A recent blog from the Microsoft Digital (IT department) discusses the preview implementation of container management labels for security groups. The implementation is limited because it encompasses just one control: the ability to have guest accounts in the membership of security groups. However, just that limited control is sufficient to stop unintended access to sensitive information by guest accounts, and that’s a very good thing.
License insights is a new feature in the Entra admin center. The Microsoft 365 admin center also shows some license insights in a dashboard card. The two views don’t line up. This isn’t very surprising because different teams generated the information, but it would sure be nice if Microsoft delivered comprehensive license reporting for Microsoft 365 tenants, including the Entra premium licenses.
Entra ID uses an eventually consistent multi-region database architecture. PowerShell code that fetches and updates Entra ID objects needs to interact with the database in the most efficient manner. This article illustrates some guidance from Microsoft engineering with examples from the Microsoft Graph PowerShell SDK. I’m sure your scripts already use these techniques, but if not, we have some helpful pointers.
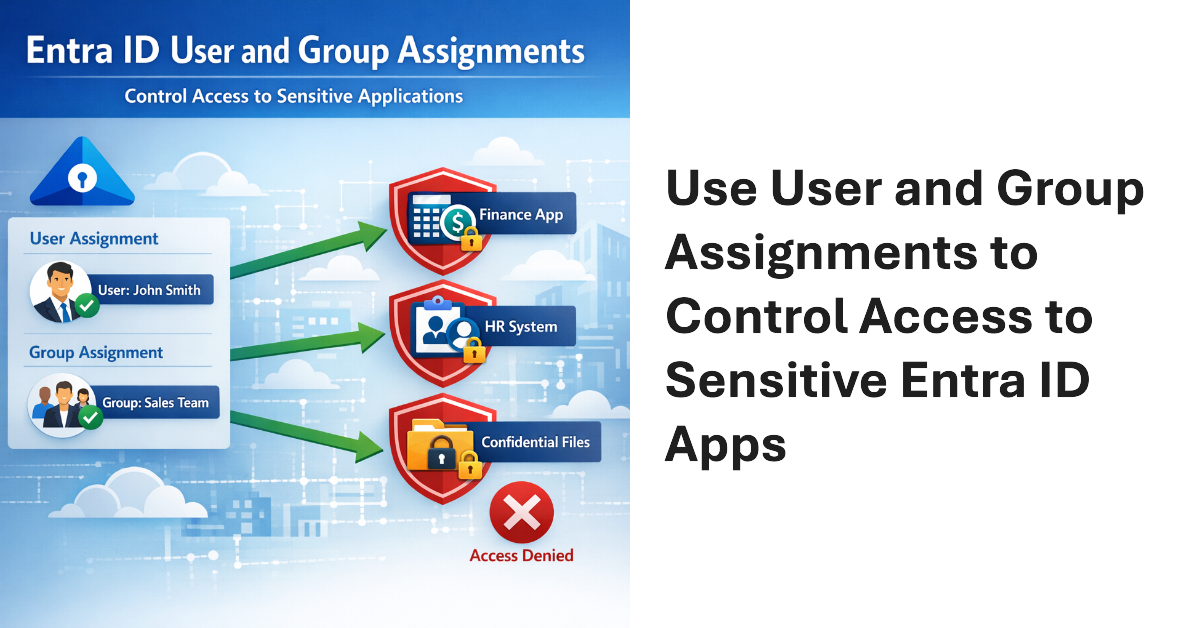
User and Group assignments can be added to Entra ID applications. Once assignments exist for an application, only assigned users can access that application. This method is a good way to secure access to applications that have consent to use high-profile permissions like Sites.FullControl.All or Mail.Read. Microsoft 365 tenants should consider how to use assignments to control user access to applications.
Microsoft disclosed that Entra ID login events were missing from Microsoft Defender for Cloud Applications for nine months — and waited more than three months after the fix to tell customers. Here’s why that matters and what you should do about it.
Microsoft released the preview of the Entra ID Backup and Recovery solution to tenants on 19 March 2026. Although the software is functional in tenants, Microsoft didn’t make a big announcement. We’ve spent the last few days testing backup and recovery and put together the major points about the new solution, which is doubtless going to be welcomed by tenants if not by backup ISVs.
This article explores how to use Entra ID audit records to create a weekly report about role assignment additions and deletions. After deciphering the information contained in the audit records, it’s easy to generate a report showing who made the assignments and if any critical role assignments are in the mix. We can then email the report to interested parties, all with some relatively simple PowerShell.
Microsoft is rationalizing the options to revoke sessions for a user account in the Entra admin center by removing an old revoke MFA sessions button. That seems like a perfectly reasonable thing to do. When administrators want to revoke sessions for an account, the best way is to create a PowerShell script to perform the necessary steps. That way you don’t need to worry about buttons.
Microsoft has released a set of security benchmark recommendations for Microsoft 365 tenants that it calls baseline security mode. The recommendations cover authentication, file access, and Teams and the idea is that these are settings that Microsoft believes have proven their value over the years. The only criticism that you might have is about the potential clash for conditional access policies, but that’s not serious.
The Entra ID Governance solution includes a workflow to detect and remove inactive user accounts. Sounds good, but the same can be done with PowerShell if you want to avoid the cost of Entra ID Governance licenses or want to create a bespoke workflow that’s better suited to the business needs of the organization. Azure Automation would be a good way to process this workflow.
Entra ID has long supported soft-deleted Microsoft 365 Groups. Now support is available to list and restore soft-deleted security groups in both the Entra admin center and cmdlets from the Microsoft Graph PowerShell SDK. The update is very welcome as it fixes a big recovery gap in the Entra ID story. Too many important security groups have been deleted in error, much to the chagrin of administrators.
The Entra ID password protection policy contains settings that affect how tenants deal with passwords. Entra ID includes a default policy that doesn’t require additional licenses. Creating a custom password protection policy requires tenant users to have Entra P1 licenses. As explained in this article, once the licensing issue is solved, it’s easy to update the policy settings with PowerShell.
A recent change has exposed the applications used by the My Sign-ins portal for use in conditional access policies. This article discusses the app-centric nature of Microsoft 365 and Entra ID and why it’s important that the newly-revealed set of applications are available for conditional access processing, just in case the Entra ID agents planned by Microsoft can’t optimize your policies.
Guest account management should be a part of every Microsoft 365 tenant administrator’s checklist, unless the tenant has no guests. That’s possible but given the way that workloads like Teams and SharePoint Online create new guest accounts, the average tenant is likely to have quite a few guests. The question is how to manage guests – with Microsoft’s tools or using tenant-designed PowerShell scripts?
The Entra ID Keep Me Signed In (KMSI) feature creates persistent authentication cookies to allow users to avoid sign-ins during browser sessions. Is this a good or bad thing and should Microsoft 365 tenants enable or disable KMSI. I think KMSI is fine in certain conditions and explain my logic in this article. Feel free to disagree!
The Org Settings section of the Microsoft 365 admin center has a new People Settings section where you can choose properties for the Microsoft 365 profile card instead of using PowerShell. The kicker is that the old method of using Exchange custom properties to customize what appears on the profile card is being replaced with standard Entra ID properties. A migration is needed, and it’s easily done with PowerShell.
Three new Graph API resources provide easy access to Entra ID authentication method summary data. The information is helpful to understand the type of sign-ins that happen, and the authentication methods used by user connections. The article includes a script based on the MFA sign-in summary to highlight non-MFA connections and the apps users connect to.
If you use the Microsoft Graph PowerShell SDK, you don’t need to worry about obtaining an access token because SDK cmdlets include automatic token management. Although you don’t need to know the details of the access token used in an SDK session, it’s possible to find and examine its contents, and even use the token with a Graph request. It’s a nice to know thing that you’ll never need in practice.
The Conditional Access Optimization Agent is one of 6 Security Copilot agents unveiled by Microsoft on March 24, 2025. The idea is that the agent can optimize CA policies by observing the connectivity behavior within a tenant. The agent can suggest how to fill gaps in CA coverage, detect new users and apps, and generally be helpful. Is it worth it? Experience will tell…
Microsoft 365 users can connect their OneDrive for Business account to ChatGPT. This is not a great thing because it exposes the potential for sensitive corporate information to be exposed outside the organization. How can you block ChatGPT Access to OneDrive? The best way is to stop people from using the ChatGPT app. If that’s not possible, make sure to encrypt confidential files with sensitivity labels.
A new people administrator role is available in Entra ID. The new role allows holders to manage settings associated with people, like pronouns and custom properties for the Microsoft 365 user profile card. The people administrator role is a less privileged way to assign responsibilities for people actions and removes the need to assign more privileged roles like User administrator. Time for a role review!
Entra ID allows unprivileged users to update the user principal name for their accounts via the admin center or PowerShell. It seems silly because no justification for allowing people to update such a fundamental property is evident. Perhaps Microsoft has some excellent logic for allowing such updates to occur, but blocking access seems like the right thing to do.
This article describes how to create eligible and active PIM role assignment requests using cmdlets from the Microsoft Graph PowerShell SDK. Although the PowerShell code is straightforward, Microsoft recommends using the Entra admin center for Privileged Identity Management. But you can automate the management of role assignment requests if you want to.
MC705357 (9 Jan 2024) says that the dynamic group rule builder in the Entra ID and Intune admin centers no longer supports the contains and notContains operators. There’s no real cause to worry because existing rules continue to work and if you need to use contains or notContains in a membership rule, you can edit the rule manually.
A question came in about how to report admin consent requests as viewed through the Entra ID admin center. PowerShell does the trick, once you know how. The key thing is to find the right cmdlet to use. Once you know that, the rest is pretty easy as we explain in this article.
Entra ID includes a registration campaign feature to help organizations move users to stronger authentication methods like the Authenticator app. Running campaigns is a good thing, unless you decide to do it when the administrators are away from the office (like me) or users are unprepared. But it is time to get rid of SMS and voice responses to MFA challenges, so maybe you should schedule a campaign soon?
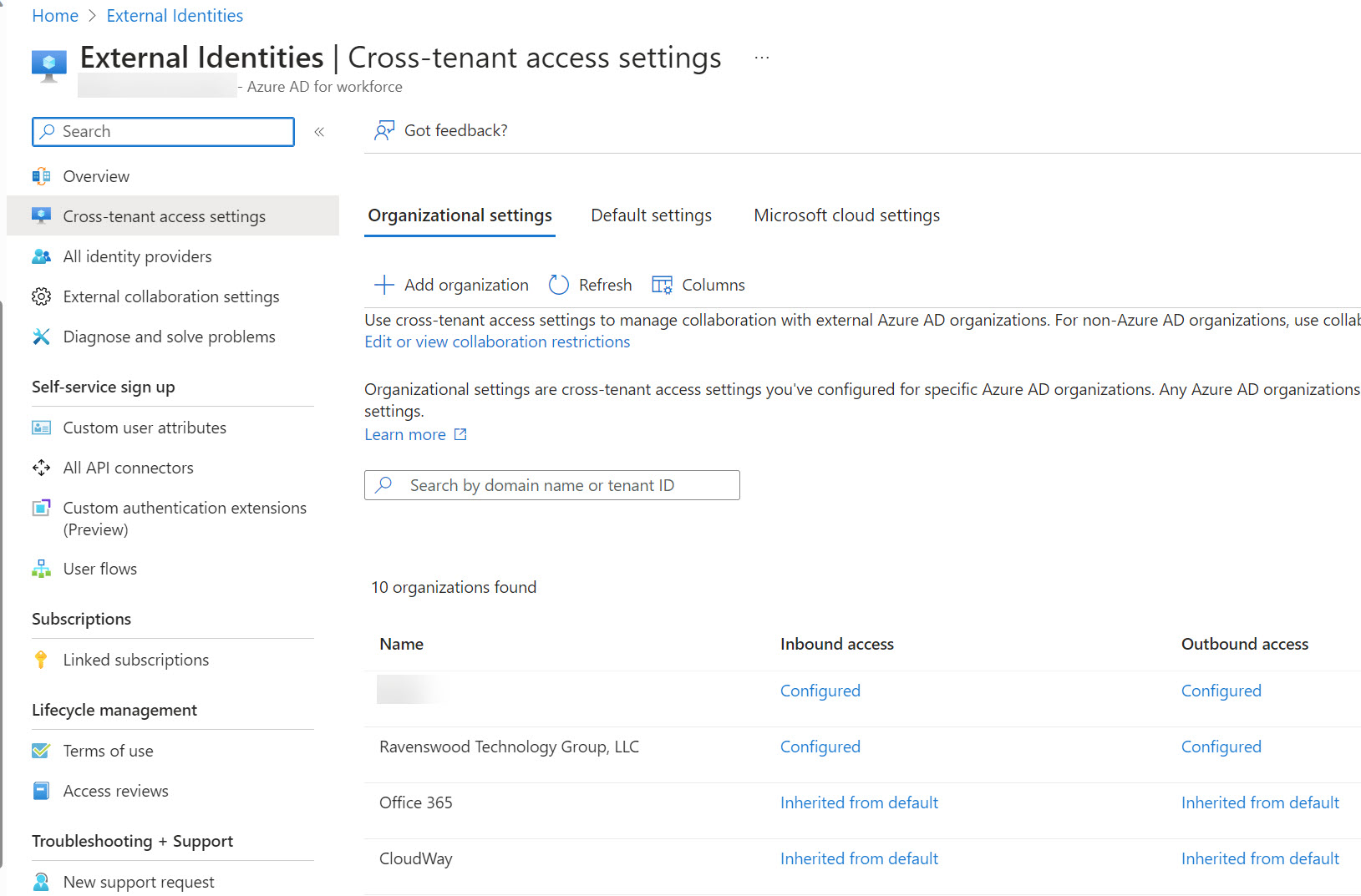
Microsoft announced three changes to Entra ID cross-tenant access settings that will improve how the settings work for large enterprise tenants in particular. One of the changes improves the blocking of Entra ID B2B Collaboration invitations extended to allow guest users access resources in a tenant. When Entra ID evaluates whether it should issue an invitation, it now takes the blocklist (if set) in the B2B collaboration policy and cross-tenant access settings into account. It’s the way things should have worked from the start.
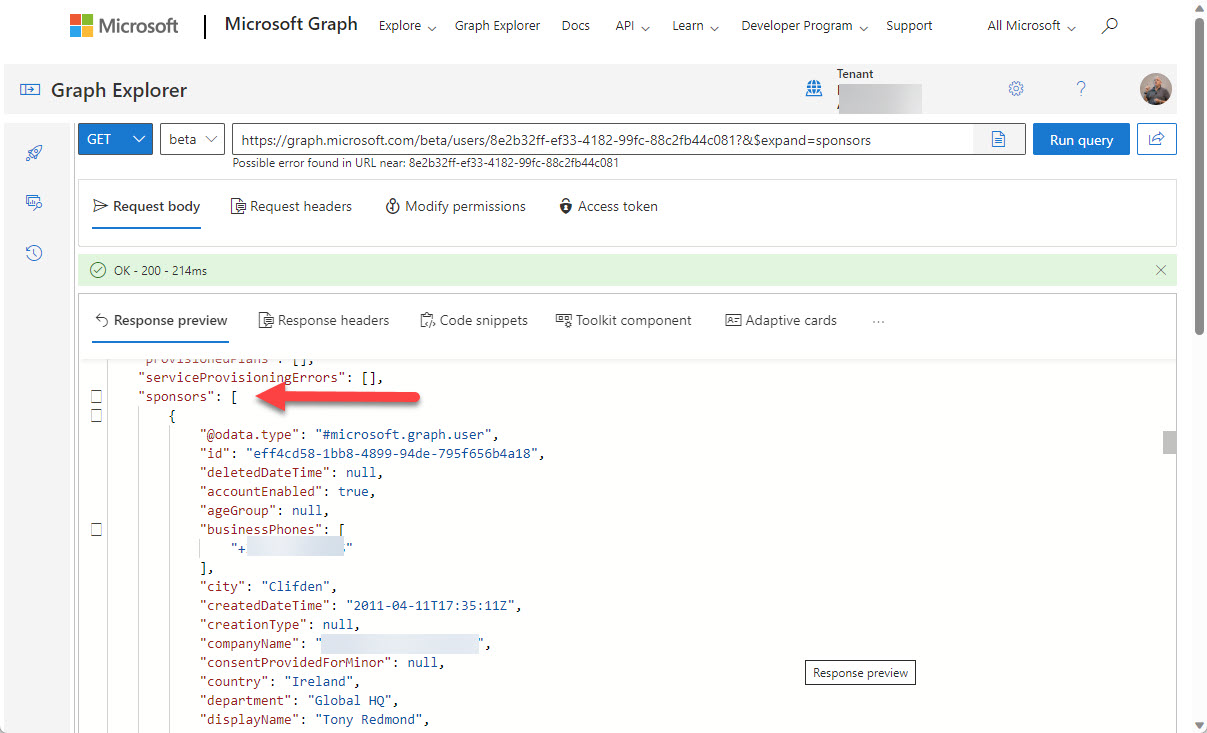
You can now define Entra ID guest account sponsors using the Entra ID admin center or PowerShell. A sponsor is an account or group that knows why a guest account exists. During operations like account reviews of the membership of a Microsoft 365 group, sponsors can help group owners decide if guest accounts should continue as members or should be removed. I’m sure others will come up with ideas for using guest account sponsors, but that’s what we have for now.
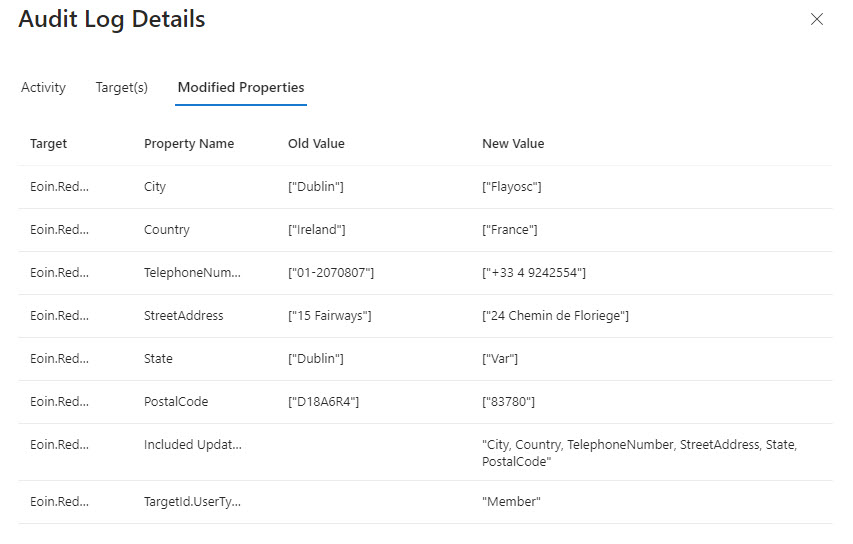
A Twitter discussion about how to audit user account changes revealed that Entra ID does not capture details of changes to the usage location for an account. The possibility existed that the data might be present in the information ingested from Entra ID into the unified audit log, but that turned out not to be the case. Even if some properties are missing, a PowerShell script demonstrates the principle of how to report user account changes (old and new properties). But it would be nice if Entra ID captured details about changes to the UsageLocation property.
PIM, or Privileged Identity Management, is a solution for managing the assignment of privileged Entra ID roles to users and groups. PIM role assignments can be active or eligible. If you report “normal” role assignments, you only see the currently active set. Some more processing is needed to fetch the PIM assignments. Here’s our version of a script to do the job for holders of the Exchange administrator and Global administrator roles.
Outlook’s Org Explorer (available in Insider builds) brings together information from multiple Microsoft 365 sources to help users understand the people they work with in an organization. It’s like an Office 365 profile card on steroids, but only for user accounts as guest accounts and other external people are ignored. In other news, roaming signatures for Outlook desktop are getting closer as OWA now supports the creation and use of multiple web signatures, all of which can be used by Outlook desktop.
Access tokens are an important part of accessing data using modern authentication through APIs like the Microsoft Graph. But what’s in an access token and how is the information in the access token used by PowerShell when the time comes to run some Graph queries in a script? In this article, we look behind the scenes to find out what’s in the JSON-structured web tokens issued by Entra ID.
The Entra ID Keep Me Signed In (KMSI) feature uses a persistent cookie to allow users close and reopen browser sessions without sign-ins. If you don’t want to use KMSI, you can update Azure AD company branding to remove the option. Users will then have to reauthenticate each time they start a browser session. The decision to disable or keep KMSI is highly tenant-specific and depends on how authentication happens.
Service principal sign-in data from Entra ID is now accessible through a Microsoft Graph API. This means that you can analyze sign-in data to locate problem apps and remove old or unwanted service principals from your Microsoft 365 tenant. It’s time for spring cleaning!
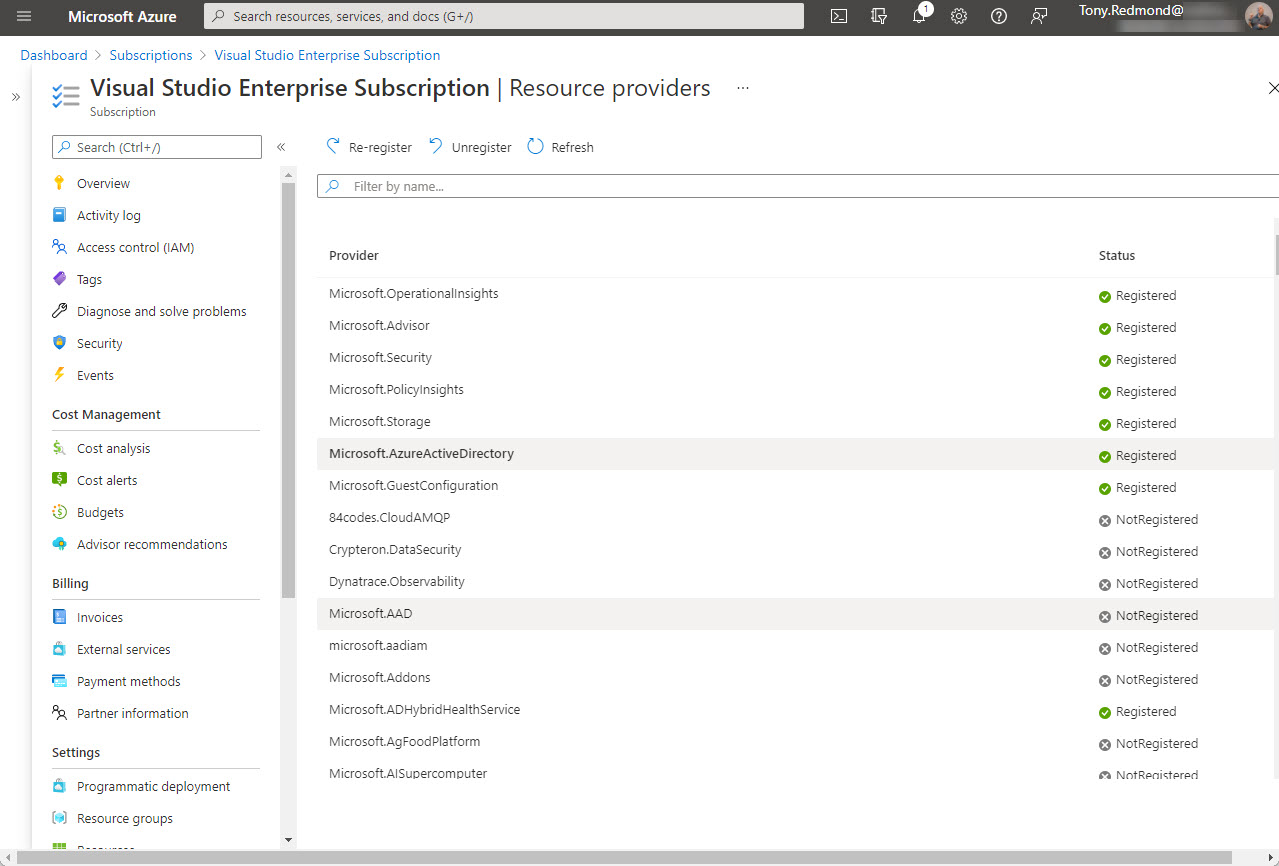
Office 365 tenants using Entra ID external identities (like Entra ID B2B Collaboration guest accounts with apps like Teams) are moving to a monthly active users (MAU) billing model. The new model replaces the 1;5 ratio for Entra ID premium licenses used up to now. Microsoft allows tenants to have the first 50,000 unique external identities free of charge each month and bills for access thereafter. If you don’t already have an Azure subscription, you’ll need one to link to Entra ID. Linking the subscription should be an easy task, until it’s not…
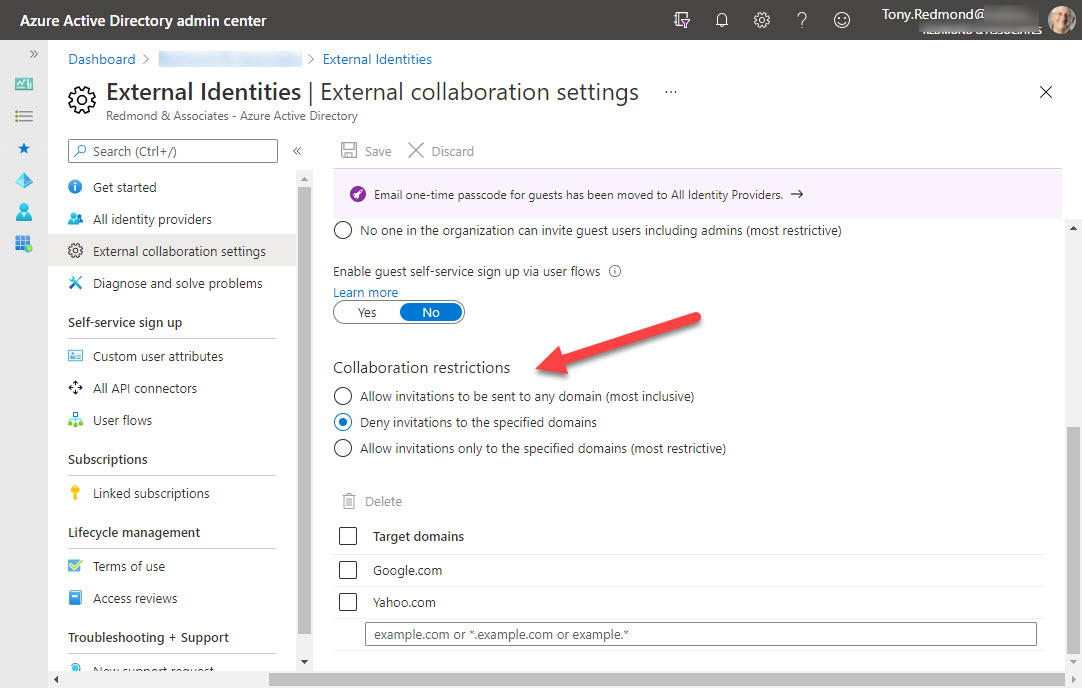
Azure B2B collaboration is used by Microsoft 365 Groups-based apps like Teams, Planner, and Yammer to control the creation of new guest accounts. You can update settings in the Azure AD portal to stop new accounts from specific domains or restrict guests to a list of known domains. But before you go ahead and update the settings, it’s a good idea to know where existing guest accounts come from. It’s easy to create a report with PowerShell. The next step might be to remove guests from offending domains.
By default, the Groups policy for an Office 365 tenant allows group owners to add guest users to group membership. You can block this access if necessary, but it’s probably not what you want to do as blocking brings guest access to a complete halt across the tenant.
Teams supports the ability to create org-wide teams, but only if your tenant has fewer than 10,000 accounts. It’s a neat idea, if you can use it, but if your organization spans more than 10,000 accounts, there are other ways to foster company-wide communications.