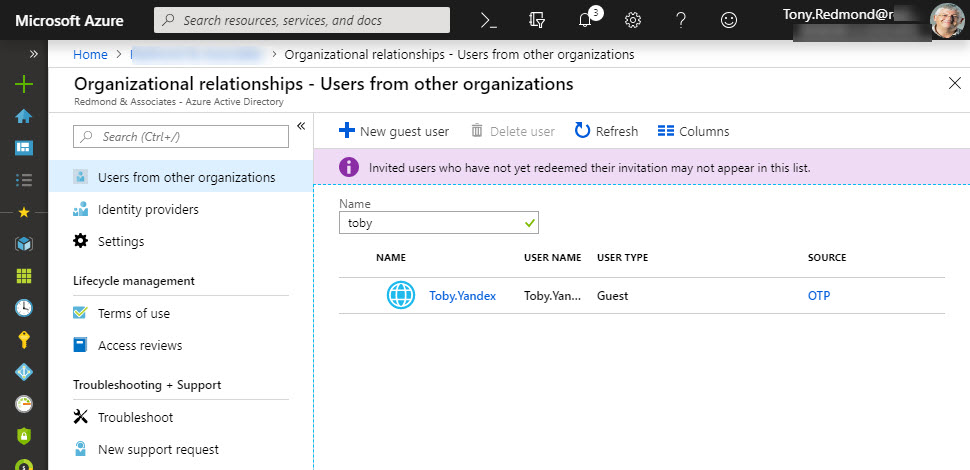
Microsoft has launched email one-time passcodes (OTP) into preview for Azure Active Directory guest accounts. It’s all to do with better collaboration. OTP doesn’t support Teams, Planner, or Office 365 Groups yet, but it can be used to share documents from SharePoint Online or OneDrive for Business.
Making sure that Office 365 user (and administrator) accounts have good passwords is a never-ending task. A new preview feature in Azure Active Directory helps by ensuring that users can’t include common words specific to the organization (like its name) in a password. It’s another piece in the puzzle to frustrate potential attackers.
Now that we know all about the different email addresses used by Microsoft 365 Groups and Teams, the question arises of how to include a team channel as a member of a distribution group. As it turns out, there’s a simple way and a more complicated way.
By default, the Groups policy for an Office 365 tenant allows group owners to add guest users to group membership. You can block this access if necessary, but it’s probably not what you want to do as blocking brings guest access to a complete halt across the tenant.
Microsoft has updated its retention period for Office audit records from 90 to 365 days, but only for accounts with Office 365 E5 licenses. On another front, the problem with truncated audit records for Azure Active Directory events still persists.
How many guest users does your Office 365 tenant have? And how many of those accounts are actually used? Given that many Office 365 applications now generate guest user accounts to facilitate external access to content, managing these accounts is a growing concern.
Org-Wide Teams are a nice feature, but calculating their membership can be puzzling, as in the case of some perfectly valid accounts that were not added to a team. As it turns out, the error lies in Azure Active Directory.
You can now connect Office 365 accounts to LinkedIn accounts (or block the connection at a tenant level). It’s a nice way to keep tabs on your LinkedIn contacts and find out what they’re doing with a simple click in an Office 365 people card.
Security groups are often used to protect access to resources, but they can’t be used to control membership for Microsoft 365 Groups or Teams. If you want to use AAD security groups to control membership for Groups and Teams, you need to come up with a way to synchronize. PowerShell is available to do the job, and as it turns out, it’s not too difficult.
An outage in a U.S. datacenter on September 4 caused problems for Azure Active Directory with a ripple effect on Office 365. It’s a good example of how cloud services depend on each other, so when one fails, another has problems.
Some say that Microsoft Teams doesn’t support dynamic Office 365 Groups. Well, I couldn’t find anything formal on the topic and the teams that I have configured to use dynamic groups work well, so what’s the real scene? As it turns out, Microsoft is still working on the feature.
Microsoft has launched the preview of Google B2B Federation, which allows Google accounts to be used to access Azure AD apps. Quite how this will work out for apps that use guest user accounts is unknown at this point.
A recent post by MVP Mark Vale describes how to use synchronization transformation rules in AADConnect to change the last name, first name format (for example, Smith, James) for display names to a more user-friendly first name last name format (our example becomes James Smith) for accounts as they synchronize to Azure Active Directory from an …
Read More “Losing the Last Name, First Name Legacy”