Microsoft announced that they are rebranding Azure AD to become Microsoft Entra ID. This is just a name change and no functionality or licenses are affected. It’s simply yet another Microsoft rebranding exercise like Microsoft 365, Purview, and Defender. The name change will start in the latter half of 2023 and be completed by 2024.
SharePoint Online is embracing Azure AD more closely by forcing new tenants to use the integration between the two Microsoft 365 components. In addition, site sharing will use the Azure AD invitation mechanism instead of SharePoint’s own code. The changes make a lot of sense and shouldn’t cause much disruption for tenants. It’s a good reminder to check the relevant policies that control external access via Azure B2B Collaboration.
In most situations, it’s a good idea to enable Azure AD accounts for SSPR (self-service password reset) to avoid the need for administrators to update user accounts when things go wrong. This article explains how to report accounts that are not yet set up to use SSPR. It’s a check that should happen regularly, perhaps with the aid of Azure Automation.
A new setting for Azure AD conditional access policies allows organizations to dictate the authentication strength of accepted connections. This is part of a Microsoft effort to move MFA-enabled Azure AD accounts away from the relatively insecure SMS-based challenges to methods that are less susceptible to attack.
By now, Microsoft 365 tenant administrators realize the need to understand how apps use consent to access Microsoft 365 data. App certification helps by reassuring tenant administrators that third-party apps meet certain criteria set by Microsoft. Achieving Microsoft 365 certification is the highest bar in the program. It’s just a pity that many of the apps now appearing in the ecosystem don’t achieve this level of app certification.
Access tokens are an important part of accessing data using modern authentication through APIs like the Microsoft Graph. But what’s in an access token and how is the information in the access token used by PowerShell when the time comes to run some Graph queries in a script? In this article, we look behind the scenes to find out what’s in the JSON-structured web tokens issued by Entra ID.
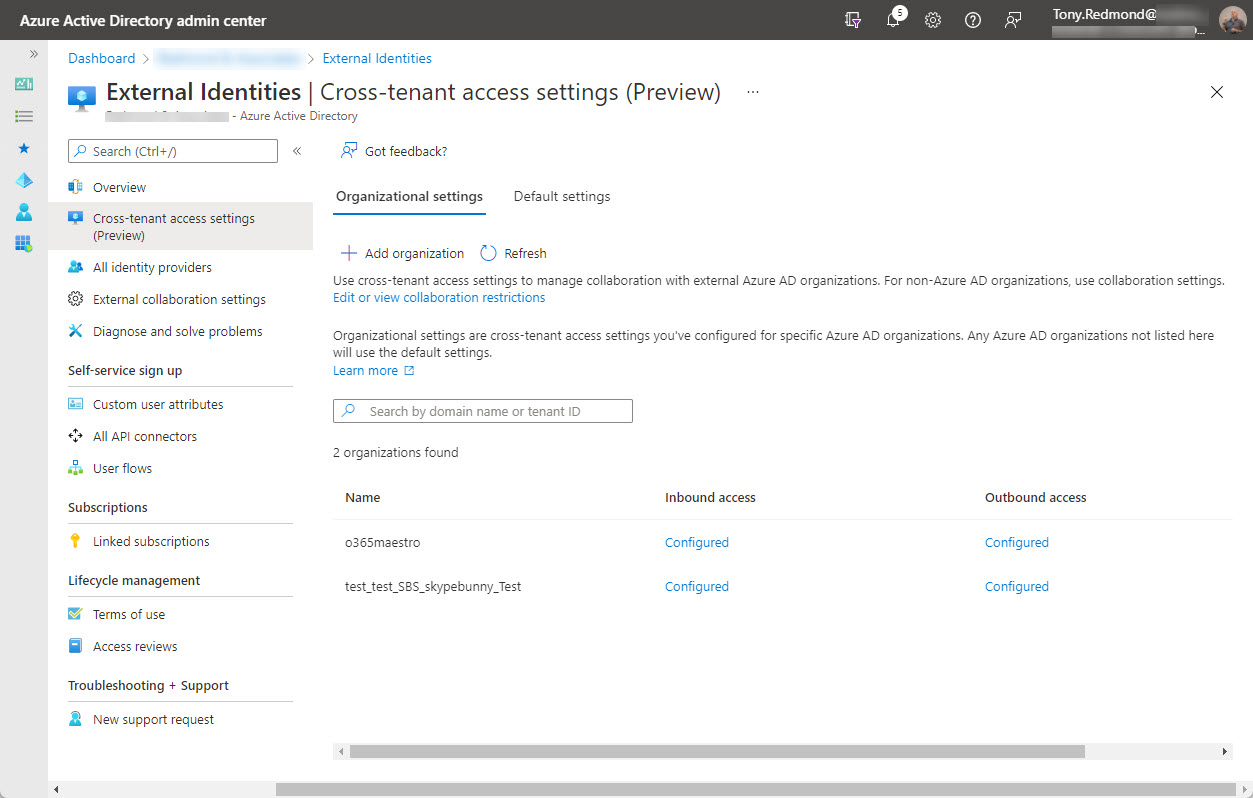
On February 7, Microsoft announced the preview of Azure AD cross-tenant access, a new capability to allow users obtain credentials in their home tenant and use these credentials to access resources in other Microsoft 365 organizations. Microsoft Teams Connect (aka shared channels) is likely the first app to use cross-tenant access, with public preview of that feature expected in March 2022.
Service principal sign-in data from Entra ID is now accessible through a Microsoft Graph API. This means that you can analyze sign-in data to locate problem apps and remove old or unwanted service principals from your Microsoft 365 tenant. It’s time for spring cleaning!
You might never need to use a break glass account, but if the need arises, you’ll be glad that you had the foresight to anticipate that bad things can happen and create a break glass account for your Microsoft 365 tenant. This article describes why you might want one or more of these accounts, their characteristics, some pitfalls to avoid, and how to check that the break glass accounts aren’t being used.
Finding the age of a Microsoft 365 tenant isn’t an important administrative operation. However, understanding how to retrieve this information (if asked) is an interesting question, which is why we spent several hours playing around with PowerShell and the Microsoft Graph to figure out how to answer the question. It’s the kind of in-depth analysis we do all the time to build content for the Office 365 for IT Pros eBook.
On January 10, Microsoft announced that the base Office 365 workloads support Continuous Access Evaluation (CAE) for critical Azure AD events like password changes or account deletions. Although you can take CAE even further with conditional access policies, giving Exchange Online, SharePoint Online, and Teams the ability to react to critical events in almost real-time is a very big thing indeed.
Microsoft pushed out version 2.0.88.0 of the AAD Connect synchronization utility earlier this month. Unfortunately, the new software removes disabled on-premises user accounts from Azure AD, which means that on-premises shared mailboxes disappear for cloud users. Microsoft has released version 2.0.89.0 but maybe it’s better to go back to a version that you know works. At least until after the holidays.
A reader asked how to find when Azure AD accounts received certain licenses. As it turns out, this isn’t as simple as it seems. PowerShell can tell use when user accounts are enabled with service plans, but to get dates for licenses (products or SKUs), we need to go to the Graph API, and those dates aren’t quite there yet. In any case, it’s an interesting question which deserves some exploration to see if we can find an answer.
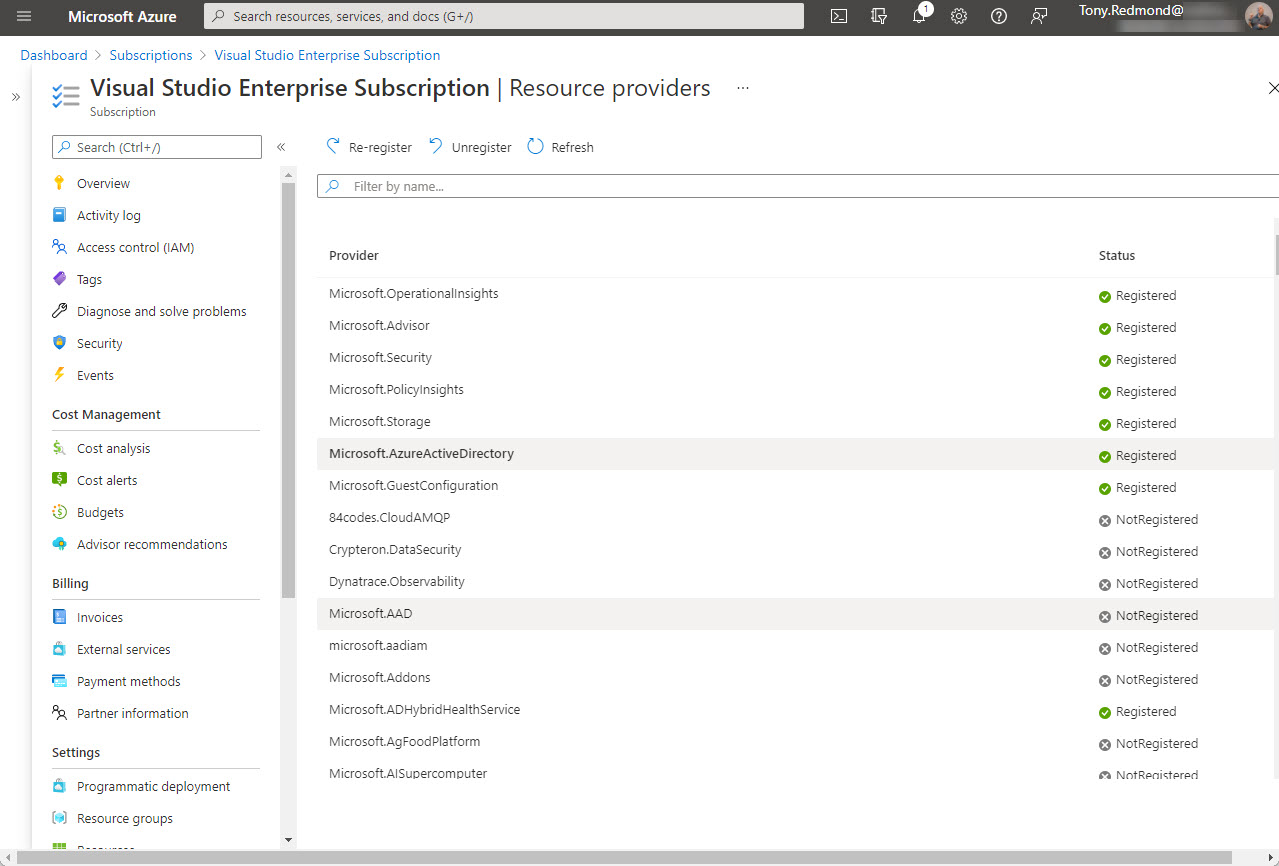
Office 365 tenants using Entra ID external identities (like Entra ID B2B Collaboration guest accounts with apps like Teams) are moving to a monthly active users (MAU) billing model. The new model replaces the 1;5 ratio for Entra ID premium licenses used up to now. Microsoft allows tenants to have the first 50,000 unique external identities free of charge each month and bills for access thereafter. If you don’t already have an Azure subscription, you’ll need one to link to Entra ID. Linking the subscription should be an easy task, until it’s not…
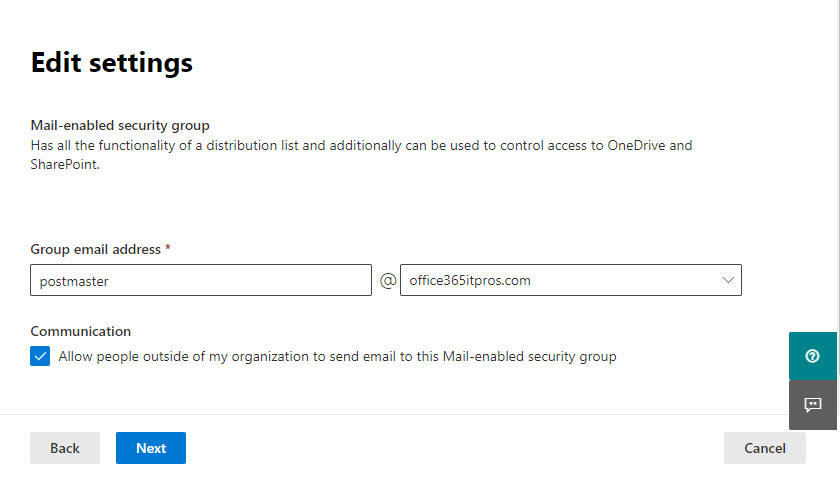
Azure AD administrators should be able to assign a reserved alias to a new group. At least, that’s what the documentation says. As it turns out, this isn’t strictly true as there are places where administrative interfaces (GUI and PowerShell) block any attempt to use reserved aliases. Does this matter? Probably not, unless you like consistency… which we do!
The preview of a new app governance add-on for Microsoft Client App Security gives Office 365 administrators insight into Graph-based apps. The add-on depends on information gathered from Azure AD and MCAS to generate insights about apps and their usage, including highlighting apps which are overprivileged or highly privileged. Although you can do some of the auditing yourself, the add-on makes it easier. It’s a preview, so some glitches are present.
A preview for Sensitivity Labels show how they can use Azure AD authentication contexts and conditional access policies to protect SharePoint Online sites. Although you can link conditional access policies to sites with PowerShell, it’s a lot easier to make the connection through sensitivity labels. Any SharePoint Online site which receives a label configured with an authentication context automatically invokes the associated conditional access policy to protect its contents.
Anyone writing PowerShell code against Azure Active Directory probably uses the Azure AD module. In June 2022, Microsoft will deprecate the API underpinning the Azure AD module. Tenants who want to use PowerShell to create scripts to automate administrative processes will need to move to Graph API calls or use the Microsoft Graph PowerShell SDK. Either way, there’s a bunch of work to do to upgrade scripts.
Without warning (for security reasons), Microsoft stopped the Exchange Online Set-User cmdlet being able to update the work and mobile numbers for Azure AD accounts. We don’t know what kind of security concerns caused Microsoft to take this action, but it might be associated with administrative roles. In any case, this disappointing example of how to communicate with customers might end up with people having to update some PowerShell scripts – and no one likes unexpected work.
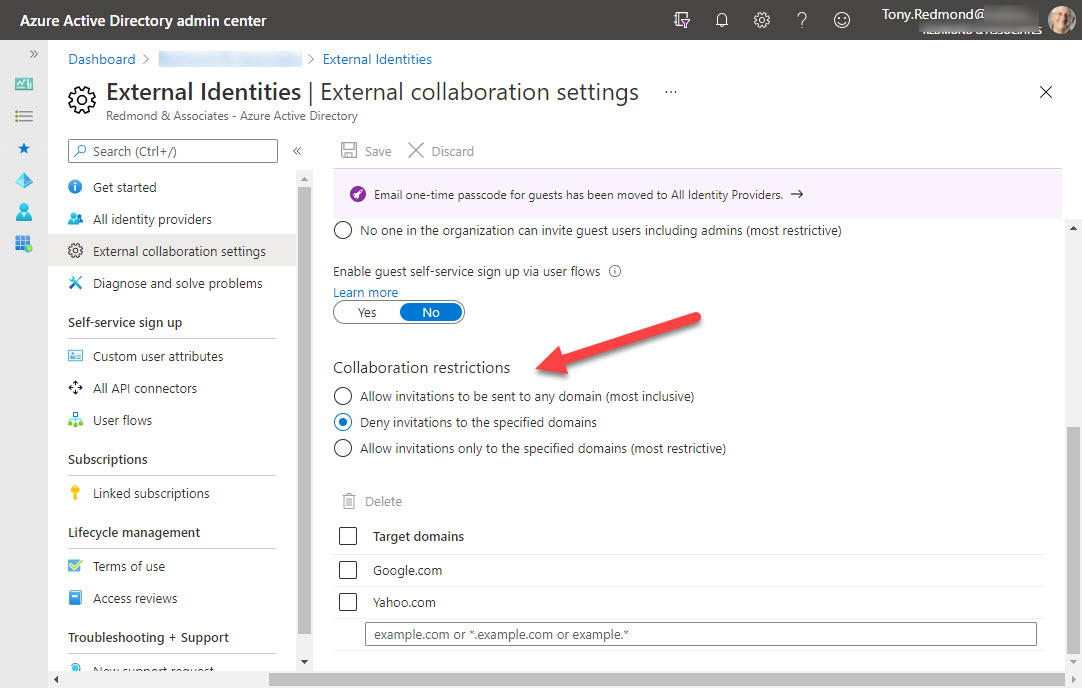
Azure B2B collaboration is used by Microsoft 365 Groups-based apps like Teams, Planner, and Yammer to control the creation of new guest accounts. You can update settings in the Azure AD portal to stop new accounts from specific domains or restrict guests to a list of known domains. But before you go ahead and update the settings, it’s a good idea to know where existing guest accounts come from. It’s easy to create a report with PowerShell. The next step might be to remove guests from offending domains.
Office 365 administrators can update Azure AD guest accounts with photos. Guests can do the job themselves using three PowerShell commands. Other approaches work too, but this is the easiest and quickest method to do the job, especially if you have guest accounts in multiple tenants.
Azure AD holds information about managers and their direct reports. It’s easy for that data to go out of date, so we create a report to tell us who are the managers and how many direct reports they have. Azure AD has some cmdlets to retrieve information about managers and direct reports, but as it turns out, the older Get-User cmdlet is the best way to proceed.
A new preview feature allows the resources available to an Azure AD guest account to be reassigned to another email address. It’s a nice feature, but Teams has some problems with it at present. On the upside, everything works great with SharePoint Online and Planner, and we’re sure that Microsoft will fix the problem with Teams soon.
The Office 365 audit log is packed full of information about what happens inside workloads. New events show up all the time. The question is how to understand what actions these events relate to. We outline a simple procedure to discover the presence of new audit events and dive into the investigation of an event called Consent to application, which is pretty important in the context of recent high-profile attacks.
Exchange dynamic distribution lists allow messages to be sent to sets of recipients determined by a query against the directory. A custom filter is a powerful way to find the right set of recipients. In this case, we want to find mailboxes with certain job titles whose Azure AD accounts are not blocked for sign-in. Here’s how to create the filter, make sure it works, and create the DDL.
Many Microsoft 365 features depend on accurate user account data in Entra ID (Azure AD). Here’s how to use PowerShell to track down accounts with important missing properties. Once you know which accounts need to be updated, it’s easy to insert the missing properties. Boring, but easy…
Over time, you might join several Office 365 tenants as a guest. Some of those Azure AD guest accounts probably won’t be needed forever and you want to clean them up. This is easy for individuals to do through their MyAccount page, which might just be a page that they never knew existed.
Security groups are often used to protect access to resources, but they can’t be used to control membership for Microsoft 365 Groups or Teams. If you want to use AAD security groups to control membership for Groups and Teams, you need to come up with a way to synchronize. PowerShell is available to do the job, and as it turns out, it’s not too difficult.