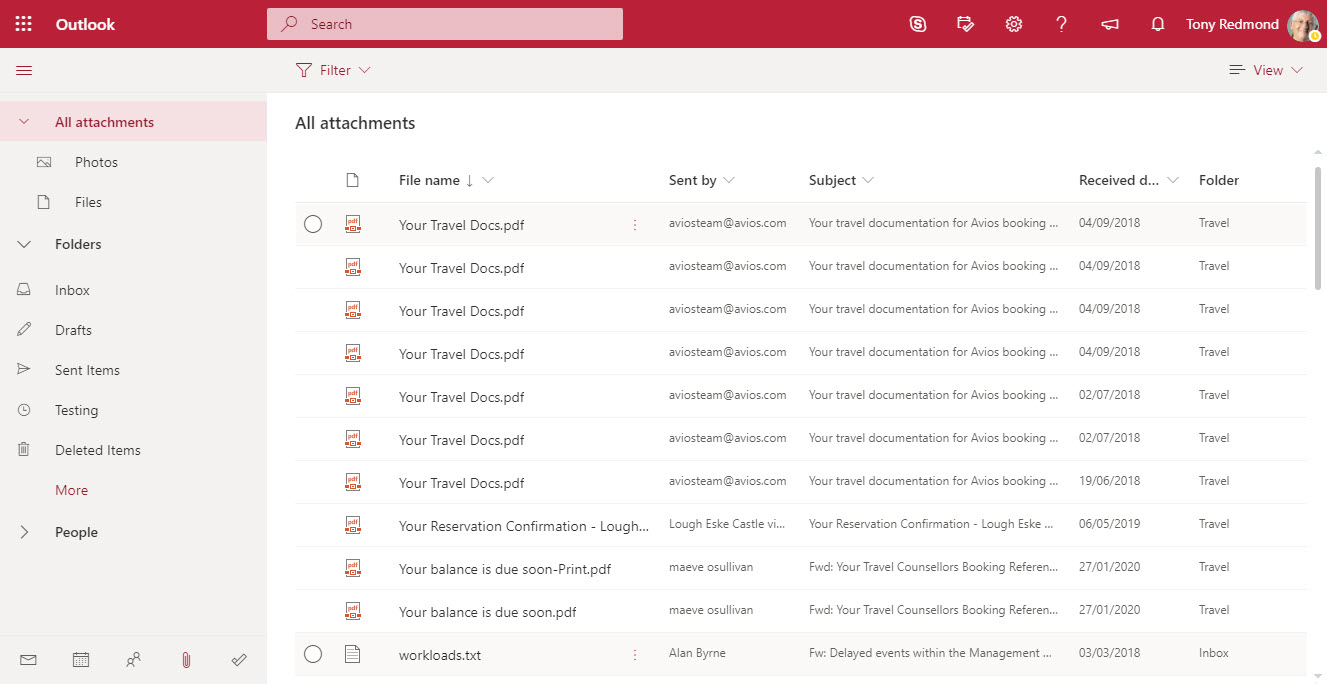
OWA now includes Files in its “module switcher”). The new module allows fast access to attachments stored in any folder in an Exchange Online mailbox. It’s a neat feature that will please many people simply because it makes finding often-elusive attachments just that bit easier.
Not many Office 365 users choose OWA as their mobile client, but those who do will soon be forced to use the new OWA because Microsoft is removing the toggle to allow people to switch between the old and new versions in February, just like they did for workstation versions last July. The new OWA is a fine client, but its usefulness on mobile browsers is not as good as the functionality offered in Mobile Outlook, which continues to be our choice as the best mobile Office 365 email client.
Exchange Online now supports a custom recipient limit for mailboxes of between 1 and 1000. The limit controls the maximum number of recipients a mailbox can add to a message. Think of the fun you could have by setting the recipient limit on manager mailboxes to something small, like 6….
In November, Microsoft set a 1TB limit for Exchange Online auto-expanding archive mailboxes. Now they’ve retreated and the latest service description says nothing about a limit. The two changes in the service featured little or no customer communications and a total lack of any supporting material, like administrative controls to help manage archive mailboxes approaching the limit. While a limit has gone for now, it will be back.
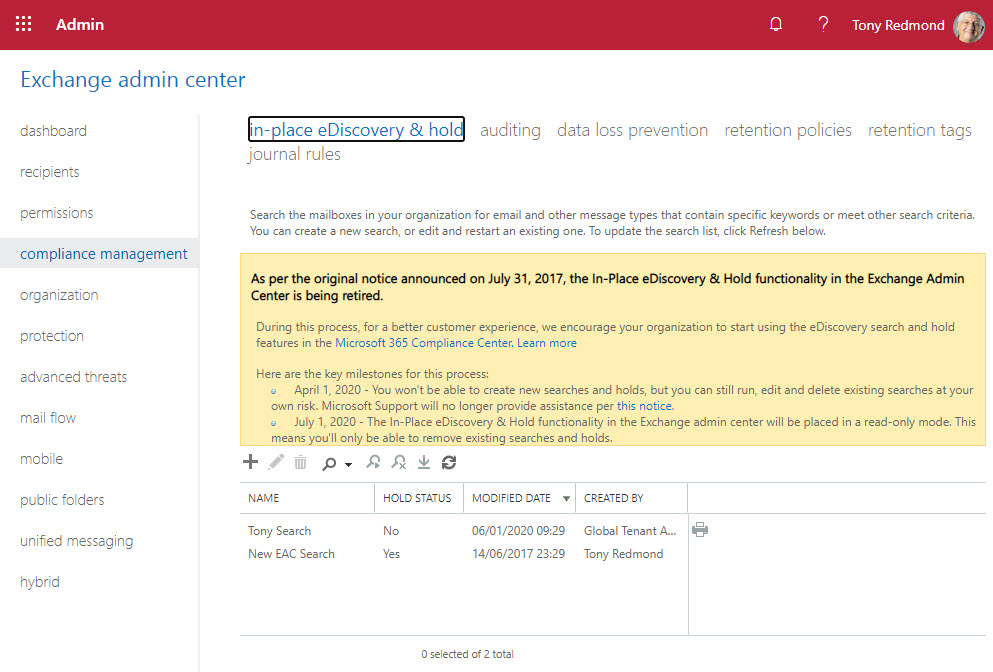
Microsoft announced the retirement of legacy eDiscovery tools from Office 365. The Exchange Online in-place holds and eDiscovery tool, Office 365 Advanced eDiscovery 1, and the Search-Mailbox cmdlet are being retired. All will be gone by mid-2020. It’s a pity to see the Search-Mailbox cmdlet being removed, but time and progress make this kind of thing inevitable.
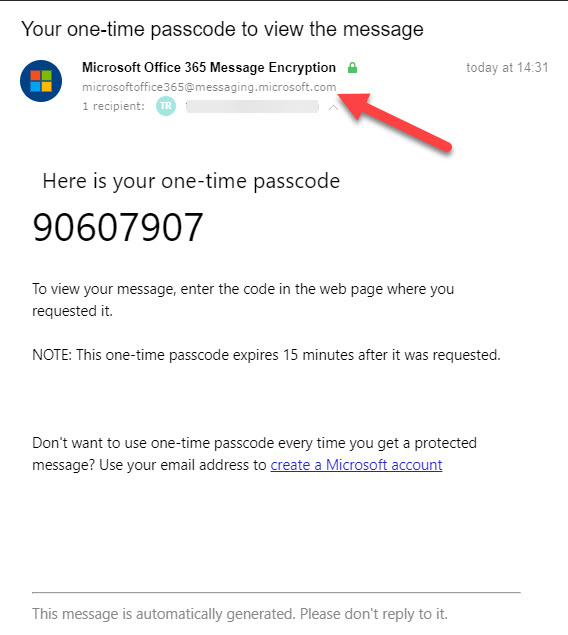
Microsoft is releasing some updates to Office 365 Message Encryption (OME) in January. The detail in the announcement wasn’t great, so we plunged in to find out what’s happening. THe bottom line is that OME will use tenant domains to send email so that anti-spam filters will consider the messages to be authentic.
Exchange Online transport rules can block outbound email stamped with selected Office 365 Sensitivity Labels to make sure that confidential material doesn’t leave organizations. The transport rule is very easy to construct with the only complication being the need to discover the GUID of the sensitivity label you want to block. Fortunately, PowerShell gives us an easy way to find a label’s GUID.
Outlook for iOS finally supports the Do Not Disturb feature to suppress notifications for new email, something that Outlook for Android has been able to do for 18 months. iOS and Android are obviously different ecosystems, so the delay might have been caused by problems dealing with the Apple notification service. In any case, you can now snooze some or all of your email accounts. In other news, some of the more interesting features available to U.S. email accounts are still not available outside the reach of Cortana.
Multiple PowerShell modules are available to Office 365 administrators to automate common processes. In this case, we want to send a welcome message to new accounts. Three PowerShell modules are available, but what’s the best in terms of performance and ease of use? There’s only one answer and that’s Exchange Online.
The Microsoft Immersive Reader exists to make messages more readable for those who need a little help. It’s built into Office apps like Teams and OWA. Most people don’t know this or don’t need to use the reader, but those who do need support to access and understand text will find the Immersive Reader very helpful.
OWA now supports the automatic labeling of outbound messages with Office 365 Sensitivity Labels. The new feature uses Office 365 sensitive data types to detect content in messages that should be protected, and once detected, the message is stamped with a label before it passes through the Exchange Online transport service.
ORCA is a project to help Office 365 tenant administrators validate their anti-spam and anti-malware settings against recommendations from Microsoft. ORCA is installed as a PowerShell module with just one cmdlet. After running Get-ORCAReport, you’ll have a report containing recommendations and observations about your configuration.
Nine new REST-based PowerShell cmdlets are available for Exchange Online. They offer the prospect of better performance and reliability. Here are the code samples we used to test the new cmdlets for a theater session delivered at the Microsoft Ignite 2019 conference. Anyone wanting to explore the new cmdlets can use these examples to get going.
At the Ignite 2019 conference in Orlando, Microsoft announced that Office 365 Groups will soon support sensitivity labels, but only to mark group containers with levels of sensitivity. The actual content of the containers, like the messages in Outlook Groups or Teams, will remain unaffected by the labels. For now.
In a surprise development, Microsoft reversed course for Exchange Online auto-expanding archives and imposed a 1TB limit. The promise of a bottomless archive that continually expanded to cope with user data is removed. Although it’s reasonable for Microsoft to restrict the consumption of resources, suddenly implementing a limit is not, especially when you don’t communicate with customers.
OWA now supports Office 365 Sensitivity Labels, which means that users can apply labels to mark and/or protect messages with encryption just like they can with Outlook. The update adds to the ways that sensitivity labels can be applied to Office 365 content, with the next step being to achieve the same support for the other online Office apps.
Some Exchange Online mailboxes are quite small (2 GB for frontline users). Tenant administrators might want to monitor mailbox usage to make sure that quotas aren’t unexpectedly exhausted. This post explains how to use a PowerShell script to calculate the percentage of mailbox quota used and highlight the problem if a threshold is passed.
The Office 365 E5 plan includes Advanced Threat Protection (ATP), which builds on the anti-malware capabilities of Exchange Online Protection. ATP the includes Safe Attachments and Safe Links features, both of which can delay email delivery. I don’t notice the delay but others do. In any case, the more protection you have against malware, the better.
Microsoft has announced that basic authentication for multiple email connection protocols won’t be supported after October 13, 2020. You won’t be able to connect with EWS, EAS, IMAP4, POP3, or Remote PowerShell unless you use modern authentication. There’s just over a year to prepare, but there’s some work to be done.
Microsoft is now rolling out MyAnalytics access to Office 365 accounts with an Exchange Online license.The first sign that anyone gets is when they receive one of MyAnalytics’s well-intended messages to help them organize their work life smarter. Funnily enough, some people don’t like the idea of Office 365 analyzing and reporting their work habits, which is why you might need to disable MyAnalytics for some mailboxes.
Microsoft has confirmed that disconnected Exchange Online mailboxes are not included in the sources scanned by Office 365 content searches, thus clearing up some misunderstandings that might have existed in the field. The bottom line is that if you want to search mailboxes that don’t belong to accounts, you should use inactive mailboxes.
Exchange Online allows users to add personal retention tags to their maiboxes through OWA settings. Some organizations don’t like this, so they can deploy user role assignment policies to block the feature. It;s something that you could consider doing if you’re preparing to switchover to Office 365 retention policies to impose the same retention regime across multiple workloads.
Deploying new features to a massive 100-million plus user community takes a lot of planning and careful management. Outlook Mobile caters for both consumer and commercial users, and different methods are used to deliver new features to the two groups. Sometimes this means that different users in the same tenant can’t access a new feature even if they have the right software.
Outlook mobile users now have shared mailbox support in both iOS and Android platforms. The work to upgrade the backend service is also progressing and is past 50% rollout. And dark mode is coming too. It’s available in beta today to Testflight users (only for iOS), and it’s also been enabled for some users who run the latest version of the clients.
The Outlook Places service is used by Outlook clients to present metadata about meeting locations to users. Currently, OWA is the only client that consumes the service. You can update location metadata with details to make it easier for users to select the right location for their meeting, including geocoordinates that can be used to display map directions to the location.
Outlook people favorites give Exchange Online users fast access to their most important email correspondents. OWA has the best implementation but the feature is also available in Outlook mobile. As usual, Outlook desktop lags. It’s a small feature that could turn out to be very important to some users. Office 365 is full of such examples.
Outlook for Office 365 (the click to run version) now supports the Office Black theme. Preferring to use dark Outlook is very much a personal choice. I’m not convinced that I like it, even if you can force the message reading pane to be in light mode.
Outlook 2013 introduced the concept of hybrid mode (sometimes called Exchange Fast Access) to allow clients configured in cached Exchange mode to fetch data direct from the server when possible. The mode works well, except when you’re connected on a poor network as the attempts to fetch data from the server might cause Outlook to hang. A registry setting gives a way to force Outlook to operate in classic cached mode and use the OST exclusively when it needs data.
Microsoft has announced that the AdditionalStorageProvidersAvailable setting in OWA mailbox policies will now control access to both first-party and third-party storage providers. The new setting is now available and becomes active in August. Before then, you might want to adjust some of your OWA mailbox policies.
A question about how best to set auto-replies for Exchange Online shared mailboxes to respond to messages arriving during a public holiday gives another chance for PowerShell to show how useful it is. You could do the work with Flow, but PowerShell is more flexible and capable when dealing with multiple shared mailboxes.
Following a configuration change, the Exchange Online Focused Inbox ran into a problem on July 24 and delivered all messages to the “Other” view. This caused problems for users who didn’t receive notifications of new mail. Software can have bugs, but configuration changes should be tested before getting to production.
Microsoft dropped support for the ExMerge tool in Exchange 2007. An ISV has taken the initiative to create a modern version of the tool, called Super ExMerge. The utility supports both Exchange on-premises and Exchange Online.
Microsoft has announced that the switchover to the new OWA interface will start on July 22 when Office 365 tenants in targeted release will lose the chance to toggle back and forth between the two interfaces. By the end of September, everyone will use the new OWA. Let’s hope that Microsoft has fixed all the functionality gaps by then.
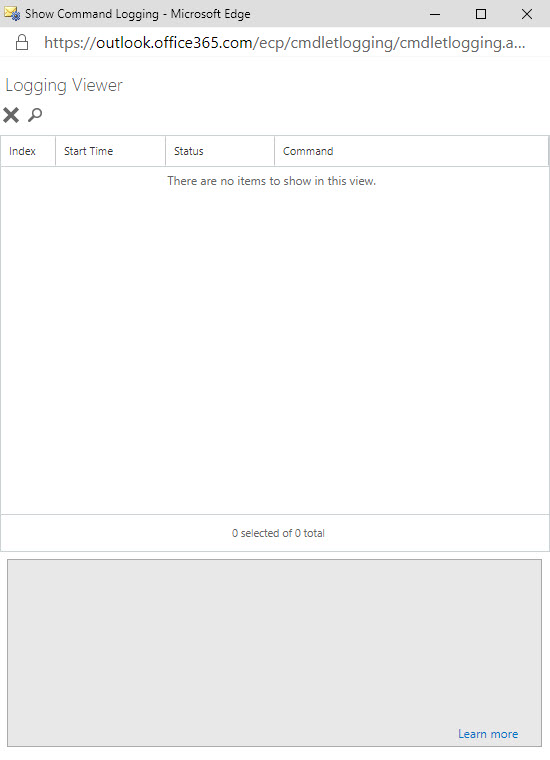
The ability to see the PowerShell commands executed by Exchange administrative centers has existed since Exchange 2007. Now something has changed in Exchange Online and the command log is blank. It’s sad because many administrators learned to use PowerShell by examining how Microsoft used it to manage Exchange. Let’s hope that Microsoft fixes this bug soon.
Microsoft launched the MailItemsAccessed audit event (to capture when email is opened) in January, reversed the roll-out in April, and now might restart sometime in Q3. It’s an odd situation that isn’t really explained by a statement from Microsoft. Are they going to charge extra for this audit event? Will they be analyzing the events? Or does Office 365 capture too many mail items accessed events daily?
Removing Office 365 accounts is easily done through the Admin Center. You can also restore deleted accounts within 30 days, but what if you want to remove accounts in such a way that they can’t be restored? The answer is that it can be done using a two-stage process. And if the mailboxes belonging to those accounts are on hold, they are kept as inactive mailboxes.
Microsoft has announced that it will deploy the ability to add shared mailboxes to Outlook Mobile by the end of July. But if you want to see the feature early, you can join the Testflight program and install the beta version of Outlook mobile. Using Outlook for iOS with Testflight also forces the upgrade of your Office 365 tenant to the Microsoft Sync Technology.
Microsoft has announced that Outlook Mobile (iOS and Android) will include support for Exchange Online shared mailboxes “in the next several weeks,” which probably means early July 2019. The update comes as good news for many people who have been forced to use an IMAP4-based workaround to access shared mailboxes. Microsoft is also making some other changes to improve the Files view and calendar sync in Outlook mobile.
Microsoft has implemented a new synchronization mechanism in Outlook ProPlus to deal more efficiently with shared folders. The new approach increases the limit from 500 to 5,000 folders and is a more elegant and precise solution. Users who manage other peoples’ mailboxes will appreciate the change after they install build 11629.20196 or later.
The new version of OWA boasts new abilities for owners to manage Office 365 Groups. The new UI is pretty slick and a welcome upgrade to the previous capabilities. You’ll still need to revert to PowerShell to manage some aspects of Office 365 Groups, but not as many times as you used to.