Adding the ability to search for spoken text in Teams meeting recordings is just one of the new features added after Microsoft moved storage for meeting recordings to OneDrive for Business. A new video viewer and support for 27 additional languages (some different variants of a base language) are also important developments. In this article, we explore how Exchange Online captures the text spoken in Teams meetings, how OneDrive for Business links the text with the video, and how Search can find spoken text from the transcripts.
Microsoft 365 retention policies control how the system removes items automatically from Exchange Online, SharePoint Online, Teams, and other locations. Because these policies are so powerful, it’s a good idea to keep an eye on who makes changes to their settings. The audit log is a natural place to go looking for information about policy updates and while we can find information there, some of the data is oddly formatted or obscured for some reason. Persistence and PowerShell delivers answers, but this is a task way harder than it should be.
The preview of a new app governance add-on for Microsoft Client App Security gives Office 365 administrators insight into Graph-based apps. The add-on depends on information gathered from Azure AD and MCAS to generate insights about apps and their usage, including highlighting apps which are overprivileged or highly privileged. Although you can do some of the auditing yourself, the add-on makes it easier. It’s a preview, so some glitches are present.
Office 365 tenants will soon be able to create adaptive scopes for retention policies. An adaptive scope is nothing more than a filter to select target mailboxes, sites, and Microsoft 365 groups based on some criteria. They’re adaptive because administrators don’t have to update policies as they add new objects. Like other Microsoft 365 Information Governance features which automate some aspect of operations, adaptive scopes are likely to demand Office 365 E5 or Microsoft 365 E5 Compliance licenses.
It is now possible to apply Microsoft 365 retention policies to Teams private channel messages. The messages are in user mailboxes and discoverable due to their properties. All the retention policy must do is find the messages and apply the policy settings, and if an item is expired, remove it from the mailbox. Easy… or is it?
Yammer compliance records are generated by the Microsoft 365 substrate and consumed by features such as communications compliance policies and eDiscovery. In this post, we consider where Yammer compliance records are stored and what they contain and how to use PowerShell to figure out the activity levels of Yammer communities.
A change being made to SharePoint Online in August will make the deletion process for files with retention labels consistent with OneDrive for Business. The intention is to achieve consistency across the two browser interfaces and to remove a little friction for users who might become confused when they SharePoint Online stops them deleting labeled files. Everything will happen in August. We wonder if anyone will notice?
After writing about auto-label policies for Teams meeting recordings, we were asked about how to track the creation of the recordings. The key to be able to report the data us events in the Office 365 audit log. Once you know where to look, it’s easy to find the audit records and extract data about the creation of Teams meeting recordings.
Auto-label policies are a good way to assign retention labels to important files stored in SharePoint Online and OneDrive for Business. The big problem is tracking the progress of auto-labeling. In this article, we explore how to use events logged in the Office 365 audit log to figure out what files are labeled and how long it takes the auto-label policies to process the files. The example explored here is an auto-label policy for Teams meeting recordings.
Teams meeting recordings are now accumulating as MP4 files in OneDrive for Business and SharePoint Online. If you have Office 365 E5 licenses, you can use an auto-label policy to remove recordings after a set period. If you don’t have those licenses and need to remove recordings, you’ll have to come up with another plan, maybe after tracking the creation of recordings through the Office 365 audit log.
Licensing is everyone’s favorite topic. Combine it with information protection and governance and peoples’ eyes glaze over. Even so, it’s important to know what information protection and compliance features need which licenses as you don’t want to get into a position where something stops working because Microsoft enables some code to enforce licensing requirements. This post covers the basics of licensing and how Microsoft differentiates between manual processing and automated processing when deciding if a feature needs a standard or premium license.
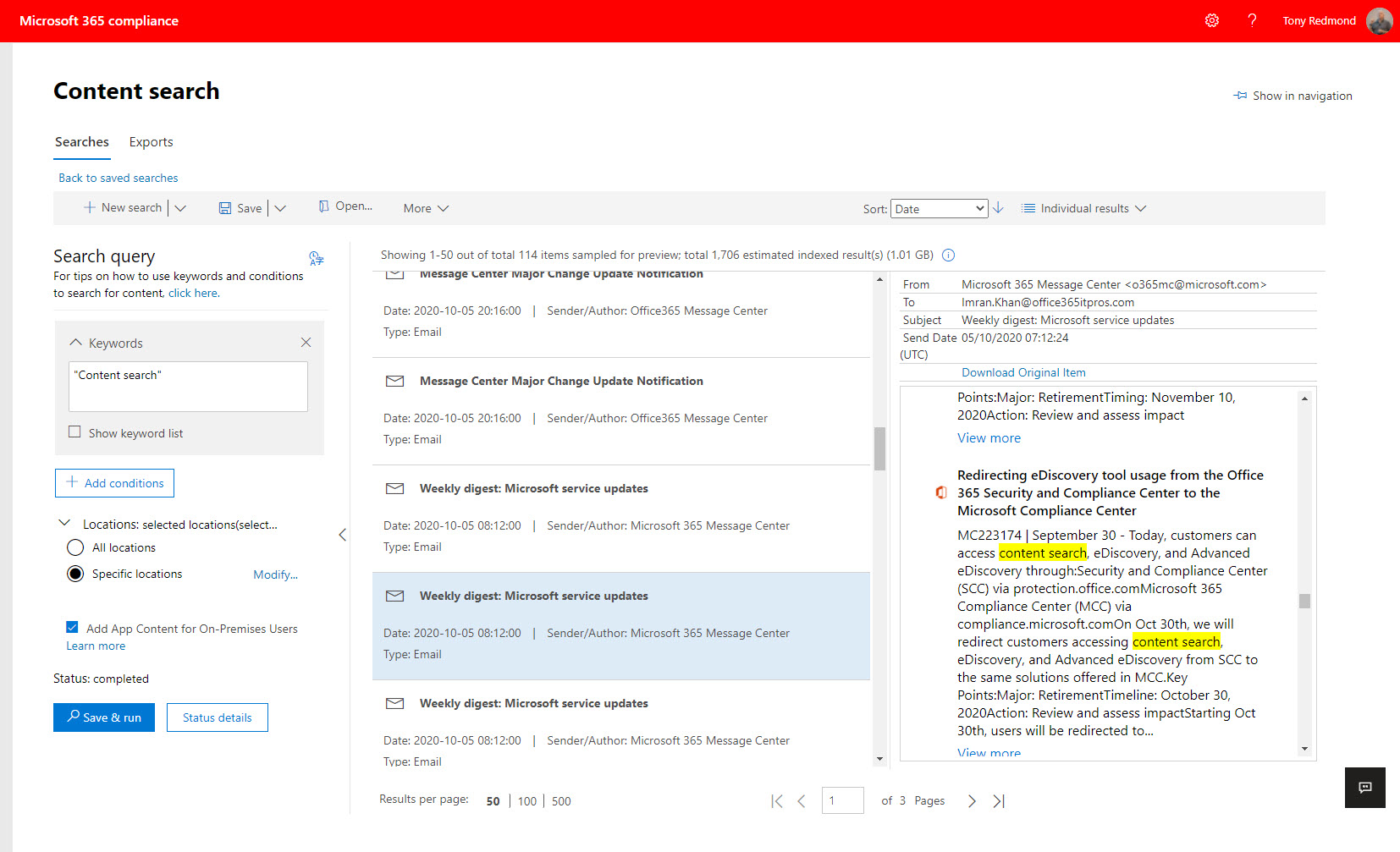
The Microsoft 365 compliance center has a new content search UI. The new UI is prettier than before, but it’s also slower and more buggy. After several years of effort to develop content searches, you’d expect Microsoft to do better. A lot betterr. Unhappily, the beauty of the new interface seems to have distracted the engineers from the problems that become all too apparent when you try to use content searches to do real work. What, if any testing, was done to validate the new UI is unknown.
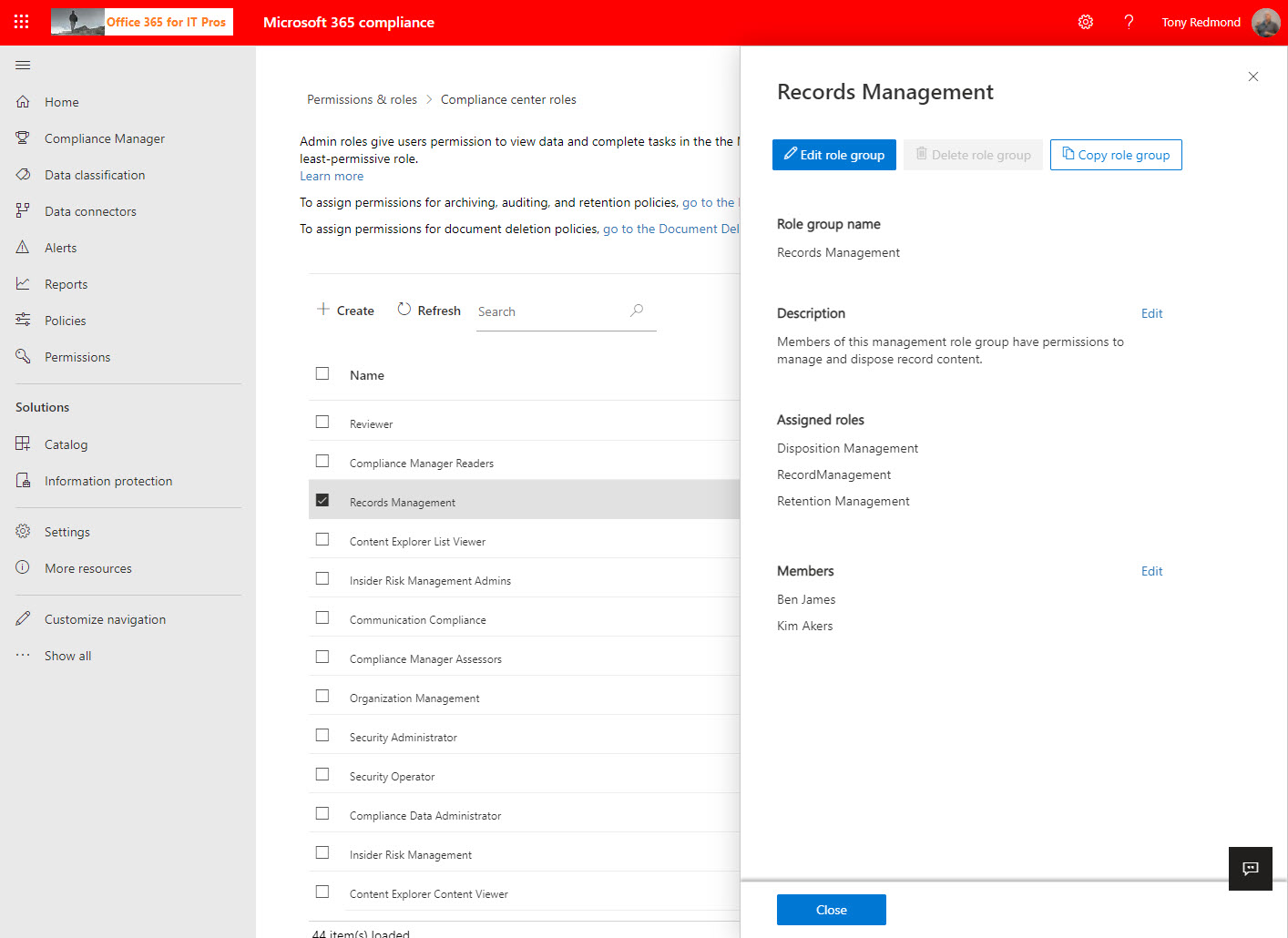
Compliance role groups control access to Microsoft 365 compliance functionality. A new permissions page makes it easier to manage these groups in the Microsoft 365 compliance center, where you can also manage the Entra ID roles used by Microsoft 365 compliance. If you want to generate a report about who holds what role, you’ve got to use PowerShell. The code is easy once you know which roles you want to report.
Microsoft 365 eDiscovery features will respect documented limits from May 10. The changes are likely made to conserve resources consumed by searches against the massive amounts of data now found in Office 365 tenants. The changes probably won’t affect eDiscovery investigators except in reminding everyone that the items shown in search preview are only a representative sample of what can be found by a full search.
Audit records are a great way to gain an understanding of what happens inside Office 365. We use PowerShell to report actions taken with sensitivity labels such as protecting files and containers. The latest development is the addition of support in the Microsoft 365 apps for enterprise (Office desktop) to log audit events when users interact with sensitivity labels. Unsurprisingly, more events are often logged by the desktop apps than their online equivalents.
The Microsoft 365 substrate now captures Teams app card data in compliance records to make the data available for eDiscovery, content searches, holds, and retention. The compliance records are stored in user and group mailboxes. Audit records for card interactions are also logged in the Office 365 audit log. Using compliance records means that some app data context is lost, but at least you can find the information.
Microsoft has released a set of new sensitive information types, used to locate sensitive data by Microsoft 365 DLP policies. Many are country-specific versions of previous generic types (like passports or identity cards). The recommendation is to consider upgrading DLP policies to use the new types to get better (more accurate) matching.
The format of the Teams compliance records generated for personal and group chats and stored in Exchange Online mailboxes is changing. Microsoft is removing a bunch of unnecessary attributes from the records to reduce the processing load on the service to retrieve the attributes from Azure AD. The change is unlikely to affect most tenants. Compliance records for older chats are not affected.
Exchange Online indexes the items stored in mailboxes. Some of the items are partially indexed, meaning that not all of their content is indexable. Microsoft has a PowerShell script to analyze the number of partially indexed items found in mailboxes. The output is kind of esoteric, so we worked it over to create something more understandable.
When you use an Office 365 content search to find items, the results from Exchange Online might include some encrypted attachments. A change means that the attachments can now be decrypted to make it easier for investigators to review the information. It’s a small but important change, just like the update to Edge which stops ClickOnce programs running unless an Edge setting is enabled. All good, clean, honest fun.
Microsoft has made Endpoint DLP generally available. Leveraging Windows 10 workstations and the Edge browser, Endpoint DLP sends signals for evaluation to detect possible violations. The solution requires Microsoft 365 licenses and only supports Windows, so it’s not for every tenant. But those who have Microsoft 365 licenses will find this an attractive solution.
Power Automate (Flow) can forward email from Exchange Online mailboxes to external recipients. This isn’t a great idea if you want email kept within the control of your data governance framework. Power Automate now inserts x-headers in the email it sends, which allows the use of transport (mail flow) rules to detect and reject these messages if required.
Communications compliance policies scan user messages to detect violations of company or regulatory rules. A change introduces support for hybrid users whose mailboxes are on Exchange on-premises servers. The change might not pick up many new violations, but it does increase the coverage and stops some violations sneaking through, which is always a good thing.
When you need to block external access to your most sensitive documents, Office 365 Data Loss Prevention policies and sensitivity labels combine to find and protect the documents. A really simple policy is enough to detect and block external access, and is covered by Office 365 E3 licenses. If you have E5 licenses, you can consider auto-label policies to find and protect sensitive documents at scale.
Support for sensitivity labels is generally available for SharePoint Online. Users can apply labels to classify and protect documents, but a mismatch can happen between labels applied to documents and the sites where the documents are stored. When this happens, SharePoint Online emails site owners to tell them that a mismatch exists.
For compliance purposes, the Microsoft 365 substrate captures copies of Teams messages in Exchange Online mailboxes. The compliance records are indexed and discoverable, which means that they can be found by content searches. However, Teams compliance records are imperfect copies of the real data, which is a fact that seems to have escaped many people.
The SendAs audit event is logged when someone uses the send as permission to send a message from an Exchange Online mailbox. The events are stored in the Office 365 audit log and can be found there with an audit log search. However, things aren’t as straightforward as they are on-premises because some other types of delegated messages turn up in searches. Fortunately, we have a script to help.
Microsoft has released information about high-value Office 365 audit events and audit event retention policies. Both are part of a Microsoft 365 Advanced Audit offering. The MailItemsAccessed event is the first high-value audit event (we can expect more) and the retention policies are used to purge unneeded events from the Office 365 audit log.
The Office 365 compliance framework can now to place holds on Teams compliance records created for conversations in private channels. You simply have to place holds on the mailboxes of members of the private channels and hope that no one removes the members from the tenant. If they do, the hold lapses, which seems like a pity.
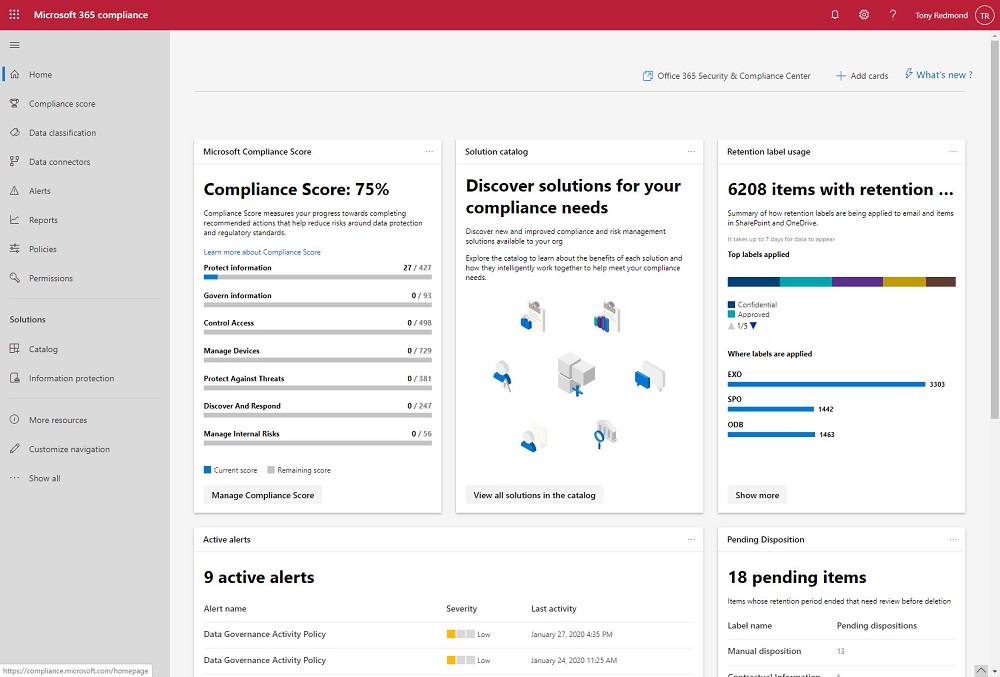
The Microsoft 365 Compliance and Security centers are roling out to Office 365 tenants where they’ll replace the old Security and Compliance Center over time. The new centers look fresher than the SCC, but looks can deceive and it’s much more important that the functionality exposed in the new portals work reliably all the time.
OWA now supports the automatic labeling of outbound messages with Office 365 Sensitivity Labels. The new feature uses Office 365 sensitive data types to detect content in messages that should be protected, and once detected, the message is stamped with a label before it passes through the Exchange Online transport service.
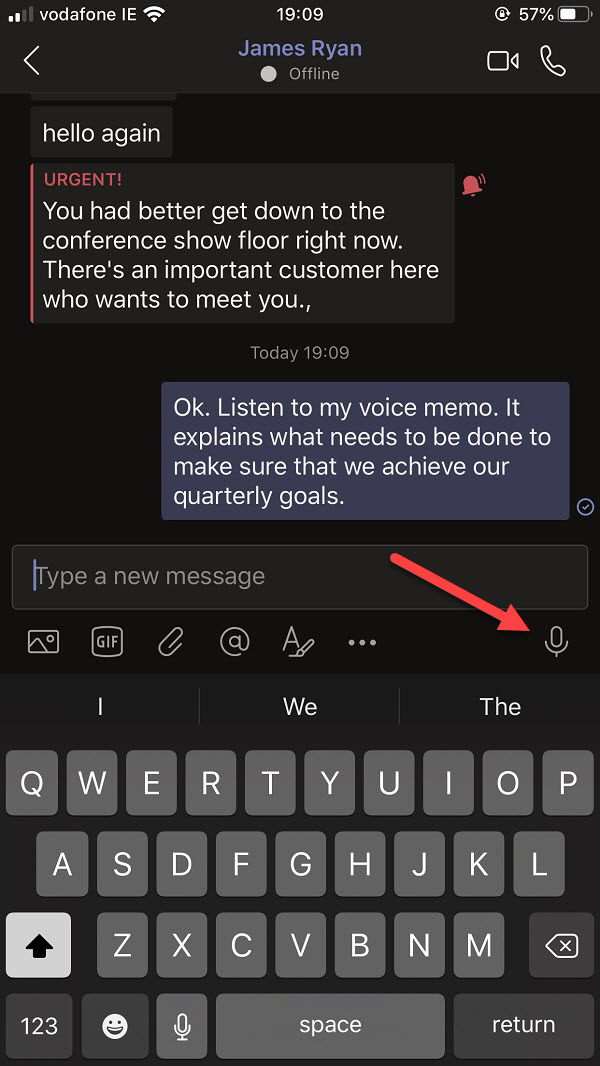
The Teams mobile clients allow users to record and send voice memos in personal and group chats. It’s nice functionality, but from a compliance standpoint some glaring weaknesses exist in the way that Office 365 captures compliance records for these memos. No voice recognition, no metadata, nothing to search for. It’s a compliance mess that Microsoft needs to clean up.
Exchange Online allows users to add personal retention tags to their maiboxes through OWA settings. Some organizations don’t like this, so they can deploy user role assignment policies to block the feature. It;s something that you could consider doing if you’re preparing to switchover to Office 365 retention policies to impose the same retention regime across multiple workloads.
Teams does a good job of storing compliance records in Exchange Online mailboxes so that the data is available for Office 365 eDiscovery. But the number of records can impact the mailbox quotas of frontline workers, especially if they send graphics in personal and group chats. Here’s some PowerShell to help discover how much mailbox quota is being absorbed by compliance records.
Microsoft launched the MailItemsAccessed audit event (to capture when email is opened) in January, reversed the roll-out in April, and now might restart sometime in Q3. It’s an odd situation that isn’t really explained by a statement from Microsoft. Are they going to charge extra for this audit event? Will they be analyzing the events? Or does Office 365 capture too many mail items accessed events daily?
A busy week included speaking engagements in Germany and Oslo. The Experts Live Norway event saw Tony talk about Office 365 data governance, a topic he thinks he knows well. You can grab a copy of the presentation he used in Oslo from this post.
Exchange Online supports inactive mailboxes as a way to keep mailbox data online after Office 365 accounts are removed. Inactive mailboxes are available as long as a hold exists on them. You can update mailbox properties to exclude all or some org-wide holds. If you exclude holds from a mailbox, you run the risk that Exchange will permanently remove the mailbox. If that’s what you want, all is well, but if it’s not, then you might not be so happy.
Office 365 supervision policies can now make use of artificial intelligence and machine learning to detect offensive language in email and Teams communications. The data model covers a wide range of problematic language, but only in English. You can go ahead and cheerfully continue to swear in French, German, and other languages with no danger of being detected by policy.
On May 7, Microsoft eventually fixed a truncation bug that affected group events (creation, add member, etc.) ingested into the Office 365 audit log. The fix took far too long coming and the overall response is certainly not Microsoft’s finest hour. Audit events, after all, are pretty important in compliance scenarios and it’s not good when those events are incomplete.
Sometimes Office 365 can be infuriating. My latest tribulation came in the form of missing retention labels, which disappeared from SharePoint Online without any reason for two weeks. Some labels returned due to auto-label policies, but any applied to documents manually had a vacation somewhere in the bowels of the services. It wasn’t a good experience.