A May 20 post contains the welcome news that the new audit events promised for Purview Audit standard customers should be available in June 2024. Some of these events are for Exchange Online, like the famous MailItemsAccessed event. Others are for Teams and SharePoint Online. In the case of Exchange, tenant administrators might have to do some work to validate that mailbox audit configurations are correct.
On May 14, Microsoft announced that they will require Azure MFA for connections to services starting in July 2024. No details about the implementation are available, so it’s difficult to measure the likely impact on Microsoft 365 tenants. Given that very few people access services like the Azure portal, it’s probable that the impact will not be large, but it would be nice to hear more precise details from Microsoft.
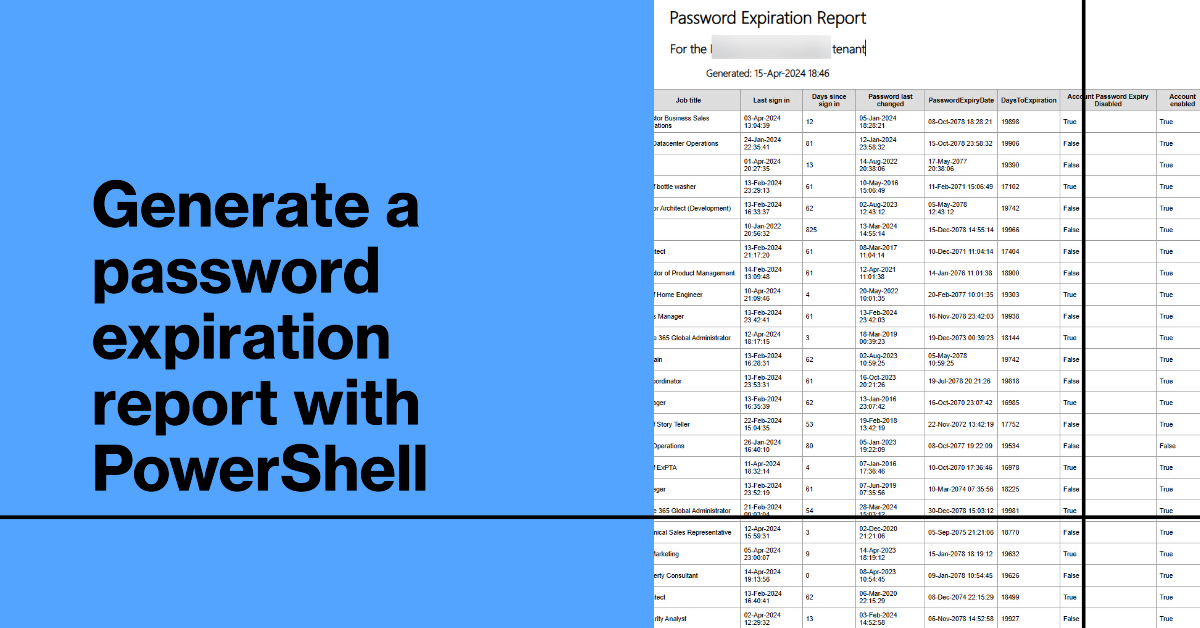
Although the trend is toward password authentication, many Microsoft 365 tenants still use passwords and some force users to change passwords regularly. This article explains how to create a password expiration report with PowerShell. The script caters for where a tenant password expiration policy is set for passwords to never expire. If anything else, it’s yet another example of how to extract information using PowerShell.
The Maester tool is a community initiative to create a tool to help tenant administrators improve the security of their Entra ID tenants. It’s still in its early stages, but even so Maester shows signs that it will be a valuable asset for administrators who want to learn more about securing their tenant against possible external compromise.
A new major version of the MsCommerce PowerShell module makes you hope that something good is included in the new code. In this case, it’s hard to know if the developers did anything but increase the major version number for the MsCommerce module. Not much has changed. The module is as bad as ever, but at least it can be used to disable self-purchases of all supported licenses, which is all that’s really important.
Every Microsoft 365 tenant has a tenant identifier, a unique GUID that’s used within the Entra ecosystem to identify a tenant and its objects. Much has changed since I last wrote about this topic in 2021, including the introduction of new Graph APIs to resolve tenant names to identifiers and vice versa.
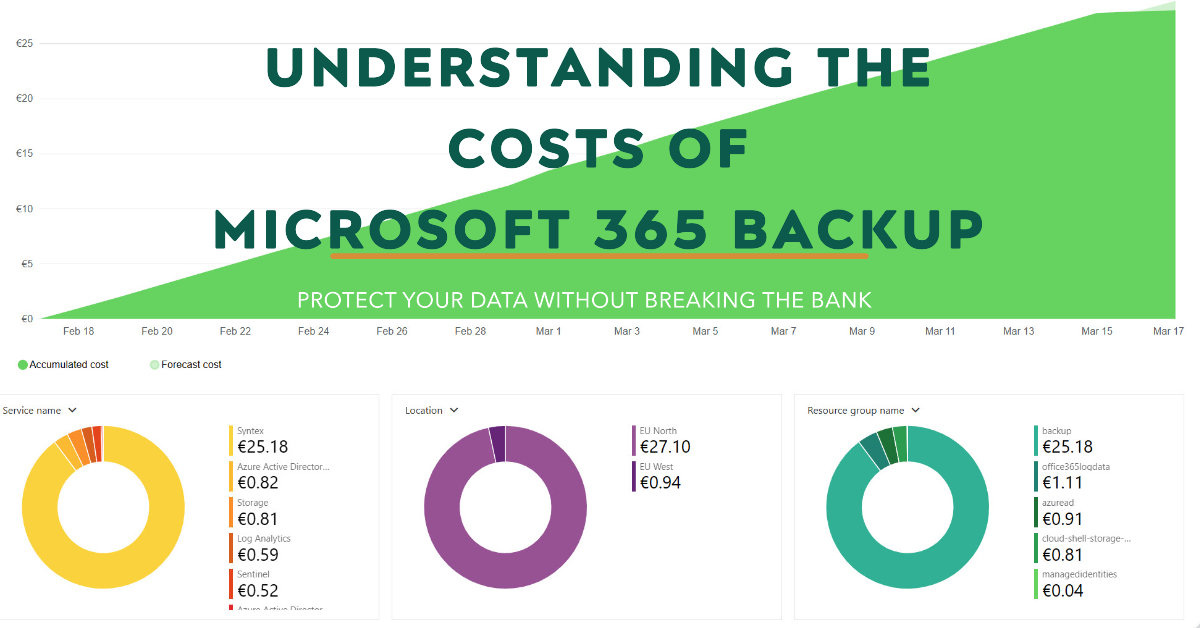
Microsoft 365 Backup costs are charged on a PAYG basis against an Azure subscription. You pay a flat fee of $0.15 per month per gigabyte of protected content. This article discusses calculating the sizes of protected data and reports the costs accrued over two months.
A recent article by a Microsoft MVP attempted to lay out a case that tenants should not use Microsoft 365 PowerShell and use ISV products instead. It’s a silly position to argue. PowerShell is an important automation tool for administrators that can’t be replaced by any ISV product. ISV products have their place and fill many gaps, but arguing to dump PowerShell and use ISV products instead just can’t be justified.
Microsoft has created an easy to use Microsoft 365 Backup solution. Its key feature is speed, including speed to restore data. I tested restores for Exchange Online (which worked) and SharePoint Online and OneDrive for Business (which didn’t). The lack of logging and error reporting when failures happen lead to frustration. Microsoft has some work to do to bulletproof this solution.
The latest version of the Microsoft 365 Licensing Report script includes code to generate cost analyses for the departments and countries assigned to user accounts. Everything works well if the properties of Entra ID user accounts are complete and accurate. Sometimes this isn’t so, and that leads to problems when attributing costs at a department or country level.
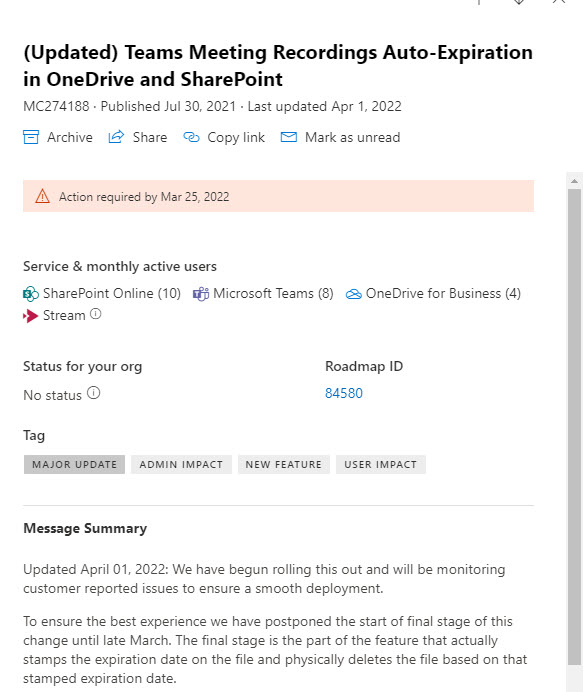
This article describes how to use the Microsoft Graph PowerShell SDK to retrieve and interpret Microsoft 365 message center posts with the intention of discovering what percentage of announcemengts end up being delayed (not being available at the predicted date). Teams makes lots of feature announcements and over 57% of those announcements are delayed.
The Microsoft Graph includes the Service Communications API. SDK cmdlets can use the API to retrieve and work with service health data. In this article, we show how to use Graph SDK cmdlets (based on the API) to fetch and work with service health data, including creating an email report to update people about the current state of tenant health.
Exchange mailbox statistics reports are usually produced using PowerShell cmdlets. However, using Graph usage data is a faster way to process mailboxes because it avoids the need to fetch mailbox statistics by running a cmdlet for each mailbox. This article describes how to speed things up in a way that will probably benefit larger organizations most, but every Exchange Online tenant can probably benefit.
On November 15, Microsoft announced Microsoft 365 Backup would enter a public paid preview in December 2023, Paid preview means that tenants must link a valid Azure subscription to Syntex pay-as-you-go to pay the $0.15 fee per GB per month for protected content. We’ll know more once the preview begins and we get the chance to see just how fast backup and restore is.
This article describes how to use the Microsoft Graph PowerShell SDK to customize the user account properties shown by the Microsoft 365 user profile card. Previously this was possible using a Graph API request to the beta endpoint. Now everything is in production and Graph SDK cmdlets are available to make customization a tad easier.
The MFCMAPI utility is of great help to Microsoft 365 tenant administrators who want to understand the data apps store in Exchange Online mailboxes. An on-premises mailbox stores email data, but in the cloud, Microsoft 365 apps use Exchange Online as a convenient place to store data that needs to be accessible to services like Search and eDiscovery.
A setting in the Teams meeting policy controls whether users can access the meeting chat in meetings hosted by non-trusted external tenants. By default, the setting is On, meaning that users can participate in chat for any meeting they join in any tenant. If you have concerns about this aspect of meetings, turn the setting Off and define trusted tenants.
Microsoft suggests that allowing every user to create new Microsoft 365 groups. That’s mad. Controlling group creation through policy settings is the only way to go. It will avoid group sprawl (or team sprawl) and avoid a lot of administrative effort that will otherwise be devoted to cleaning up the mess of unused and unwanted groups. This article explains how to update policy settings to control group creation using cmdlets from the Microsoft Graph PowerShell SDK.
This article explains how to use PowerShell to remove licenses from disabled accounts, including some caveats such as not removing Exchange Online licenses. Organizations might want to do this to save money on Microsoft 365 license fees while an account is temporarily unused. Removal of Exchange Online licenses can result in the loss of a mailbox, and you don’t want that to happen if you’re disabling accounts just because someone is on a long-term sabbatical or other leave of absence.
Microsoft 365 tenants with eligible licenses can use Bing Chat Enterprise (BCE). It’s a great way for users to become accustomed to dealing with AI prompts and generated results. First, users can discover how well-structured prompts generate better results. Second, they can see how a lack of care in reviewing results might get them into trouble because of AI-generated errors.
For whatever reason, SharePoint Online doesn’t allow administrators to control the settings of document libraries. In particular, default sensitivity labels. It seems crazy that other Microsoft 365 workloads allow administrators to manage the settings of things like mailboxes, groups, plans, and teams, but SharePoint Online holds steadfast to not allowing administrators go deeper than a site. It would be nice to see consistency around administrator access across all workloads.
Teams Premium Trial licenses are to be offered to end users in commercial tenants worldwide for self-service purchases from September 2023. I quite like some of the functionality available in Teams Premium, but I think organizations are better off using the “regular” Teams Premium trial licenses to run a test involving up to 25 users for 30 days. The results are probably going to be more indicative of the worth of Teams Premium than any individual test can be.
Microsoft announced on August 17 that they are not proceeding with the implementation of dark mode support in the Teams Admin center. The news came as a surprise, but it’s an indication of the lack of user interface consistency across the different Microsoft 365 administrative consoles. Token handling is another example. I can live without dark mode, but being forced to sign out by the Teams admin center is a pain.
A reader asked why some deleted Microsoft 365 user accounts appear to have assigned licenses. That seemed strange because licenses are freed up for reuse when accounts are deleted, so we took a look behind the scenes to find out why some deleted user accounts keep license information in their properties and some do not.
At the Inspire conference, Microsoft briefed their partners about the Microsoft 365 Backup and Microsoft 365 Archive products they plan to launch at some time in the future. Microsoft’s biggest advantage is their access to data and the speed at which they can process the information. Whether this gets people past the “all digital eggs in the Microsoft basket” issue remains to be seen.
Outlook Monarch controls are available to help with the deployment of the new Outlook for Windows client in a mixture of Exchange settings and registry entries. You can block users from using the new client or adding consumer email accounts to Monarch. And best of all, you can disable the “try the new Outlook” toggle until you’re ready for people to plunge into the brave new world of the revamped Outlook for Windows.
In this article, we discuss how to create a report of registered devices known to the Exchange mobile device management framework. Microsoft hasn’t made many changes to the way Exchange Online manages mobile devices connected to its mailboxes over the past few years and would prefer if organizations used Intune instead. But if you just want simple device management, Exchange delivers, and PowerShell reveals what devices are active.
Microsoft has announced that Teams now supports the Microsoft 365 targeted release mechanism, meaning that new Teams features should appear more consistently. The Teams preview program continues, but targeted release takes precedence. In other news, the Teams chat client in Windows 11 is being replaced by the Teams Free client. This probably won’t make much different, but it’s good to know.
A new Microsoft 365 Audit Platform service plan is available to license solutions like App Governance in Microsoft 365 Defender for Cloud Apps. After a shaky start, App Governance includes some useful functionality, including a set of default policies to highlight apps that need some attention. If you don’t have the necessary licenses to use App Governance, there’s always the examination of raw data about app activity, like sign-in information for app service principals.
Sometimes administrators need to intervene and cancel meetings on behalf of users. That’s why the Remove-CalendarEvents cmdlet exists. The cmdlet scans a user mailbox to find meetings organized by the user for a defined period and cancels the events. Meeting participants receive a cancellation notice. It’s a useful cmdlet to know about, just in case.
Microsoft didn’t do a great job of announcing the side-by-side viewing feature for Microsoft 365 apps. It seemed like the only reason for the feature was to drive usage for the Edge browser. As it turns out, you can choose to have Microsoft 365 apps use a different browser, and the tools to do that are now available.
Microsoft 365 includes a framework to create, send, and manage organization messages to users. It’s a good idea, but the implementation is sadly limited. First, you’re restricted to messages that Microsoft wants administrators to send to boost consumption of the Office apps. Second, you can’t customize the text or the appearance of the messages. Last, the dashboard to manage organization messages is half-finished.
Microsoft 365 tenants can select any of the verified domains for the tenant to send Microsoft 365 service messages instead of using the default domains. The update also allows tenants to choose a routable recipient (username) instead of the traditional “no-reply” address. Overall, this seems like a very easy change to implement that shouldn’t cause any problems.
The new SharePoint block download policy applies at the site level to stop users downloading files, even to work with them using the Office desktop apps. It also stops people printing and synchronizing files. In this article, we explain how to apply the policy with PowerShell, including how to apply the SharePoint block download policy to all sites assigned a certain sensitivity label.
Applying a default sensitivity label to a SharePoint Online document library is just one of the set of security and management and governance features requiring the new Syntex Advanced Management license. The new license is in preview so all the features that it covers might not be fully baked. Microsoft 365 customers might well ask if this is yet another example of Microsoft bundling features into a new paid-for add-on license. Of course it is. You don’t expect new functionality for free, do you?
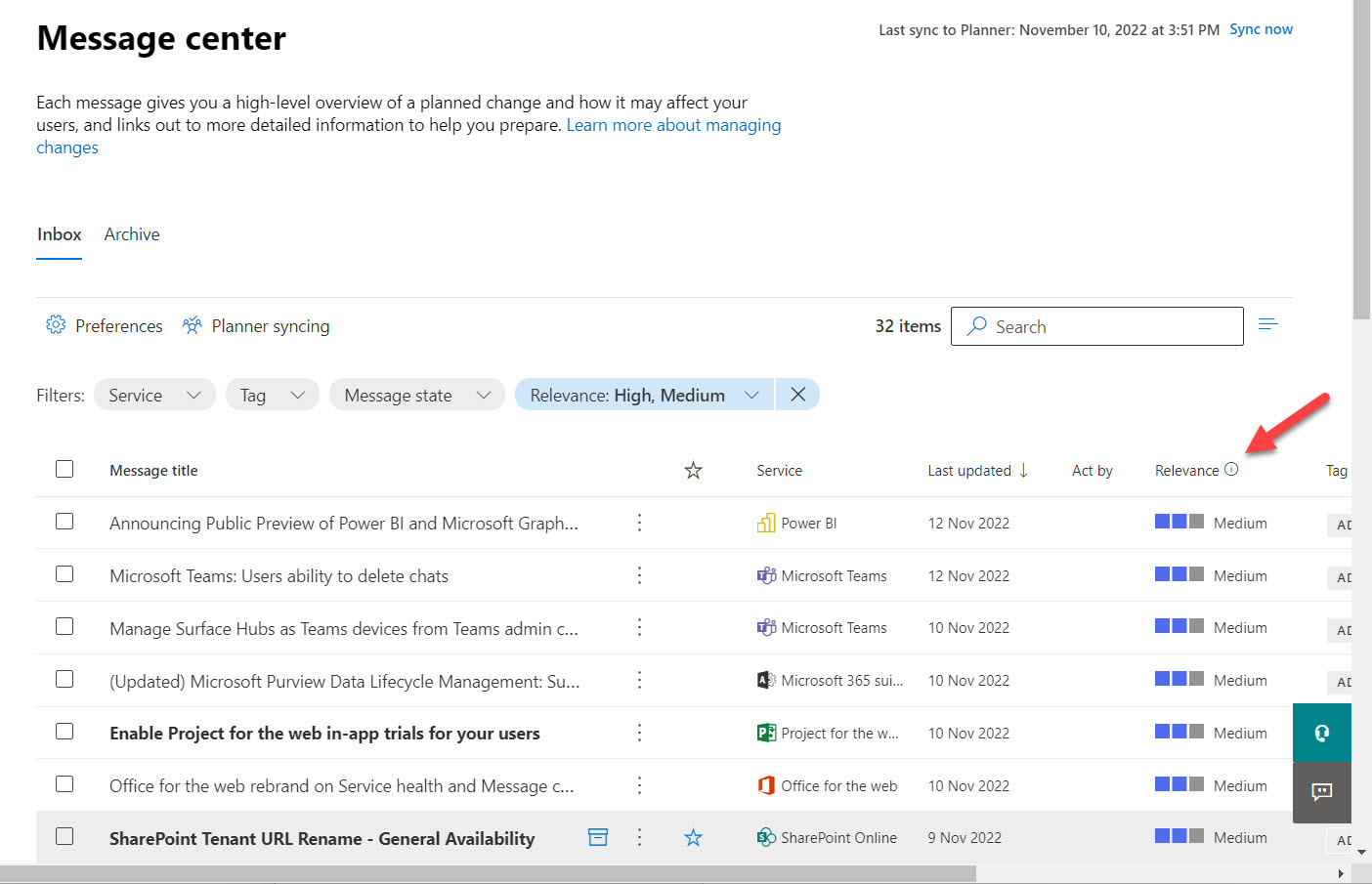
Microsoft 365 message center notifications now boast a “relevance recommendation.” This is a visual marker computed by Microsoft based on aspects of the change. It’s intended as a way to highlight important changes so that administrators can dedicate more time to understanding the impact of these changes on their tenants. Sometimes the recommendation isn’t perfect, but you can tell Microsoft what you think and go ahead with your own assessment of how important any individual change really is.
A new Software Updates page in the Microsoft 365 admin center is intended to help tenant administrators keep an eye on what Office and Windows software people are using. As you’d expect, the page offers no details about non-Microsoft clients connected to Microsoft 365. That’s OK, except when work is needed to make sure that clients can cope with the effects of a massive change, like the October retirement of basic authentication for seven email connection protocols.
Message center notification MC392289 highlights the need to keep the .NET Framework and the Edge WebView2 components updated to make sure that the Teams meeting add-in works with “degradation.” No further information is offered as to why Microsoft needs to sound this warning several years after introducing the Teams meeting add-in.
The message center notifications posted in the Microsoft 365 admin center are an invaluable source of information about change in a tenant. It’s curious that some administrators don’t think they have the time to keep abreast of the changes reported in these notifications. Microsoft is steadily improving the quality of what’s posted, but delayed features remain and issue.
With the demise of the AzureAD and MSOL PowerShell modules on the horizon, it’s time to figure out how to upgrade scripts to use cmdlets from the Microsoft Graph PowerShell SDK. This article books at basic account management and shows how to update, delete, restore, and find Entra ID user accounts using SDK cmdlets.