Microsoft is making some important changes to Purview eDiscovery from May 26, 2025. The changes affect how content searches work and are likely to affect many Microsoft 365 tenants. Administrators and eDiscovery investigators will both have to master new ways of working with eDiscovery cases, searching for information, reviewing search results, and exporting what’s found. Changes to PowerShell cmdlets might affect scripts, so there’s lots to consider.
The need to find SharePoint documents with sensitivity labels might arise during a tenant divestiture to decrypt the documents before the split. As it turns out, searches against the SharePoint InformationProtectionLabelId property is a good way to find the files. After that, the need arises to decrypt the documents, which is where Microsoft Purview eDiscovery (premium) might come in handy.
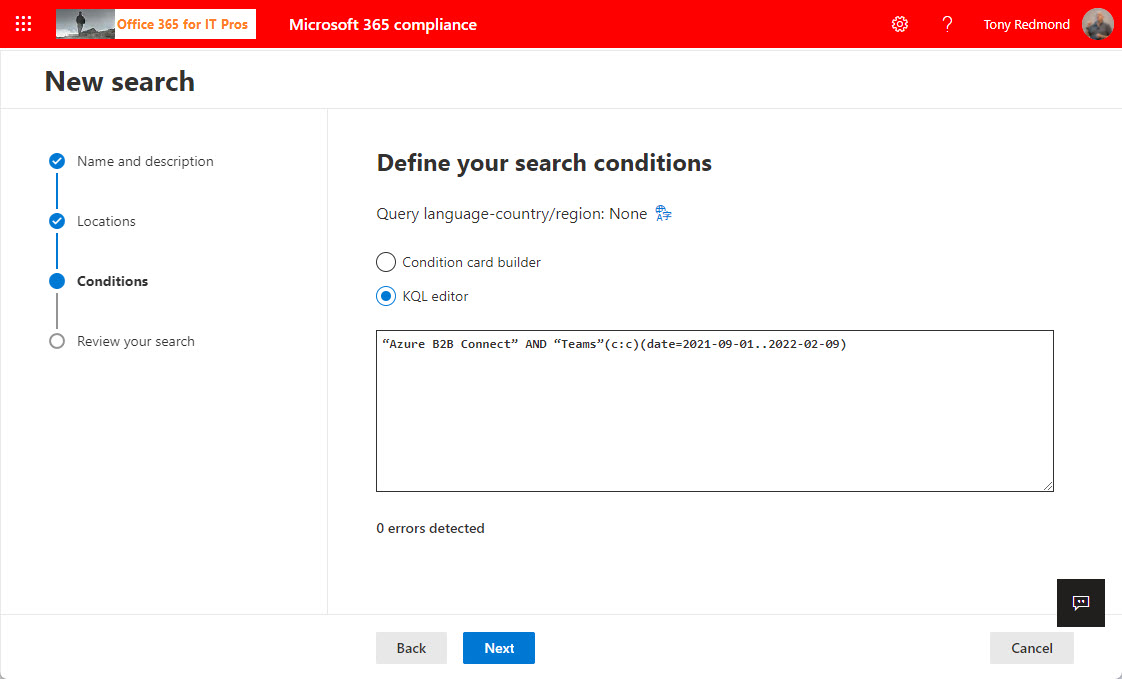
The KQL editor is a relatively new feature in Microsoft 365 that makes it easier to compose queries to find email and documents in content searches, core eDiscovery, and advanced eDiscovery. Although it’s not perfect, the KQL editor helps compliance managers to perfect queries and resolve syntax errors. Human intelligence is still needed to make sure that everything works!
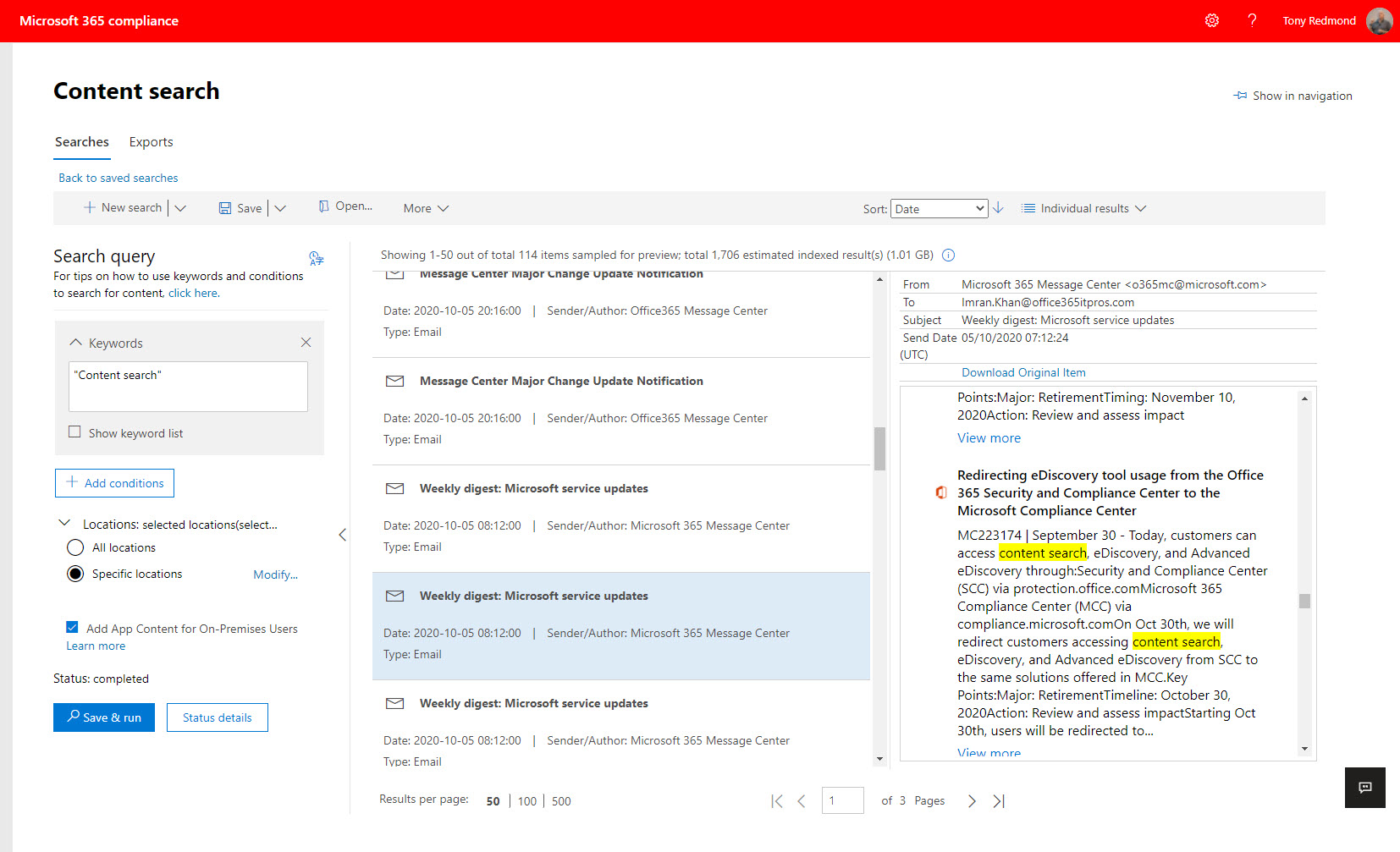
The Microsoft 365 compliance center has a new content search UI. The new UI is prettier than before, but it’s also slower and more buggy. After several years of effort to develop content searches, you’d expect Microsoft to do better. A lot betterr. Unhappily, the beauty of the new interface seems to have distracted the engineers from the problems that become all too apparent when you try to use content searches to do real work. What, if any testing, was done to validate the new UI is unknown.
Microsoft 365 eDiscovery features will respect documented limits from May 10. The changes are likely made to conserve resources consumed by searches against the massive amounts of data now found in Office 365 tenants. The changes probably won’t affect eDiscovery investigators except in reminding everyone that the items shown in search preview are only a representative sample of what can be found by a full search.
Exchange Online indexes the items stored in mailboxes. Some of the items are partially indexed, meaning that not all of their content is indexable. Microsoft has a PowerShell script to analyze the number of partially indexed items found in mailboxes. The output is kind of esoteric, so we worked it over to create something more understandable.
When you use an Office 365 content search to find items, the results from Exchange Online might include some encrypted attachments. A change means that the attachments can now be decrypted to make it easier for investigators to review the information. It’s a small but important change, just like the update to Edge which stops ClickOnce programs running unless an Edge setting is enabled. All good, clean, honest fun.
For compliance purposes, the Microsoft 365 substrate captures copies of Teams messages in Exchange Online mailboxes. The compliance records are indexed and discoverable, which means that they can be found by content searches. However, Teams compliance records are imperfect copies of the real data, which is a fact that seems to have escaped many people.
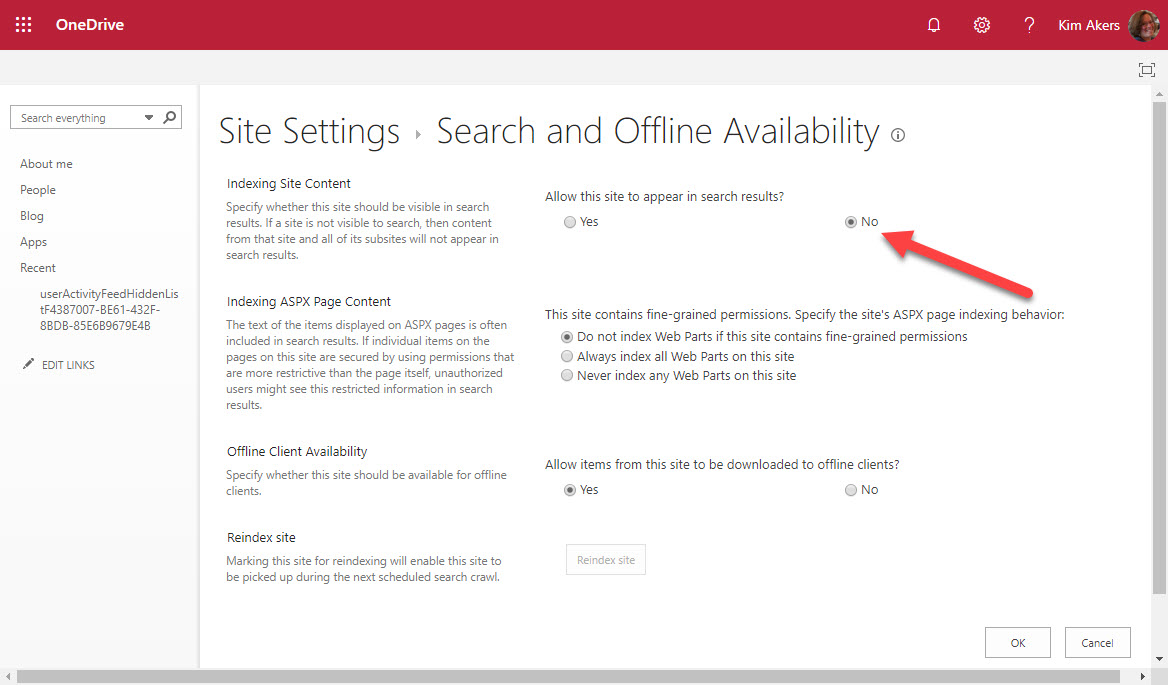
OneDrive for Business owners could exclude their sites from Office 365 searches but they can’t any longer after Microsoft acted to remove the capability from OneDrive site settings. All OneDrive for Business sites are now indexed and available to Office 365 searches.
Microsoft has confirmed that disconnected Exchange Online mailboxes are not included in the sources scanned by Office 365 content searches, thus clearing up some misunderstandings that might have existed in the field. The bottom line is that if you want to search mailboxes that don’t belong to accounts, you should use inactive mailboxes.
If you want to include SharePoint Online and OneDrive for Business locations in an Office 365 content search, you need to know the URLs of the target sites. Finding the URLs can be problematic, but here’s some easy ways to do the job. PowerShell, as usual, comes up trumps…
Office 365 tenant administrators can use different ways to access user data. Shouldn’t you have a policy to govern that access?