A little known fact about the Graph Explorer utility is that you can use it to sign into a tenant using a guest access. This might or might not be a good idea, but if you don’t want people to do this, it’s easy to block guest access by either disabling user access to the app (crude) or using a Conditional Access policy (much nicer).
A new preview feature allows the resources available to an Azure AD guest account to be reassigned to another email address. It’s a nice feature, but Teams has some problems with it at present. On the upside, everything works great with SharePoint Online and Planner, and we’re sure that Microsoft will fix the problem with Teams soon.
You can create an Azure AD Access Review for all guests in teams and groups in your tenant and then see what’s happening with the Graph API. In this case, we use PowerShell with the API to grab the access review data and create a report about the overall status of the review in a tenant.
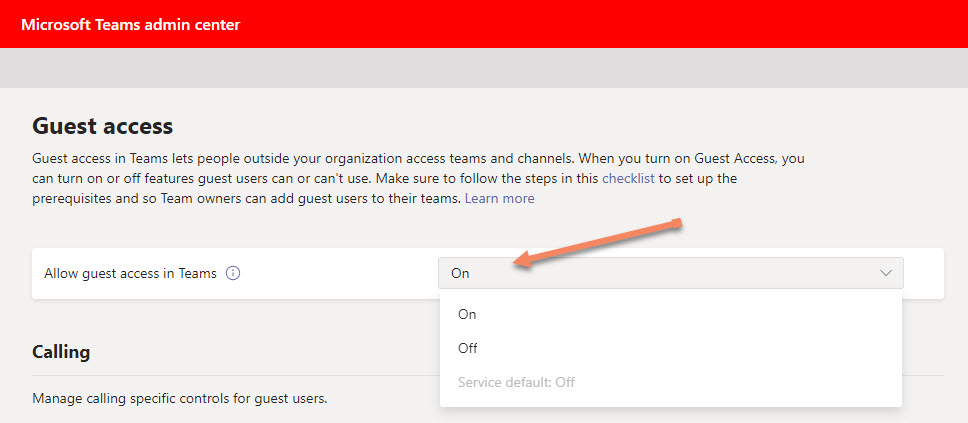
Microsoft is changing the default setting for guest access to Teams from Off to On. This won’t affect tenants already using Teams, but it’s a good opportunity to review how guest access is used in tenants and consider whether existing guest accounts are needed or can be removed. This post offers some ideas about using policies to control guests and how to check what these accounts are used for.
You can apply an Office 365 Sensitivity Label to control different aspects of Groups, Teams, and Sites. One of the settings controls whether guest users are allowed in group membership. We explain how to use PowerShell to search groups assigned a label to block guest access for existing guests, just in case you want to remove them.
Many Microsoft 365 Groups and Teams are used to hold confidential information. Sometimes you don’t want guest members to have access to the information. A variety of methods are available to control guest access.