Office 365 supervision policies can now make use of artificial intelligence and machine learning to detect offensive language in email and Teams communications. The data model covers a wide range of problematic language, but only in English. You can go ahead and cheerfully continue to swear in French, German, and other languages with no danger of being detected by policy.
The CISA report titled “Microsoft Office 365 Security Observations” makes five recommendations to improve security of an Office 365 tenant. The recommendations are valid, but competent administrators won’t take long to implement them. In fact, the worst thing is that consultants brought in to help organizations didn’t seem to have much expertise in securing Office 365.
On May 7, Microsoft eventually fixed a truncation bug that affected group events (creation, add member, etc.) ingested into the Office 365 audit log. The fix took far too long coming and the overall response is certainly not Microsoft’s finest hour. Audit events, after all, are pretty important in compliance scenarios and it’s not good when those events are incomplete.
The modern SharePoint Admin Center introduces the ability to rename the URLs for SharePoint site names. This responds to a longstanding customer request and makes it possible for site names to reflect what users see elsewhere in Office 365 groups or Teams. It’s a small but welcome change in the fit and finish category.
Announced in January, paused in March – that’s the fate of the MailItemsAccessed audit record generated by Exchange Online for the Office 365 audit log. Microsoft found some problems that they are fixing, which is good (because you want audit data to be reliable). And when the fixes are available, the deployment of the new audit record will restart.
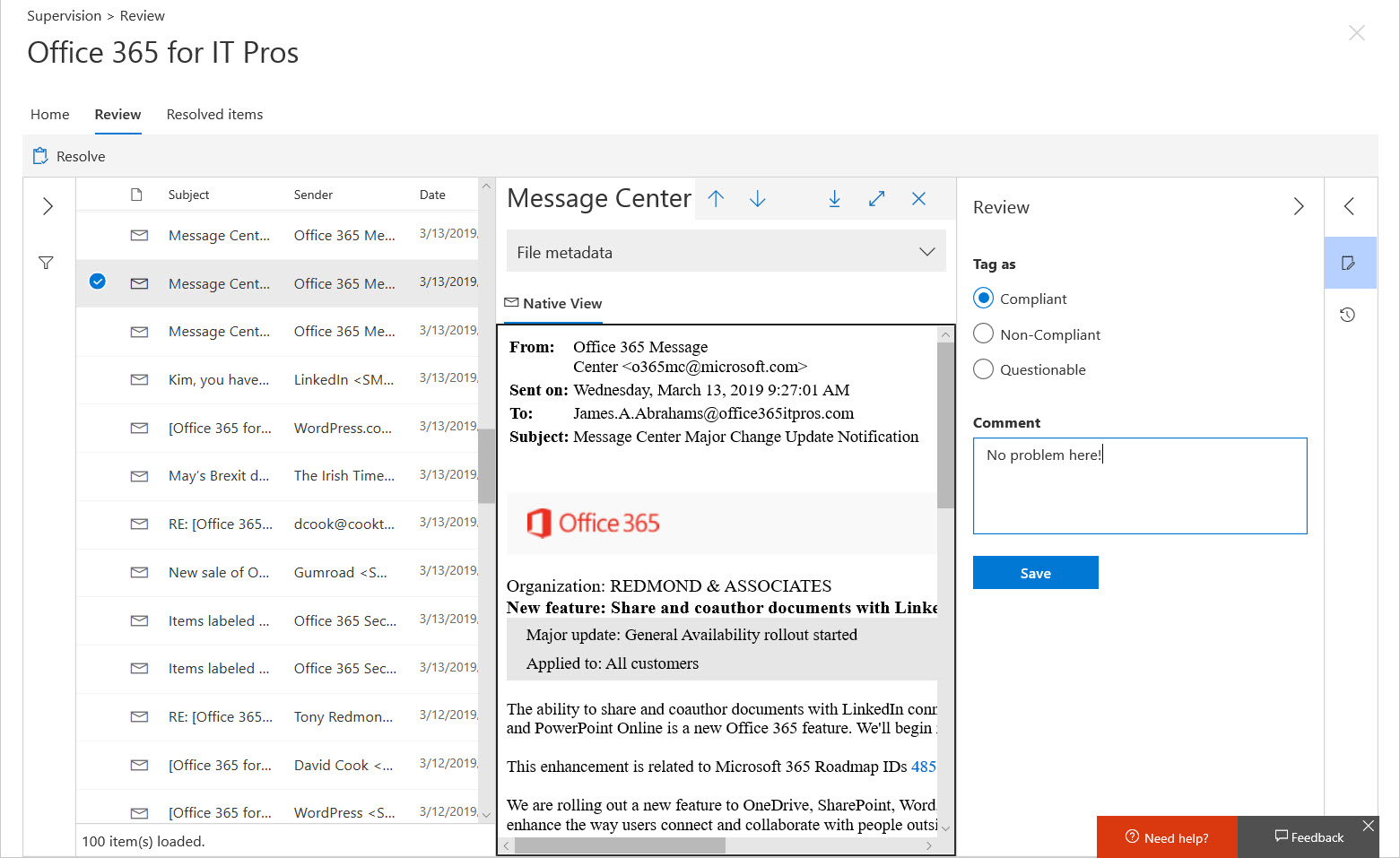
Although Office 365 supervision policies are intended to monitor a subset of user communications, usually involving specific groups of people, you might want to use a policy to monitor all email. In that case, how do you make sure that your policy has everyone in scope? The problem is that supervision policies don’t support dynamic distribution lists, so you need to do some work to build and maintain a distribution list containing all user mailboxes.
In one of those interesting (but possibly worthless) facts discovered about Office 365, we find that audit records are captured for Teams compliance records written into Exchange Online group mailboxes. The Search-UnifiedAuditLog cmdlet reveals details that we can interpret using some techniques explained in Chapter 21 of the Office 365 for IT Pros eBook.
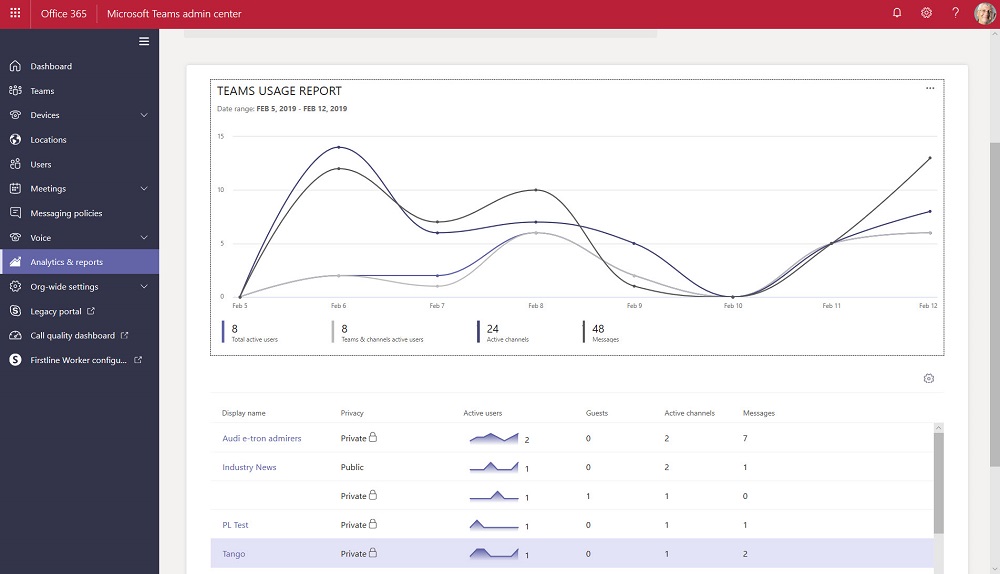
The Teams Admin Center has been renamed to remove any reference to Skype for Business Online. The console now includes a set of new Teams usage reports. The reports differ from what’s available in the Office 365 Admin Center and aren’t quite as powerful, but we can expect Microsoft to improve and refine these reports over time.
Security alerts from Office 365 Cloud App Security now flow into the Office 365 Audit Log, which means that you can run the Search-UnifiedAuditLog to find the alerts. Unhappily, more work than should be needed is necessary to extract the interesting information from the alert records.
Exchange Online now captures session identifiers in its mailbox and admin audit records that are ingested in the Office 365 audit log. That’s interesting and useful, but how do you access and interpret this information on a practical level?
Exchange Online will soon capture audit records for any access to a message in a mailbox. Initially, the audit records will not be ingested into the Office 365 audit log, but that will happen in the future.
On Wednesday, November 28, Tony’s speaking about Office 365 Data Governance at the European SharePoint Conference in Copenhagen, Denmark. The topic is interesting, if only because its source material changes all the time.
Following a Dutch report saying that Office 365 might violate GDPR, some thoughts about how to restrict some of the flows of information from an Office 365 tenant to Microsoft.
Microsoft has updated its retention period for Office audit records from 90 to 365 days, but only for accounts with Office 365 E5 licenses. On another front, the problem with truncated audit records for Azure Active Directory events still persists.
Exchange Online sends its mailbox audit records to the Office 365 audit log. You can search the log to discover who deleted messages from mailboxes, normally only an issue when delegates are involved.
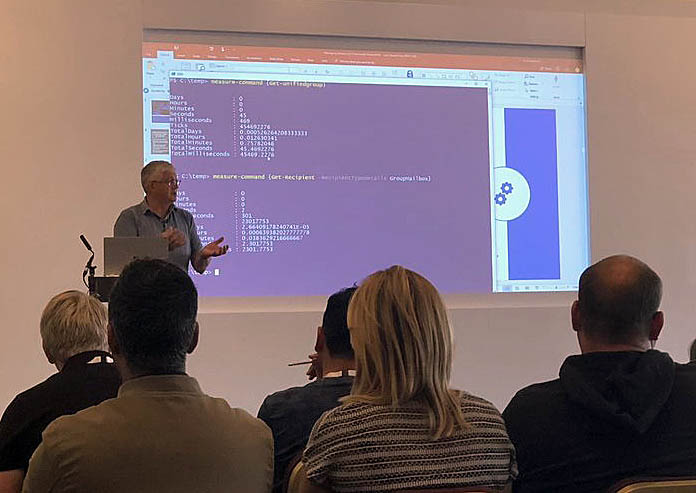
A demo to show how easy it is to use PowerShell to manage Office 365 Groups and Teams was progressing nicely at the UK Evolve conference when a problem happened with code that used to run perfectly. Sounds like a normal programming situation, but in this case, Microsoft had changed the format of Office 365 audit records for Azure Active Directory operations. That’s not so good. What’s worse is that some essential data is now missing from the audit records.
Records featuring an account called BOXServiceAccount appear in the Office 365 audit log. Not much information is available about the account, but it’s all OK because it’s used to assign administrative roles to Office 365 accounts.
Office 365 tenant administrators can use different ways to access user data. Shouldn’t you have a policy to govern that access?