The Copilot Retrieval API is a Microsoft Graph API that apps can use to search Microsoft 365 locations to find information to ground user prompts. Grounding means that the apps use the information found by Copilot to add context to the queries they submit to a generative AI engine for processing. Although I don’t have an immediate purpose for the API, it provides a nice insight into how grounding works.
Entra ID uses an eventually consistent multi-region database architecture. PowerShell code that fetches and updates Entra ID objects needs to interact with the database in the most efficient manner. This article illustrates some guidance from Microsoft engineering with examples from the Microsoft Graph PowerShell SDK. I’m sure your scripts already use these techniques, but if not, we have some helpful pointers.
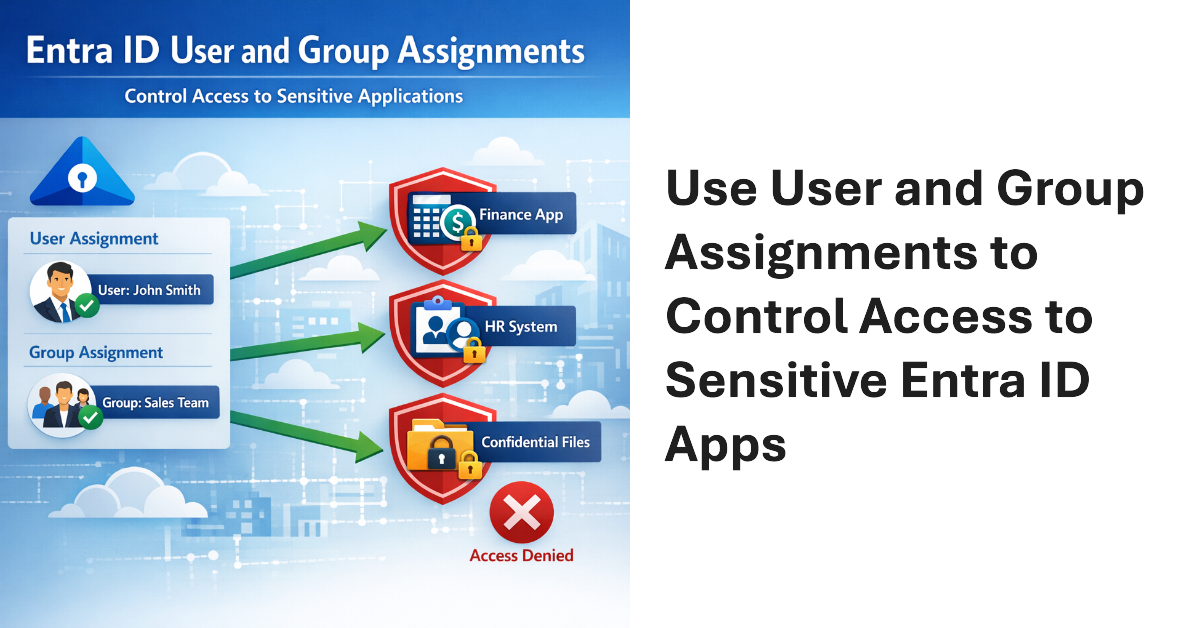
User and Group assignments can be added to Entra ID applications. Once assignments exist for an application, only assigned users can access that application. This method is a good way to secure access to applications that have consent to use high-profile permissions like Sites.FullControl.All or Mail.Read. Microsoft 365 tenants should consider how to use assignments to control user access to applications.
The Microsoft 365 admin center includes an option for administrators to send Copilot diagnostic logs on behalf of users to Microsoft for investigation. Sounds good, but the diagnostic logs are in plain text (JSON format) and the prompts and responses for Copilot user interactions can be viewed by administrators. That doesn’t seem like a good way to preserve anyone’s privacy. Vote for the feedback item to close this loophole.
The Microsoft 365 Connector for Claude allows Claude to access SharePoint and OneDrive files, emails, and Teams chats and meetings. The connector is now available to all users, including the free tier for Claude. Installing the connector creates two Entra ID enterprise apps (MCP server and client) and channels Graph requests to Microsoft 365 to fetch information for processing by Claude. Is that a good thing?
Microsoft plans to introduce flex routing to handle situations when demand exceeds capacity for Copilot processing in Europe. This could be an issue for Microsoft 365 tenants in the European Union or European Free Trade Association who want to be sure that their data is processed in Microsoft local datacenters and not sent to the U.S. or Australia when available capacity cannot meet the demand for “large language model inferencing”.
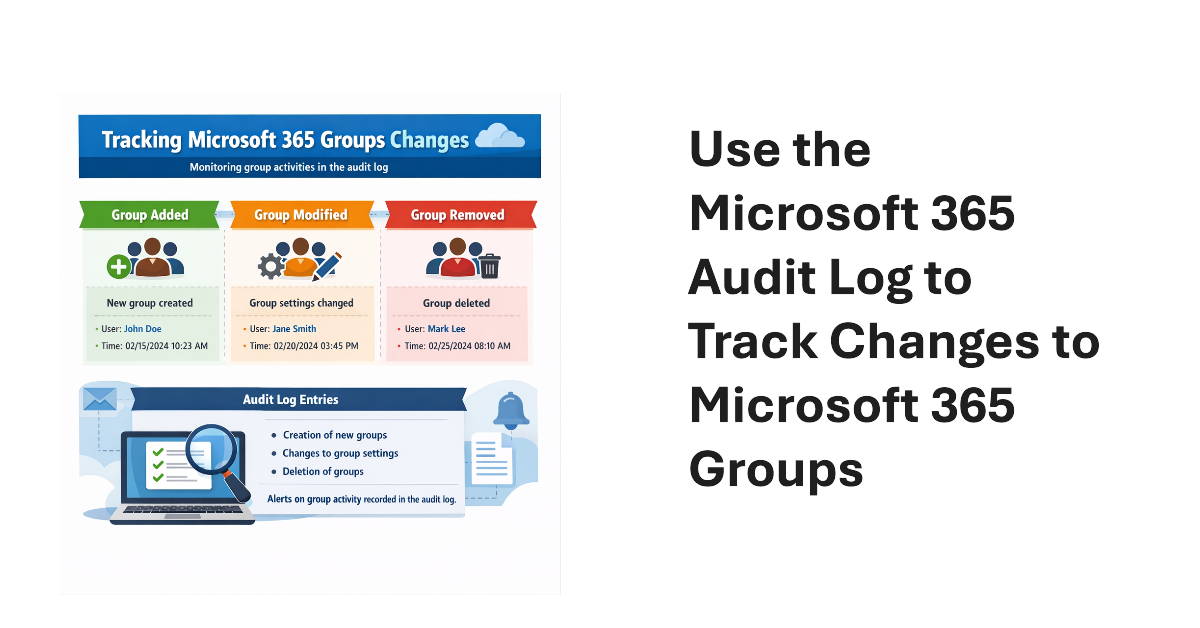
An old PowerShell script tracked changes to Office 365 Groups. The techniques from 2016 wouldn’t be used today because features like the unified audit log didn’t exist then. We show what’s possible now by creating a new version of a Microsoft 365 Groups Change Report script to track additions, deletions, and changes for Microsoft 365 groups in a tenant.
Viva Engage communities now support Purview container management labels (sensitivity labels that manage settings for groups, teams, communities, etc.). The update makes it possible to manage community settings like privacy through labels instead of settings applied to individual communities. Once communities have container management labels, you can manage the labels in the same way as when applied to Teams and Microsoft 365 groups.
This article discusses the use of restricted site creation for third-party Entra ID apps. The feature has an allow or deny list to identify apps that can create new SharePoint Online sites. Controlling the set of apps that can create new sites contributes to limiting site sprawl and makes sure that every site has a real function. First-party apps like Teams are unaffected.
Fresh from celebrating the 30th anniversary of Exchange Server, the Office 365 for IT Pros team is happy to release the 130th monthly update for the book (plus an update for the Automating Microsoft 365 with PowerShell eBook). Reflecting on 30 years of writing about the development of Exchange, Office 365, and Microsoft 365 reminds us about just how far we’ve come. It also reminds us that technology keeps on changing. On to update #131!
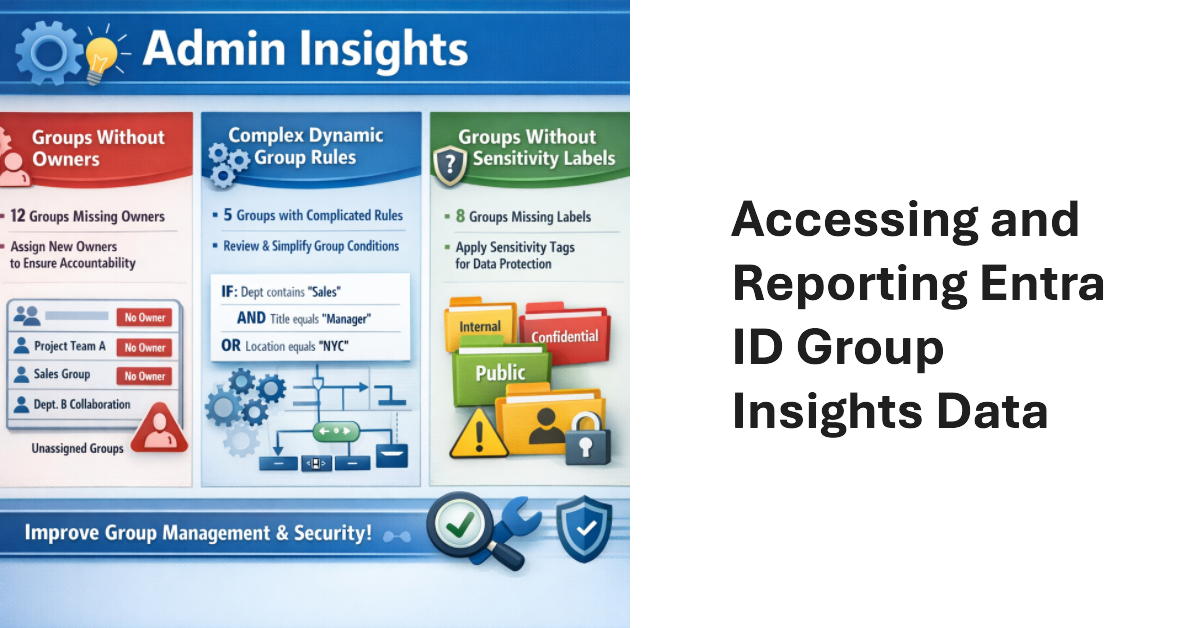
Entra ID Group Insights are a new preview feature in the Entra admin center. The lack of documentation is challenging, but it’s easy to understand what kind of insights Microsoft wants to deliver. Looking behind the scenes, we find the Graph endpoint for Group insights and can extract the data. That allows us to combine insights with other information to make them more interesting. All done with PowerShell.
Conditional access policies are very powerful. A beta feature appears to support time-limited blocks, but maybe the new feature is not needed because the same effect can be accomplished today through a mixture of conditional access policies, dynamic groups, and Azure Automation runbooks (or scheduled PowerShell scripts). Maybe that’s why Microsoft hasn’t released any documentation for the beta feature!
I’ve used a SharePoint alert to create an emailed daily digest of changes made to files in a document library for seven years. Microsoft plans to retire SharePoint Alerts in July 2026, and the race is on to find a replacement. Regretfully, neither Power Automate nor SharePoint Rules seem capable of generating an equivalent daily digest, perhaps because these solutions don’t handle the number of file versions created by AutoSave well.
Microsoft has announced details of a change to app permissions to restrict updates to sensitive message properties (like recipients) without consent for a new advanced mail access permission. If tenants have apps that interact with message properties, including apps developed by third parties, they should check whether the apps are updating sensitive properties. If so, the new permission must be assigned or the apps will stop working.
Microsoft disclosed that Entra ID login events were missing from Microsoft Defender for Cloud Applications for nine months — and waited more than three months after the fix to tell customers. Here’s why that matters and what you should do about it.
If installed into a MIcrosoft 365 tenant, ChatGPT Enterprise apps can access SharePoint Online files, Exchange Online email and calendar, and Teams chats, messages, and tasks. The Entra ID apps created by ChatGPT have the necessary permissions to access information accessible to the signed-in user. Microsoft 365 Copilot can access more information, but being able to process files, emails, calendar items, and chats and channel conversations delivers access to a lot of Work IQ.
Microsoft released the preview of the Entra ID Backup and Recovery solution to tenants on 19 March 2026. Although the software is functional in tenants, Microsoft didn’t make a big announcement. We’ve spent the last few days testing backup and recovery and put together the major points about the new solution, which is doubtless going to be welcomed by tenants if not by backup ISVs.
The April 2026 update for the Automating Microsoft 365 with PowerShell eBook is now available for subscribers to download. Refreshed EPUB and PDF files can be downloaded from Gumroad.com. The Kindle and paperback editions are also updated. This month we reflect on V2.36.1 of the Microsoft Graph PowerShell SDK and why so little has changed in this important component.
The Planner agent is now available to users with Microsoft 365 Copilot licenses and any Planner license. The purpose of the Planner agent is to help people understand the steps necessary to accomplish assigned tasks. Like any AI tool, the quality of the agent’s output depends on the precision and completeness of the instructions given for a task. But if you’re prepared to iterate, the agent might work for you.
Some Microsoft MVPs have expressed a strong opinion that Microsoft isn’t doing enough to develop and enhance the Microsoft Graph APIs across Microsoft 365. Problems include inconsistency in implementation, undocumented APIs, assembly clashes, missing coverage, and APIs that never come out of beta. It seems like Microsoft doesn’t dedicate sufficient attention to this important topic. What do you think?
Microsoft 365 E7 bundles Microsoft 365 E5, Microsoft 365 Copilot, the Entra Suite, and the new Agent 365 into a $99/user/month SKU. The big question is whether investing in Microsoft 365 E7 licenses make sense for tenants? Buying a big batch of licenses will simply throw money away unless those licenses can be used. Paul Robichaux debates the issues and suggests some advice about how to assess the need for E7.
Teams will soon block third-party recording bots from being able to create transcripts and generate AI-based summaries for Teams meetings. The problem is that these bots must export information for processing outside of a tenant, which creates all sorts of compliance issues. The new feature is part of base Teams and will be enabled in all tenants. You can disable it and allow bots if you want.
In December 2024, Microsoft introduced a control to block responses to sentiment-related prompts in Teams meeting chat. Now that block extends to every Teams user following a consolidation of the Teams meeting implementation of chat with Microsoft 365 Copilot. Basically, the block stops Copilot responding to prompts that look for opinions about emotions, judgement, or evaluations of other meeting participants. It’s a good thing.
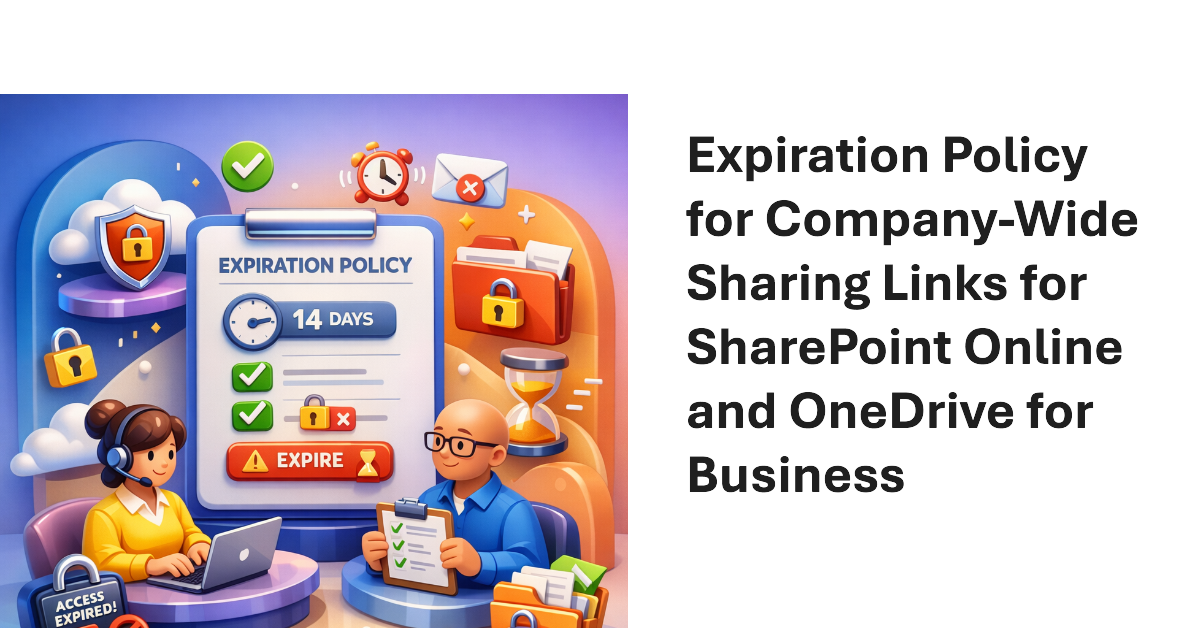
Company-wide sharing links allow any authenticated user account in a Microsoft 365 tenant to access a shared file or folder. New settings are available to create an expiration policy for company-wide sharing links, with different values supported for SharePoint Online and OneDrive for Business. The idea is to stop the potential for abuse of sharing links, including stale links that should not grant access to files and folders.
The Microsoft 365 Backup solution will soon be able to restore individual files and folders instead of complete sites. That’s a welcome upgrade to restore capabilities to cover situations like the inadvertent deletion of a file. It’s a wonder why Microsoft didn’t make more about this capability when they celebrated SharePoint’s 25th anniversary last week when they discussed departmental billing for Microsoft 365 Backup.
It’s easy to remove sensitivity labels from SharePoint Online files when only a few files are involved. Doing the same task at scale requires automation. In this article, we explain how to use the Microsoft Graph PowerShell SDK to find and remove sensitivity labels from files stored in SharePoint Online and OneDrive for Business.
Almost two years after it first previewed, Microsoft is making the High-Volume Email (HVE) solution generally available in March 2026. HVE runs on a pay-as-you-go basis, but Microsoft won’t start charging tenants for sending email until May 2026. Two months should be enough for people to decide if they want to use HVE for internal communications as it has no ability to send external email.
From July 2026. SharePoint Online and OneDrive for Business will use Entra B2B Collaboration (guest accounts) to control external access to shared files. This change has been coming since 2021, but it takes time for organizations to get their heads around changing the way to grant external access. It’s time to embrace guest accounts, and that means doing some work to manage guest accounts on an ongoing basis.
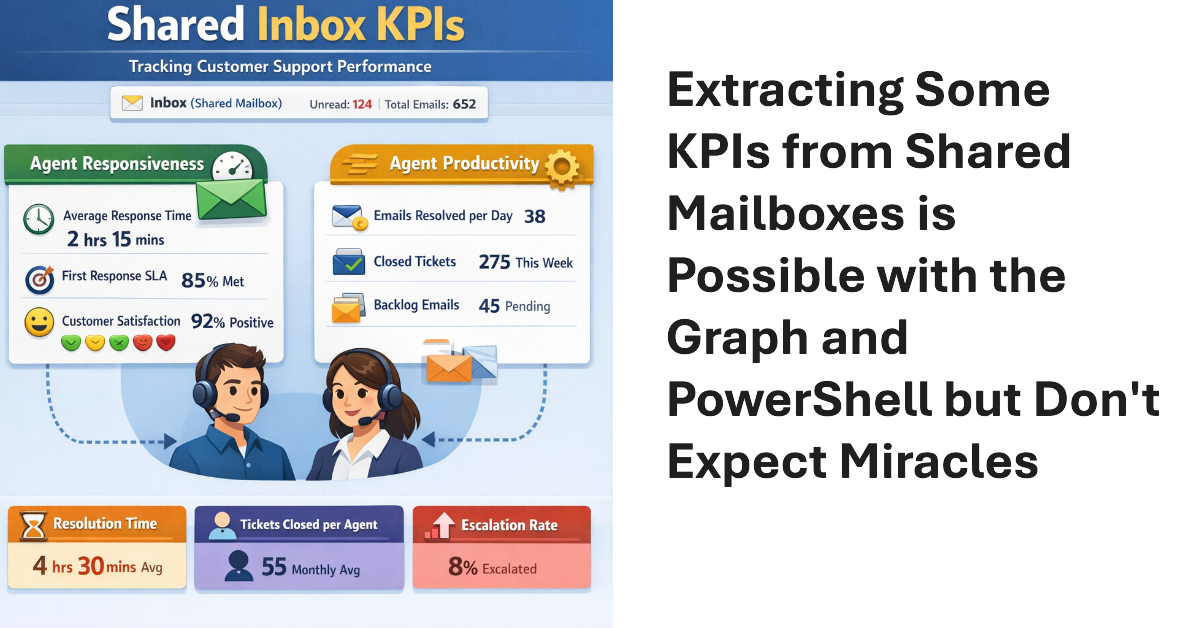
Shared mailboxes are not CRM systems. However, many Microsoft 365 tenants use shared mailboxes to handle customer queries and then want to measure KPIs such as agent responsiveness to customer queries or the number of queries handled per agent in a month. As explored in this article, it’s possible to use the Microsoft Graph to extract some KPI-like data from shared mailboxes.
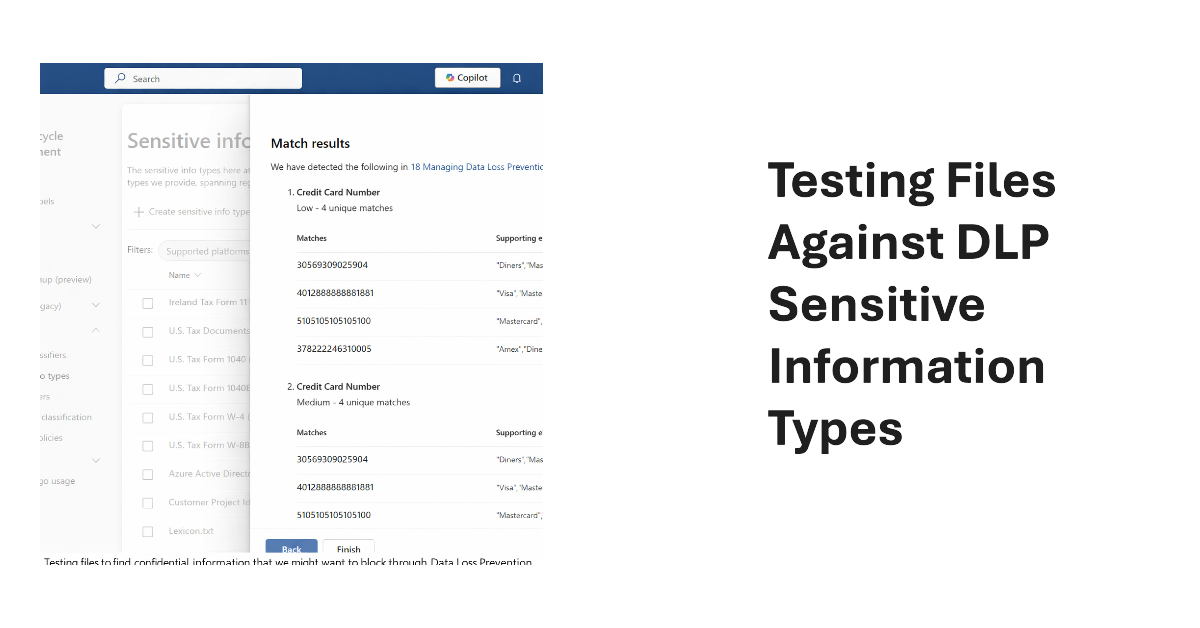
Sensitive Information types (SITs) are definitions of data like credit card numbers used by DLP rules to detect potential external sharing violations. Knowing what SIT to use in a DLP rule is often difficult, which is why the Purview developers have added a test option to allow tenants to test files against individual SITs or all SITs to see what happens.
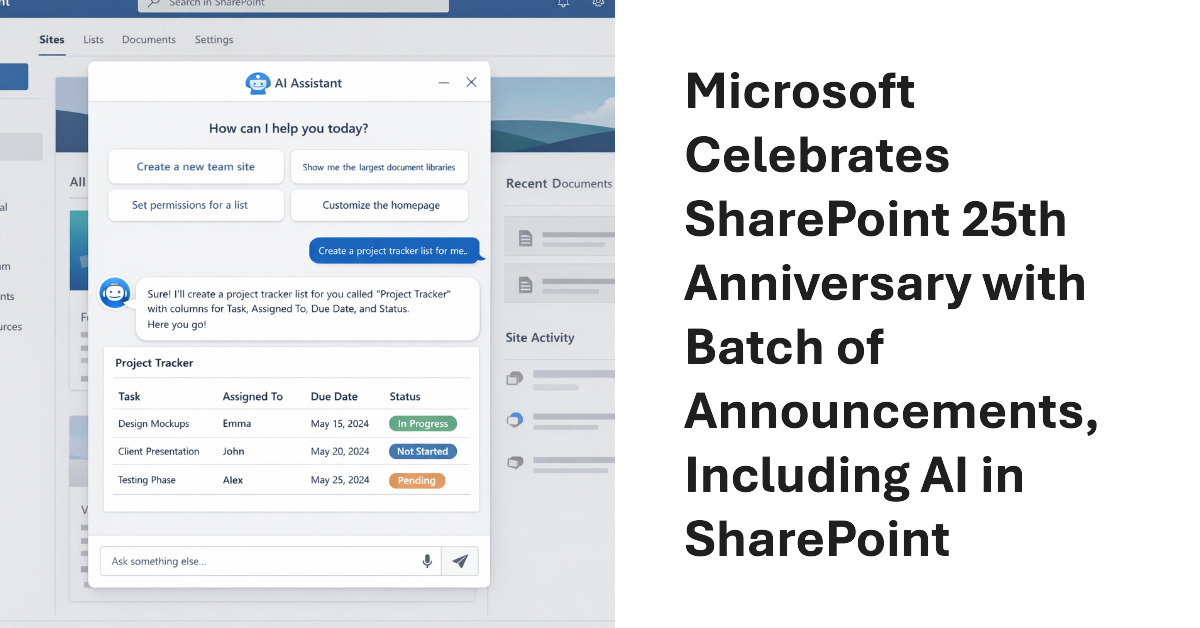
Microsoft celebrated the 25th anniversary of SharePoint with a batch of announcements, including AI in SharePoint, intended to help administrators to manage all aspects of SharePoint Online through natural language. Other interesting announcements included department-level payments for Microsoft 365 Backup and the renaming of the Connections app in Teams as the SharePoint app. Well, the last wasn’t that interesting…
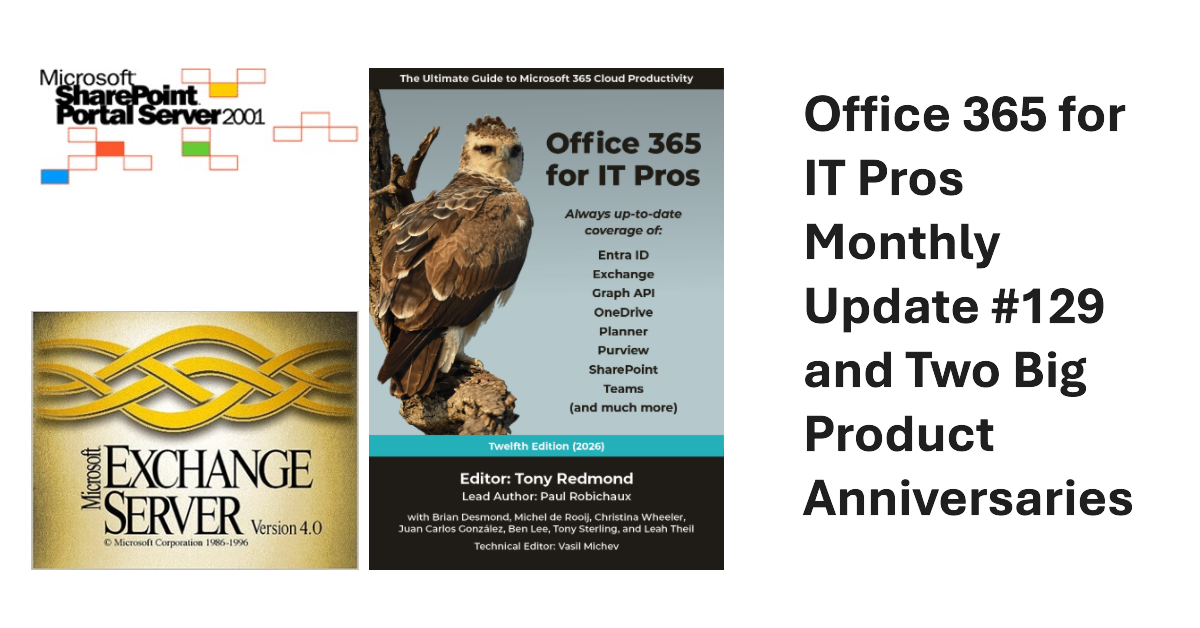
We’ve released monthly update #129 for the Office 365 for IT Pros eBook. Current subscribers can download the EPUB and PDF files from gumroad.com. This month we reflect on the 25th anniversary of the release of SharePoint Portal Server 2001 and the 30th anniversary of Exchange Server V4.0. Both servers have experienced great success online and on-premises. Long may they continue!
Microsoft has launched a redesigned user interface for the Planner app. The big news is the inclusion of task chat. Goals are also available, but only to people with a Microsoft 365 Copilot or Planner Premium licenses. Task Chat is a nice feature, and I am sure that it will be popular. UX redesigns often disappoint. At least this one offers new features.
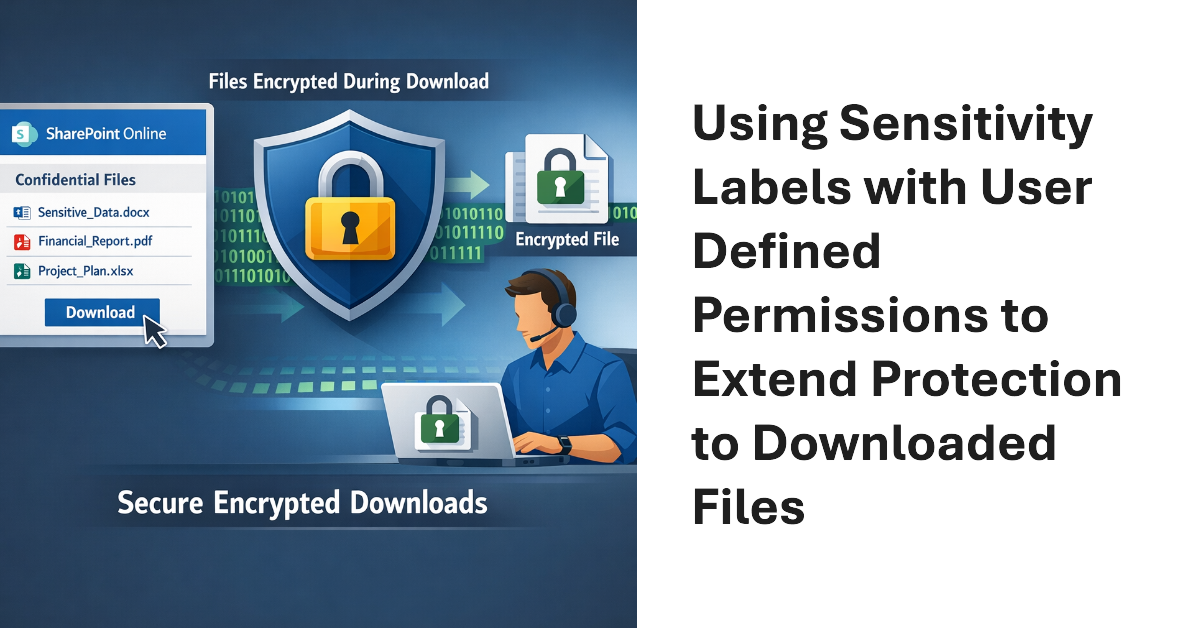
Sensitivity labels offer great protection against unauthorized access, but sometimes files that aren’t encrypted escape from a document library. SharePoint Online can now use sensitivity labels configured with user defined permissions (UDP) to extend protection to downloaded files. The magic works by configuring permissions on download based on the membership of the user who downloads a file.
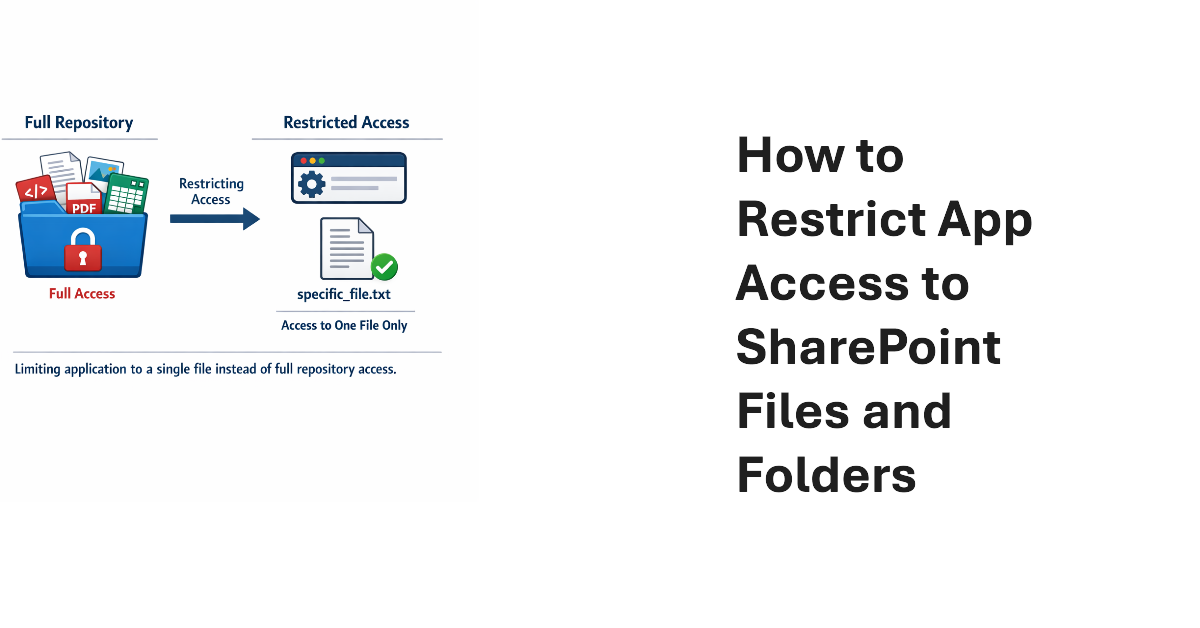
This article explains how to use scoped Graph permissions to restrict app access to lists and list items in SharePoint Online and OneDrive for Business sites. It’s a follow-up to other articles covering how to restrict app access to SharePoint Online sites and files. Scoping app access to specific objects is important because otherwise apps can access everything in SharePoint Online, and that isn’t good.
Microsoft has enhanced the DLP policy for Copilot to cover Office files held in any storage location instead of only Microsoft 365 locations like SharePoint Online and OneDrive for Business. The change is made in the Office augmentation loop, a little-known internal component that coordinates use of connected experiences by apps. Extending the DLP policy to cover all locations makes perfect sense.
Update #21 for the Automating Microsoft 365 with PowerShell eBook is now available for current subscribers to download from Gumroad.com. Refreshed PDF and EPUB files are available and the paperback version available from Amazon.com is also updated. Automating Microsoft 365 with PowerShell is packed with practical ready-to-use examples of working with apps, sites, mailboxes, teams, plans, and other data. Every Microsoft 365 administrator should have this book!
Microsoft would very much like Microsoft 365 tenants to use Copilot instead of ChatGPT. A recent comparison between Copilot and ChatGPT outlines some areas that Microsoft thinks are important when deciding which AI tool to use. Microsoft has a point because Copilot is embedded into Microsoft 365 whereas ChatGPT is more of an add-on. The competition for hearts and minds is very intense in the AI space.
Dev Proxy is a Microsoft tool built to help developers figure out the most effective way of using Microsoft Graph API requests. On the surface, Dev Proxy doesn’t seem like a tool that would interest people who use the Microsoft Graph PowerShell SDK to write scripts for Microsoft 365. But all tools have some use, and Dev Proxy can help.
Scoped permissions grant apps granular access to files and folders in SharePoint Online and OneDrive for Business sites using the Files.SelectedOperations.Selected Graph permission. The permission allows apps to access specific files or all the files in a folder. It’s a great way to make sure that apps don’t have unfettered access to confidential documents. Not that any app would try to have that kind of access…