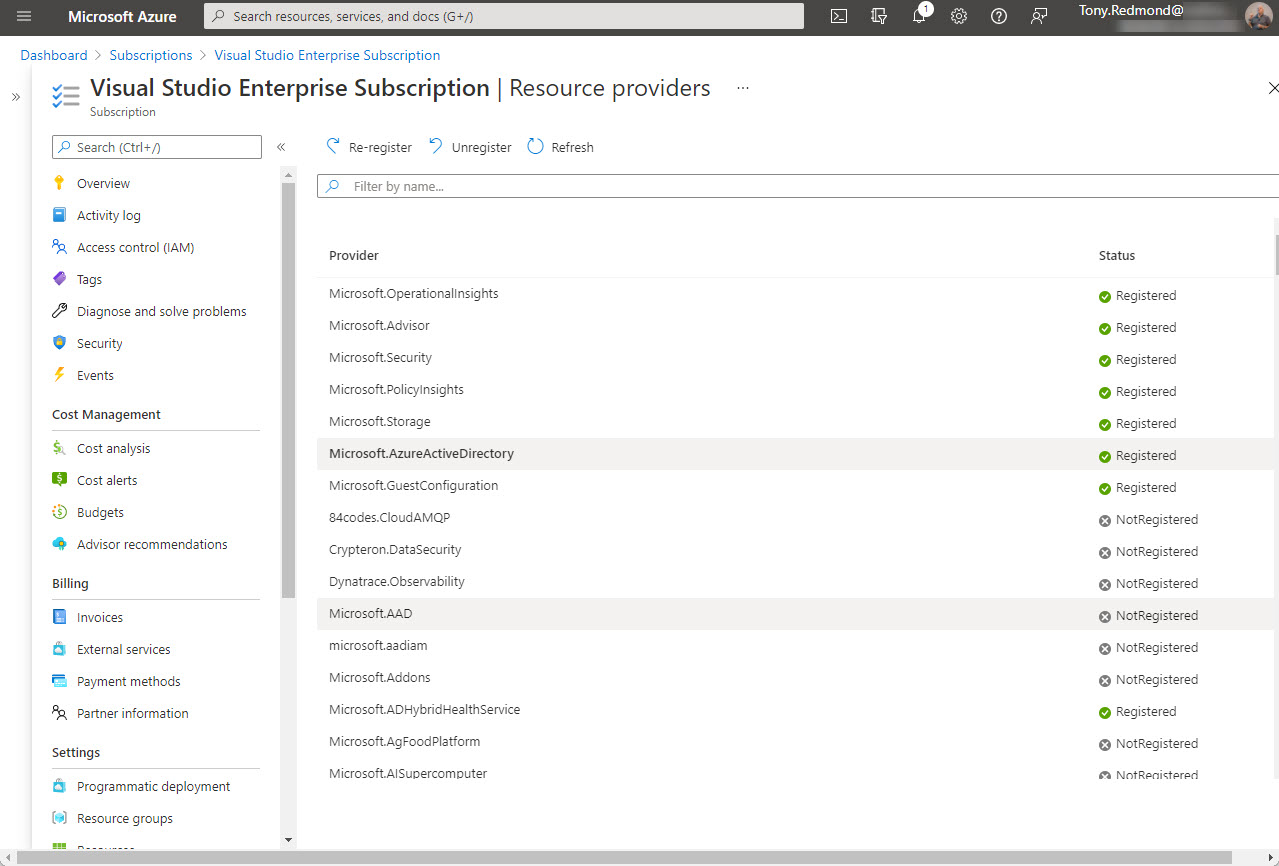
Office 365 tenants using Entra ID external identities (like Entra ID B2B Collaboration guest accounts with apps like Teams) are moving to a monthly active users (MAU) billing model. The new model replaces the 1;5 ratio for Entra ID premium licenses used up to now. Microsoft allows tenants to have the first 50,000 unique external identities free of charge each month and bills for access thereafter. If you don’t already have an Azure subscription, you’ll need one to link to Entra ID. Linking the subscription should be an easy task, until it’s not…
Yammer networks configured in Microsoft 365 mode now support Azure B2B collaboration guest users. Which is nice, if it worked. But it doesn’t for me. Guest access worked for me during the testing phase but now that the feature has reached general availability, it won’t – using the same accounts. It’s odd. Yammer’s implementation of Azure B2B Collaboration has some other quirks too, all of which mean that it’s not very usable.
You can create an Azure AD Access Review for all guests in teams and groups in your tenant and then see what’s happening with the Graph API. In this case, we use PowerShell with the API to grab the access review data and create a report about the overall status of the review in a tenant.
Over time, you might join several Office 365 tenants as a guest. Some of those Azure AD guest accounts probably won’t be needed forever and you want to clean them up. This is easy for individuals to do through their MyAccount page, which might just be a page that they never knew existed.
You can easily add people from outside your Office 365 tenant to the membership of Teams, but some oversight of who those people are and what teams they join is probably needed. This PowerShell script shows how to find records in the Office 365 audit log and figure out if they relate to the creation of new guest accounts before sending email asking to justify the addition of the new account.
Office 365 makes extensive use of Azure Active Directory guest accounts. Implementing a risky sign-in policy is a good idea, but it can have the unfortunate side-effect of suddenly blocking guest accounts that could previously access tenant resources. If blocks happen, they can only be lifted through administrative intervention in the guest account’s home tenant.
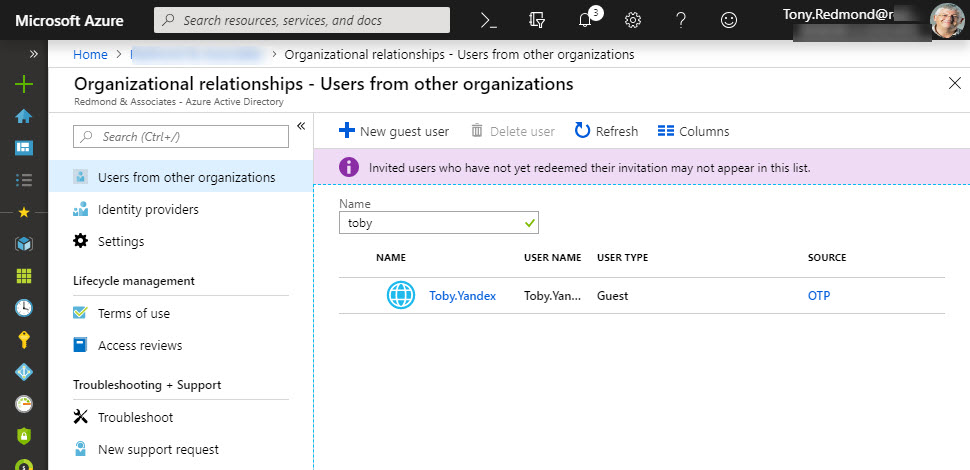
Microsoft has launched email one-time passcodes (OTP) into preview for Azure Active Directory guest accounts. It’s all to do with better collaboration. OTP doesn’t support Teams, Planner, or Office 365 Groups yet, but it can be used to share documents from SharePoint Online or OneDrive for Business.
How many guest users does your Office 365 tenant have? And how many of those accounts are actually used? Given that many Office 365 applications now generate guest user accounts to facilitate external access to content, managing these accounts is a growing concern.
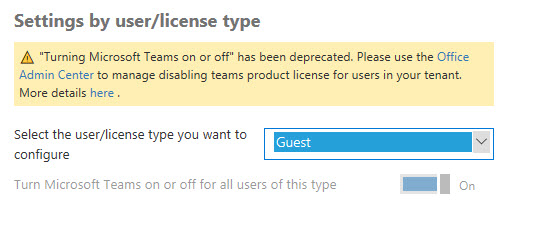
During transitions, things sometimes don’t go so smoothly. Such is the case if you want to enable or disable guest user access to Teams and find that the setting to control the access is no longer available in the Office 365 Admin Center. But PowerShell can control the setting, so that’s the solution to the problem.
Many Microsoft 365 Groups and Teams are used to hold confidential information. Sometimes you don’t want guest members to have access to the information. A variety of methods are available to control guest access.